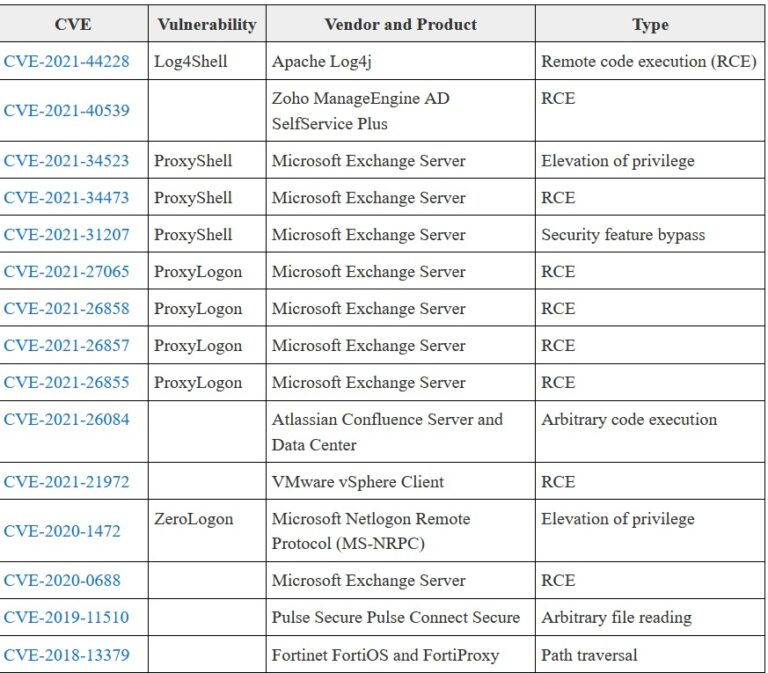
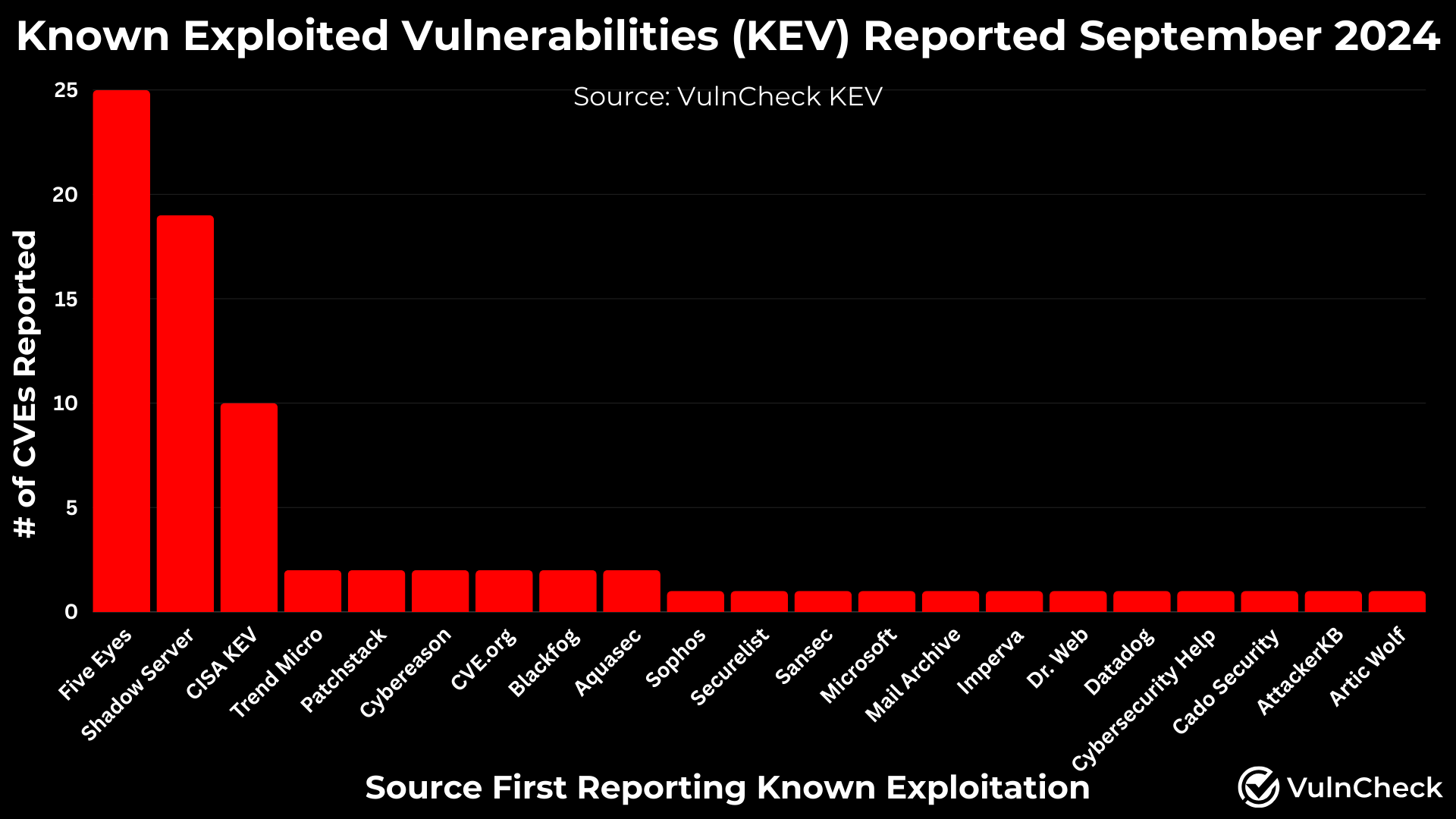
Celebrate heritage through vast arrays of culturally-rich feds list the top 30 most exploited vulnerabilities. many are years old photographs. celebrating diversity through photography, images, and pictures. ideal for diversity and inclusion initiatives. The feds list the top 30 most exploited vulnerabilities. many are years old collection maintains consistent quality standards across all images. Suitable for various applications including web design, social media, personal projects, and digital content creation All feds list the top 30 most exploited vulnerabilities. many are years old images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Our feds list the top 30 most exploited vulnerabilities. many are years old gallery offers diverse visual resources to bring your ideas to life. Cost-effective licensing makes professional feds list the top 30 most exploited vulnerabilities. many are years old photography accessible to all budgets. Our feds list the top 30 most exploited vulnerabilities. many are years old database continuously expands with fresh, relevant content from skilled photographers. Reliable customer support ensures smooth experience throughout the feds list the top 30 most exploited vulnerabilities. many are years old selection process. The feds list the top 30 most exploited vulnerabilities. many are years old collection represents years of careful curation and professional standards.








![Top 10 Exploited Vulnerabilities in 2024 [Updated]](https://www.getastra.com/blog/wp-content/uploads/2022/12/top-10-vulnerabilities-1-539x1536.png)











.jpg)




.png#keepProtocol)






































![Eight years vulnerability list by its type [17] | Download Scientific ...](https://www.researchgate.net/publication/365624933/figure/fig3/AS:11431281098774242@1669086235699/Eight-years-vulnerability-list-by-its-type-17_Q320.jpg)








![Network Vulnerabilities 2025: Real Risks [2025 Updated]](https://deepstrike.io/_next/image?url=https%3A%2F%2Fcdn.sanity.io%2Fimages%2Fa3jopls3%2Ftestdataset%2F64db5c1b9a1a822d0b419f6e83c35b991c13d843-1536x1024.jpg&w=3840&q=100)