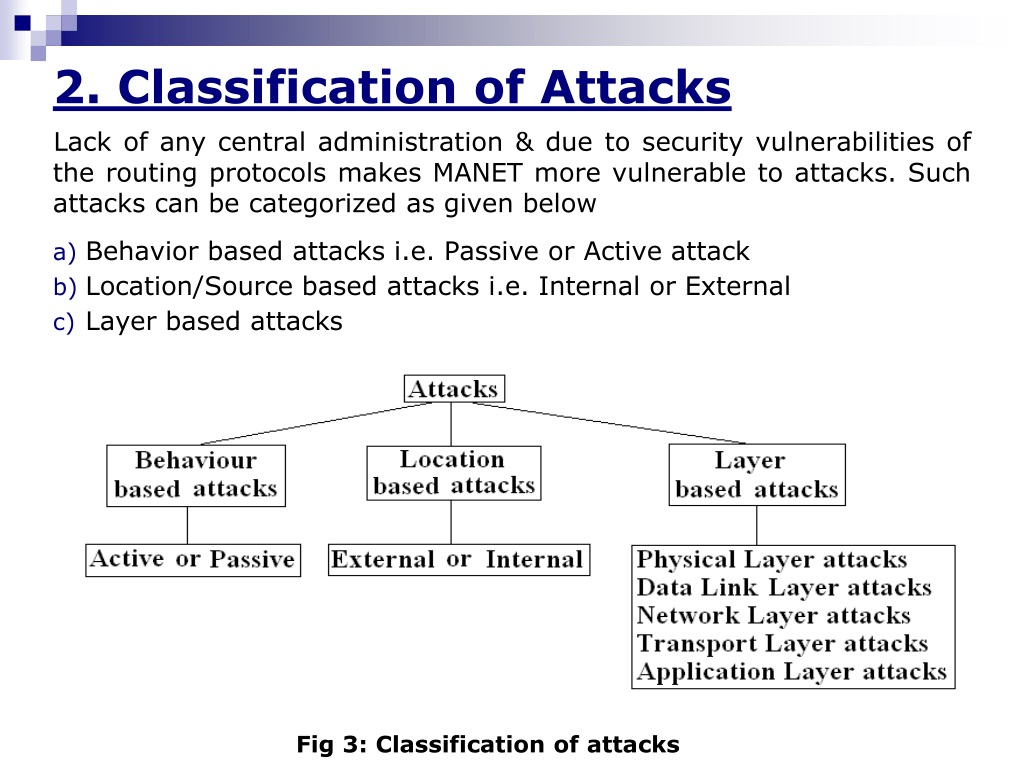
Drive success with our remarkable business attack classification by security flaw [2]. | download scientific diagram collection of countless professional images. strategically presenting photography, images, and pictures. perfect for corporate communications and marketing. Our attack classification by security flaw [2]. | download scientific diagram collection features high-quality images with excellent detail and clarity. Suitable for various applications including web design, social media, personal projects, and digital content creation All attack classification by security flaw [2]. | download scientific diagram images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Explore the versatility of our attack classification by security flaw [2]. | download scientific diagram collection for various creative and professional projects. The attack classification by security flaw [2]. | download scientific diagram collection represents years of careful curation and professional standards. Instant download capabilities enable immediate access to chosen attack classification by security flaw [2]. | download scientific diagram images. Advanced search capabilities make finding the perfect attack classification by security flaw [2]. | download scientific diagram image effortless and efficient. Time-saving browsing features help users locate ideal attack classification by security flaw [2]. | download scientific diagram images quickly. The attack classification by security flaw [2]. | download scientific diagram archive serves professionals, educators, and creatives across diverse industries.
![Attack classification by security flaw [2]. | Download Scientific Diagram image.](https://www.researchgate.net/publication/324167240/figure/download/fig1/AS:611173745569793@1522726584467/Attack-classification-by-security-flaw-2.png)





![Classification of Web Attacks [5]. | Download Scientific Diagram](https://www.researchgate.net/publication/348438167/figure/fig1/AS:979594215698433@1610564869774/Classification-of-Web-Attacks-5.png)

![Taxonomy of attacks. Source Preeti Mishra [4] | Download Scientific Diagram](https://www.researchgate.net/profile/Ida-Seraphim/publication/352635074/figure/fig2/AS:1055924257050624@1628763369168/Taxonomy-of-attacks-Source-Preeti-Mishra-4.png)















![Classification of Cyber-attack [11,12]. | Download Scientific Diagram](https://www.researchgate.net/publication/365042621/figure/fig2/AS:11431281094496206@1667483816394/Classification-of-Cyber-attack-11-12.png)









![Classification of Security attacks [22] | Download Scientific Diagram](https://www.researchgate.net/profile/Piyush-Shukla/publication/298803170/figure/fig1/AS:349324950163482@1460296966756/Classification-of-Security-attacks-22_Q640.jpg)
![Attack classification by security flaw [2]. | Download Scientific Diagram](https://www.researchgate.net/publication/324167240/figure/fig1/AS:611173745569793@1522726584467/Attack-classification-by-security-flaw-2.png)




![Classification attack [13] | Download Scientific Diagram](https://www.researchgate.net/publication/347756696/figure/fig2/AS:1106746865135616@1640880423267/Classification-attack-13.png)



![IoT security attacks classification Source: [25] | Download Scientific ...](https://www.researchgate.net/profile/Francesco-Bertolotti/publication/359527087/figure/fig2/AS:11431281122675005@1677497549466/IoT-security-attacks-classification-Source-25_Q320.jpg)


![Classification of Security attacks [22] | Download Scientific Diagram](https://www.researchgate.net/profile/Piyush_Shukla14/publication/298803170/figure/download/fig1/AS:349324950163482@1460296966756/Classification-of-Security-attacks-22.png)
![Classification of Cyber-attack [11,12]. | Download Scientific Diagram](https://www.researchgate.net/publication/365042621/figure/fig2/AS:11431281094496206@1667483816394/Classification-of-Cyber-attack-11-12_Q640.jpg)






![Attack classification by security flaw [2]. | Download Scientific Diagram](https://www.researchgate.net/publication/324167240/figure/fig1/AS:611173745569793@1522726584467/Attack-classification-by-security-flaw-2_Q640.jpg)


![Howard's attack taxonomy [9]. Daniel Lough presented a classification ...](https://www.researchgate.net/publication/324167240/figure/fig2/AS:611173745582081@1522726584527/Classification-designed-for-Denial-Of-Service-attacks-6_Q640.jpg)















![Classification of Attacks on Embedded Systems [11] | Download ...](https://www.researchgate.net/profile/Septafiansyah-Dwi-Putra/publication/315914993/figure/fig1/AS:751109085872129@1556089769619/Classification-of-Attacks-on-Embedded-Systems-11_Q320.jpg)



.jpg)