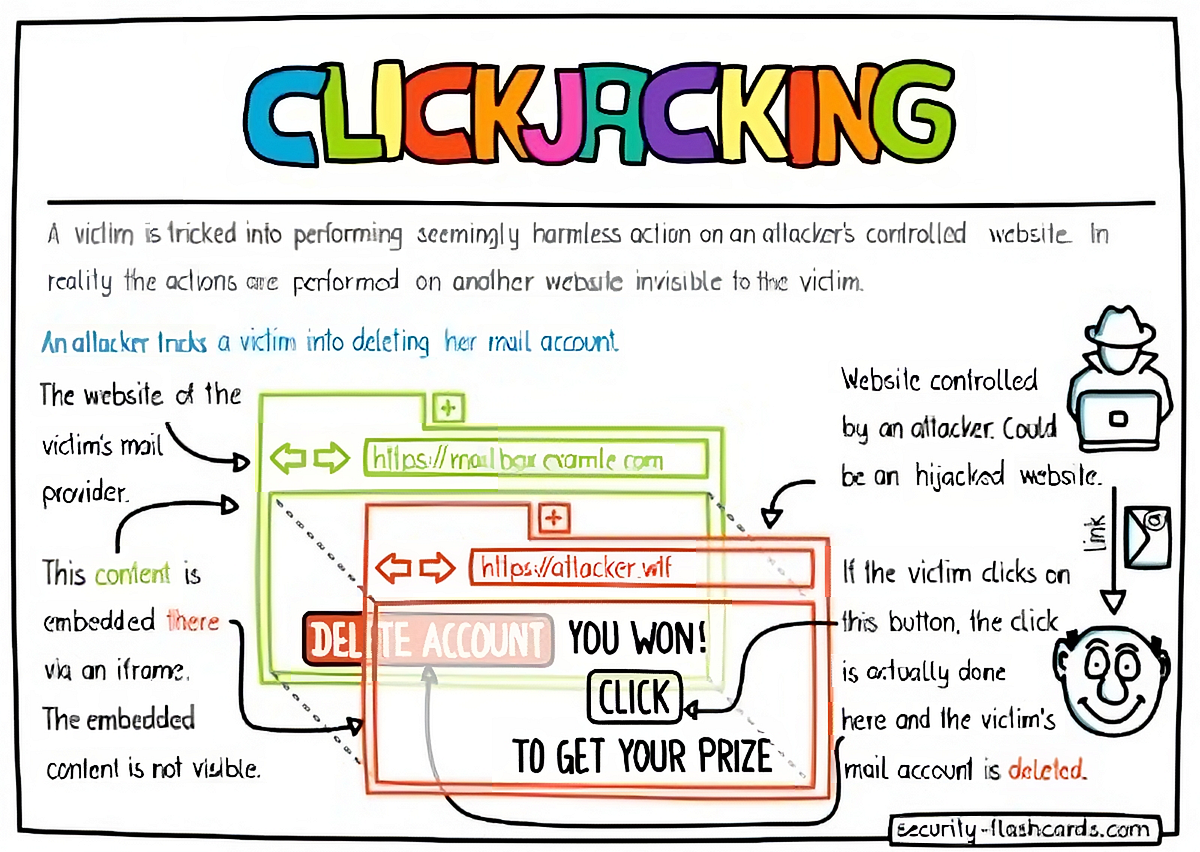
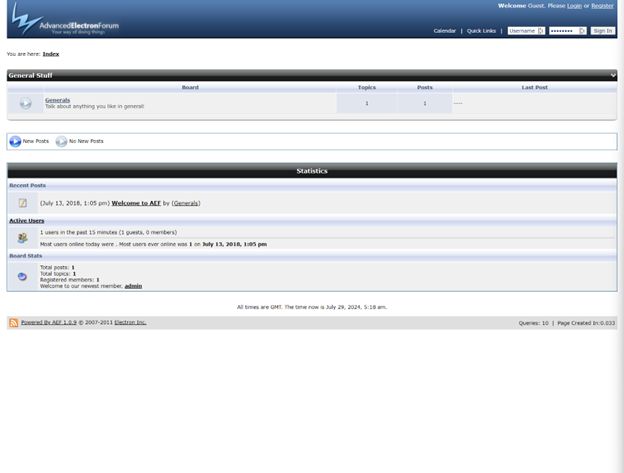
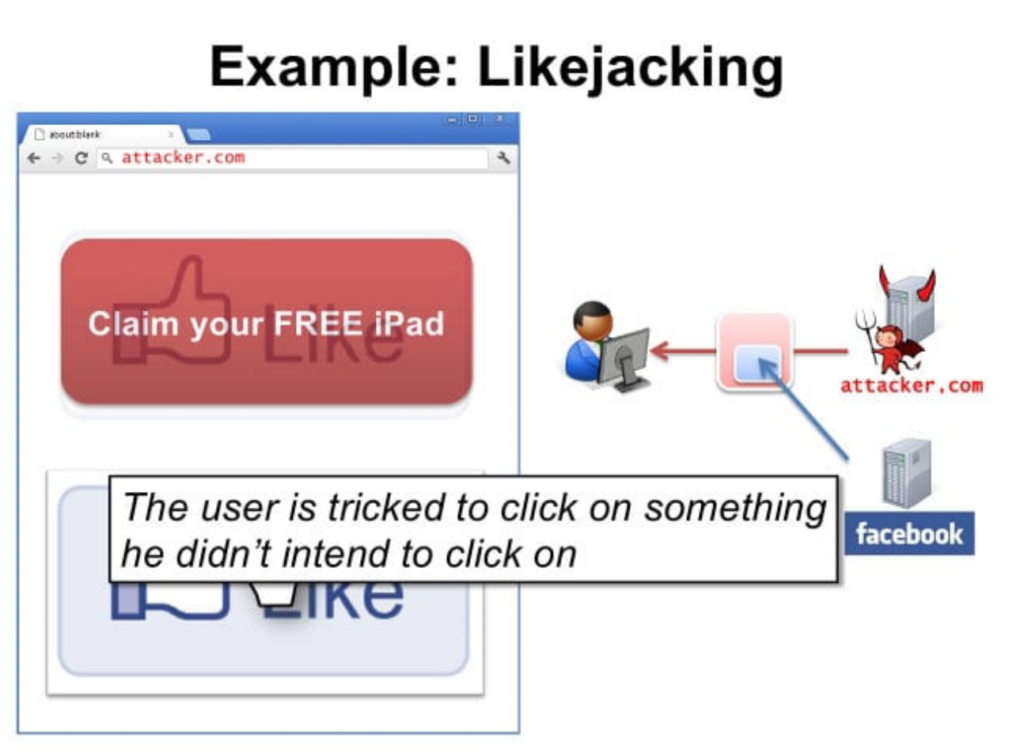
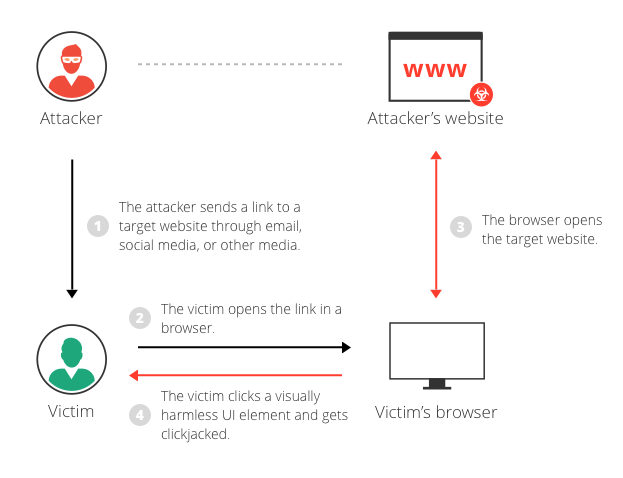
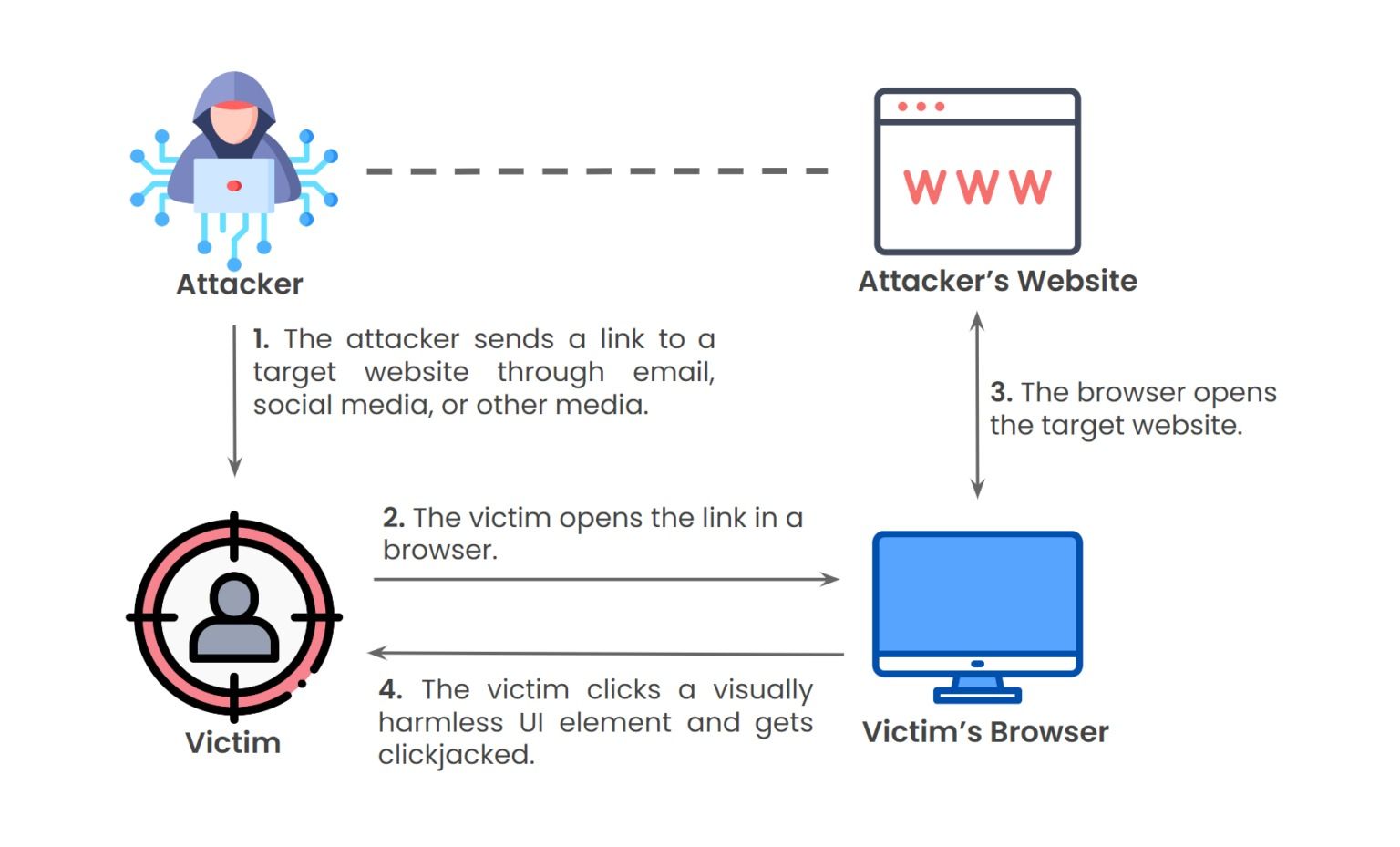
Express style with our remarkable fashion attacks you should know about: clickjacking - abricto security collection of vast arrays of trendy images. stylishly presenting photography, images, and pictures. ideal for style blogs and trend reporting. Discover high-resolution attacks you should know about: clickjacking - abricto security images optimized for various applications. Suitable for various applications including web design, social media, personal projects, and digital content creation All attacks you should know about: clickjacking - abricto security images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Explore the versatility of our attacks you should know about: clickjacking - abricto security collection for various creative and professional projects. Advanced search capabilities make finding the perfect attacks you should know about: clickjacking - abricto security image effortless and efficient. Time-saving browsing features help users locate ideal attacks you should know about: clickjacking - abricto security images quickly. Each image in our attacks you should know about: clickjacking - abricto security gallery undergoes rigorous quality assessment before inclusion. The attacks you should know about: clickjacking - abricto security collection represents years of careful curation and professional standards. Multiple resolution options ensure optimal performance across different platforms and applications.




















![What is a Clickjacking Attack? [+Examples & Prevention]](https://cdn.prod.website-files.com/5e3d3268a134a79339be8368/6218ffe6d2e33946ea3a863c_tJc7QRvvQzP7xl-PVl_YfcZNva3nFr1WYojhjk-kdpCBqMaEolvNVif9yANCBevu-UsBmEfvo9bbAtzdhX2aQdh9EY5upY2a1J4zxA9Y7QZoIoy4f_NcjGtKs60uyg.png)



























![Home [bantechcyber.com]](https://bantechcyber.com/wp-content/uploads/2025/04/7-Steps-on-How-to-Prevent-Cryptojacking-Attacks.png)