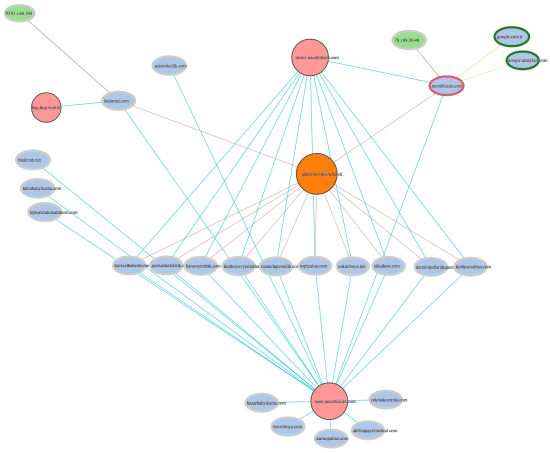
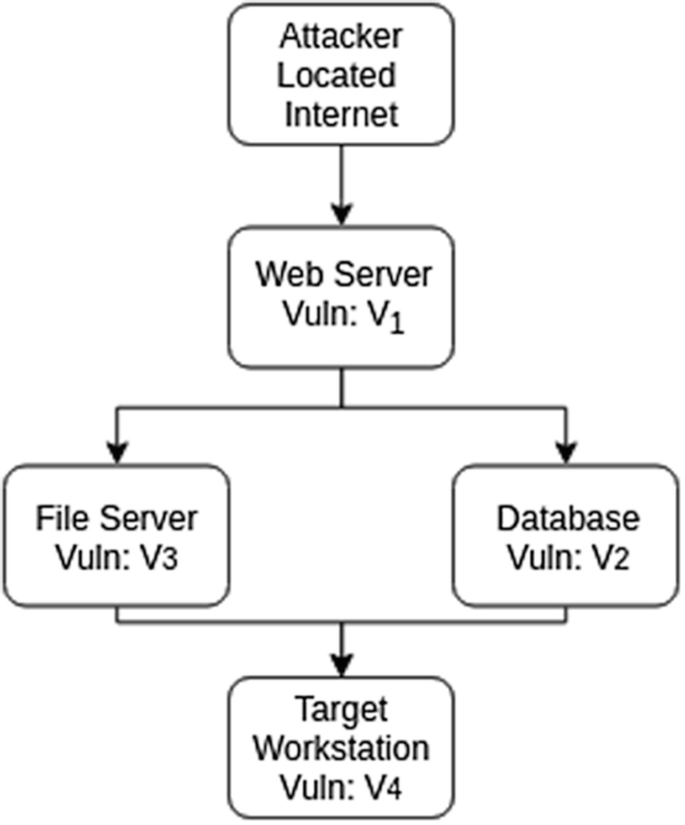
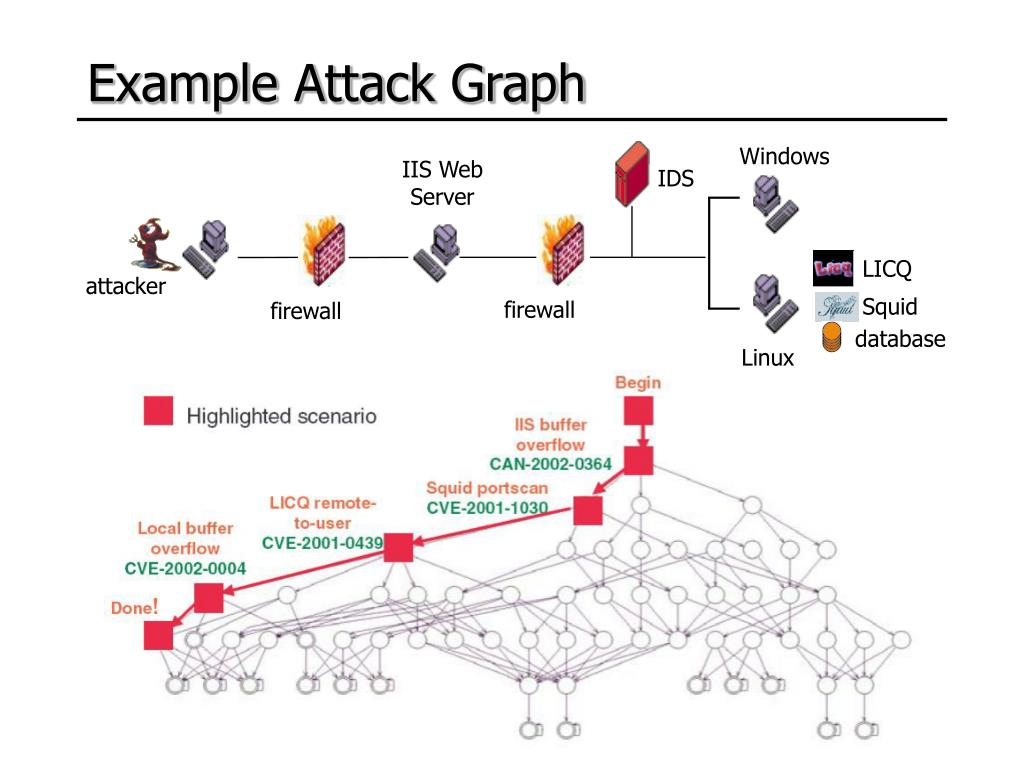
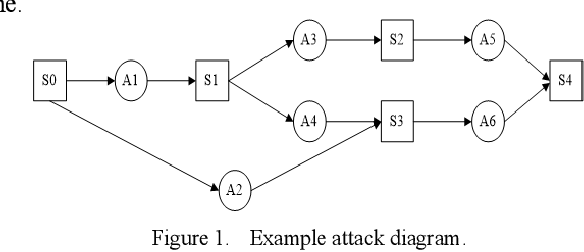
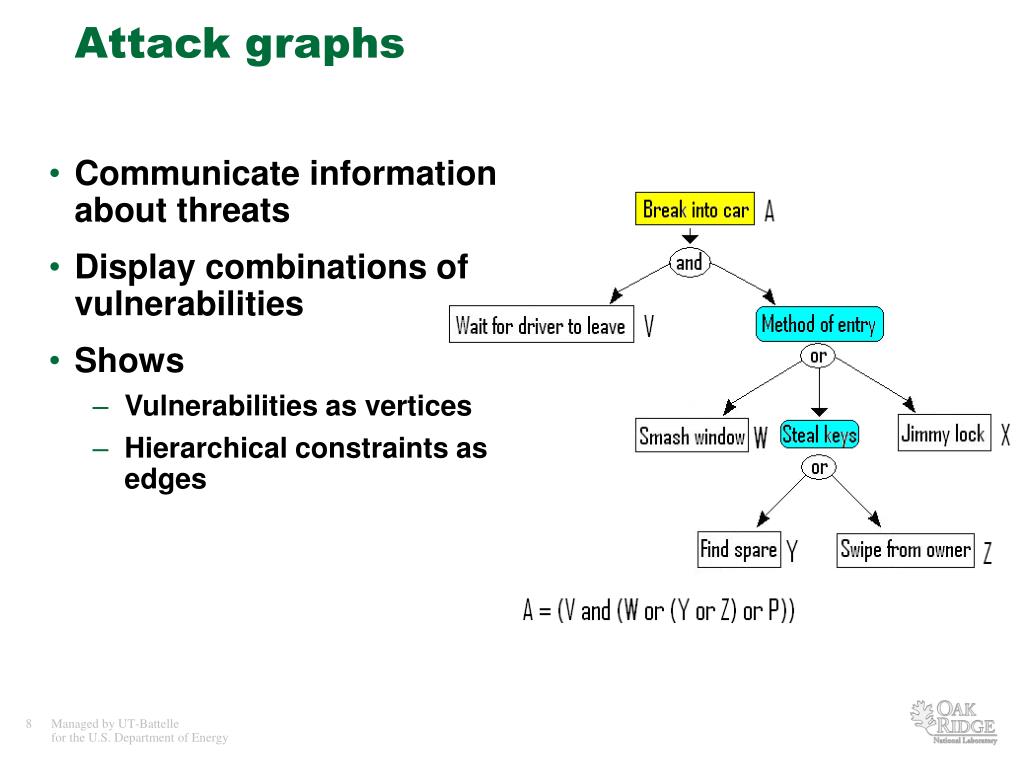
Explore the wilderness of 2: example presentation of attack graph [10]. | download scientific diagram with extensive collections of breathtaking nature photographs. featuring pristine examples of photography, images, and pictures. ideal for nature documentaries and publications. Discover high-resolution 2: example presentation of attack graph [10]. | download scientific diagram images optimized for various applications. Suitable for various applications including web design, social media, personal projects, and digital content creation All 2: example presentation of attack graph [10]. | download scientific diagram images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Discover the perfect 2: example presentation of attack graph [10]. | download scientific diagram images to enhance your visual communication needs. Professional licensing options accommodate both commercial and educational usage requirements. Reliable customer support ensures smooth experience throughout the 2: example presentation of attack graph [10]. | download scientific diagram selection process. Diverse style options within the 2: example presentation of attack graph [10]. | download scientific diagram collection suit various aesthetic preferences. Multiple resolution options ensure optimal performance across different platforms and applications. The 2: example presentation of attack graph [10]. | download scientific diagram archive serves professionals, educators, and creatives across diverse industries. The 2: example presentation of attack graph [10]. | download scientific diagram collection represents years of careful curation and professional standards.











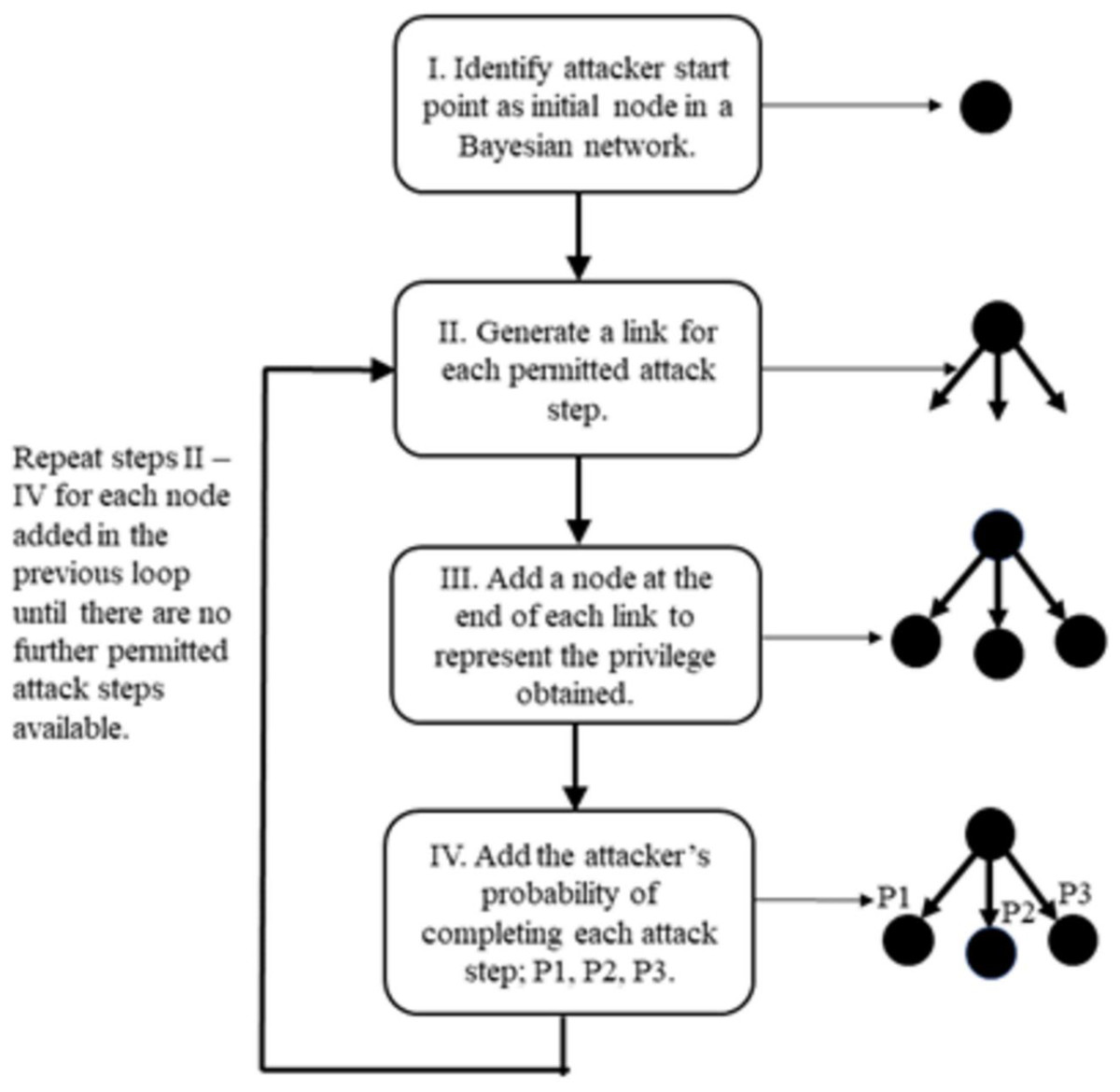
![Attack graph generation phases [35]. | Download Scientific Diagram](https://www.researchgate.net/profile/Zaid-Alaaraji/publication/362432424/figure/fig1/AS:1184957871460352@1659527380589/Attack-graph-generation-phases-35.png)

![An Attack Graph Sample [19]. | Download Scientific Diagram](https://www.researchgate.net/profile/Zaid-Alaaraji/publication/352020993/figure/fig2/AS:1029858750627840@1622548868164/Attack-Graph-uses-20_Q320.jpg)








![Attack graph example (source: Wang et al. [15]) | Download Scientific ...](https://mavink.com/images/loadingwhitetransparent.gif)


![Attack graph showing a successful attack for user2 [11] Figures 6 and ...](https://www.researchgate.net/profile/Eduard-Babulak/publication/354750950/figure/fig5/AS:1075157590347776@1633348953491/Attack-graph-showing-a-successful-attack-for-user2-11-Figures-6-and-Figure-7-show.jpg)

![2: Example presentation of attack graph [10]. | Download Scientific Diagram](https://www.researchgate.net/profile/Ali-Behfarnia-2/publication/352164613/figure/fig2/AS:1031520043155456@1622944951648/Example-presentation-of-attack-graph-10_Q320.jpg)

![Example Attack Graph [40] | Download Scientific Diagram](https://www.researchgate.net/publication/360333715/figure/fig2/AS:1151490592899073@1651548159287/Example-Attack-Graph-40.png)
![Example Attack Graph [40] | Download Scientific Diagram](https://www.researchgate.net/profile/Stefan-Rass/publication/360333715/figure/fig2/AS:1151490592899073@1651548159287/Example-Attack-Graph-40_Q320.jpg)







































![An Attack Graph Sample [19]. | Download Scientific Diagram](https://www.researchgate.net/publication/352020993/figure/fig1/AS:1029858746445826@1622548867938/An-Attack-Graph-Sample-19.jpg)



![What Is a Prompt Injection Attack? [Examples & Prevention] - Palo Alto ...](https://www.paloaltonetworks.com/content/dam/pan/en_US/images/cyberpedia/what-is-a-prompt-injection-attack/GenAI-Security-2025_6-1.png)