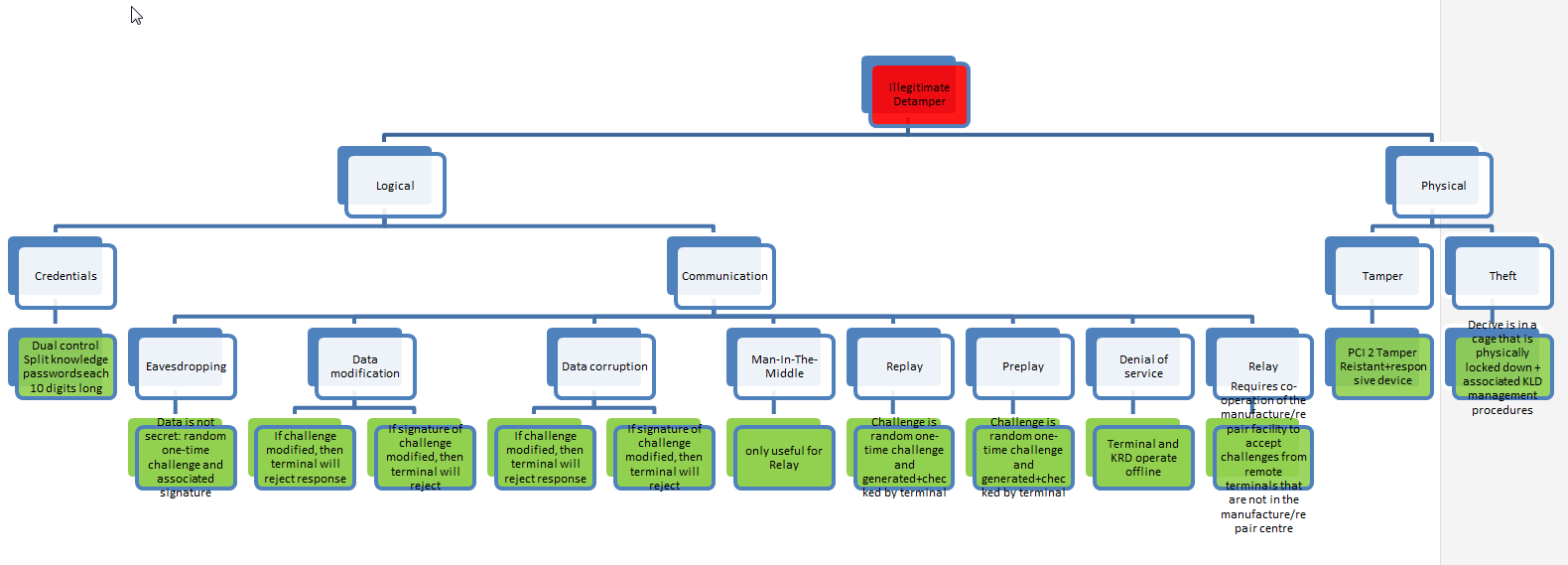
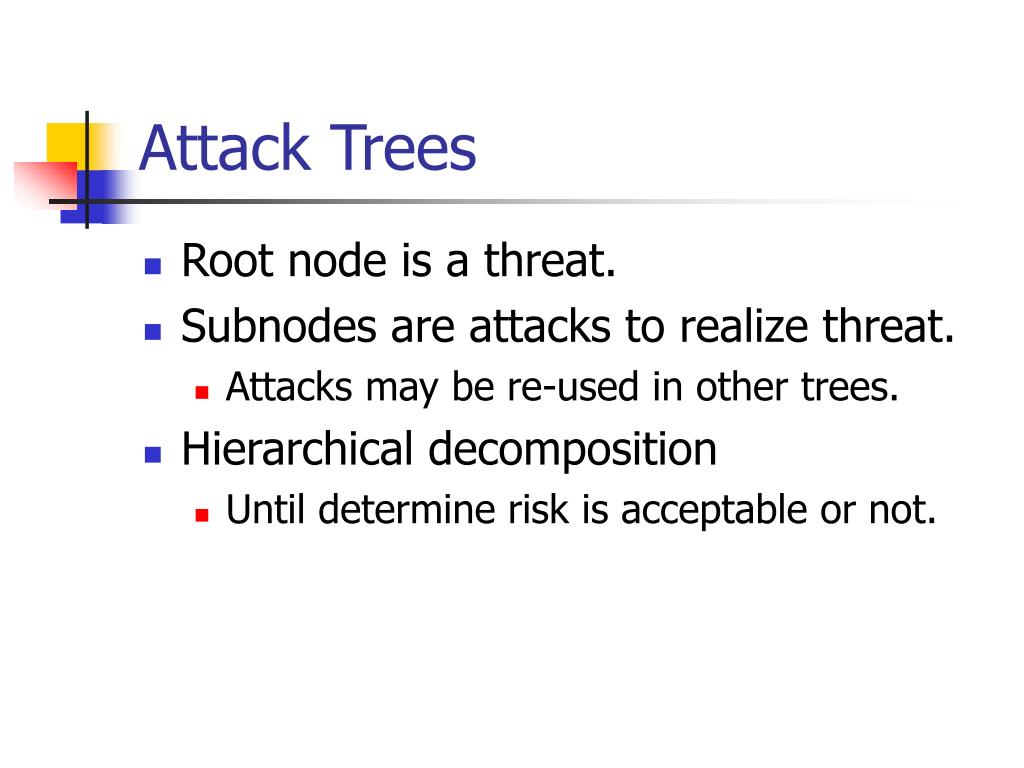
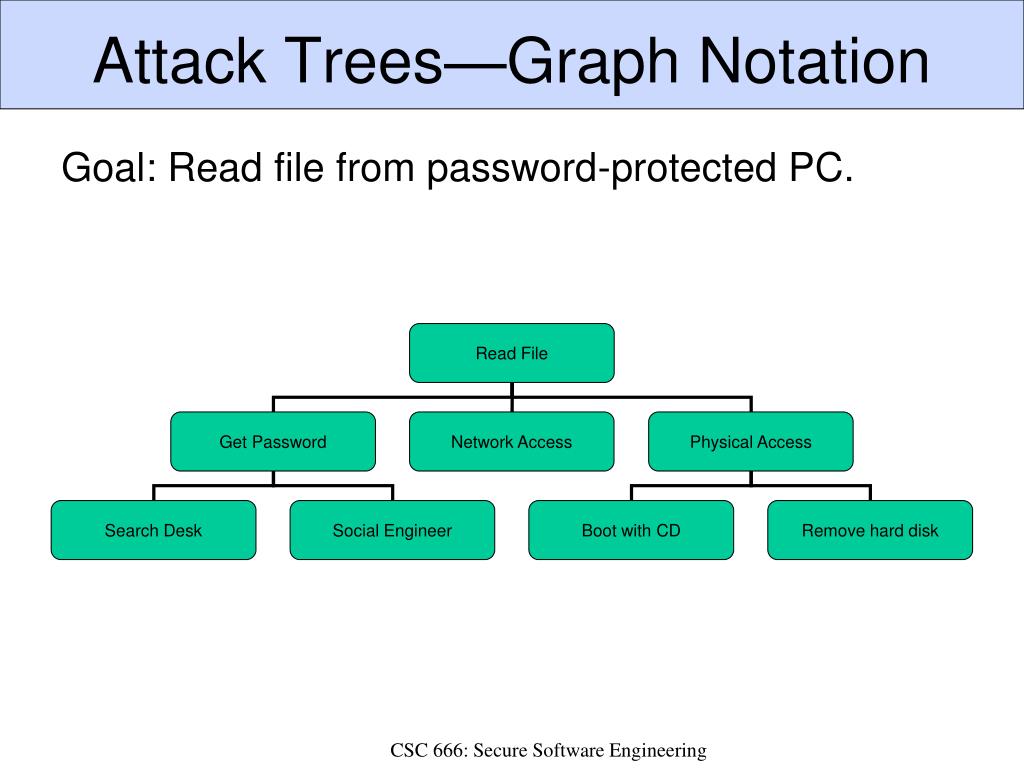
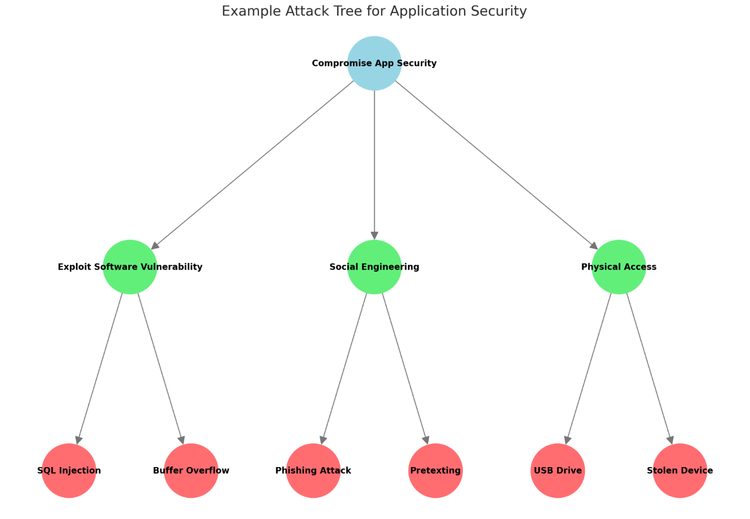
Drive innovation with our technology example of attack trees | download scientific diagram gallery of comprehensive galleries of digital images. technologically showcasing flower, tree, and plant. designed to demonstrate technological advancement. Discover high-resolution example of attack trees | download scientific diagram images optimized for various applications. Suitable for various applications including web design, social media, personal projects, and digital content creation All example of attack trees | download scientific diagram images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Explore the versatility of our example of attack trees | download scientific diagram collection for various creative and professional projects. Our example of attack trees | download scientific diagram database continuously expands with fresh, relevant content from skilled photographers. Whether for commercial projects or personal use, our example of attack trees | download scientific diagram collection delivers consistent excellence. Cost-effective licensing makes professional example of attack trees | download scientific diagram photography accessible to all budgets. The example of attack trees | download scientific diagram archive serves professionals, educators, and creatives across diverse industries. Multiple resolution options ensure optimal performance across different platforms and applications. Professional licensing options accommodate both commercial and educational usage requirements.

























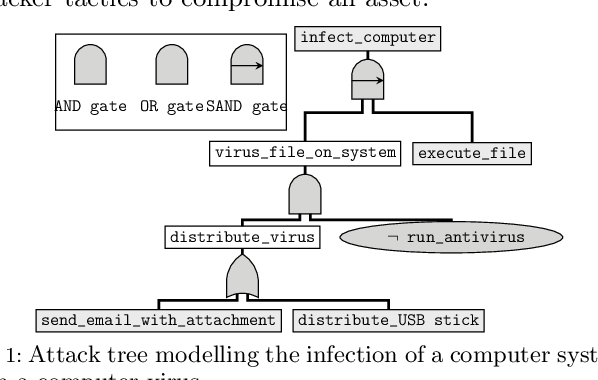
![Attack tree example [6]. | Download Scientific Diagram](https://www.researchgate.net/publication/321736333/figure/fig1/AS:649389760606218@1531837992482/Attack-tree-example-6.png)
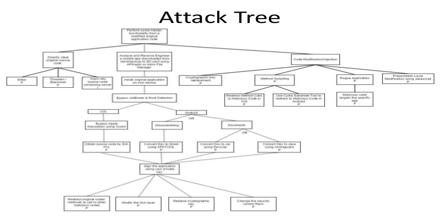
![An Example Attack Tree [16] | Download Scientific Diagram](https://www.researchgate.net/profile/Kennedy-Torkura/publication/322697698/figure/fig4/AS:637746691452939@1529062068389/Attack-Tree-of-CloudRAID-showing-possible-paths-an-attacker-could-follow-to-compromise_Q640.jpg)




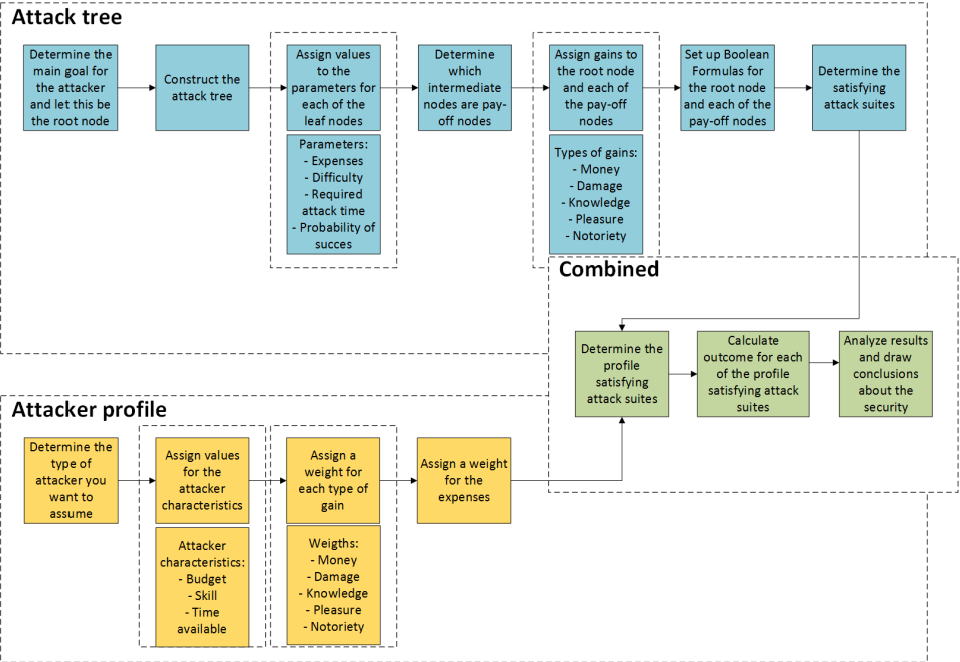
![An Example Attack Tree [16] | Download Scientific Diagram](https://www.researchgate.net/publication/322697698/figure/fig2/AS:637746691452938@1529062068324/An-Example-Attack-Tree-16.png)












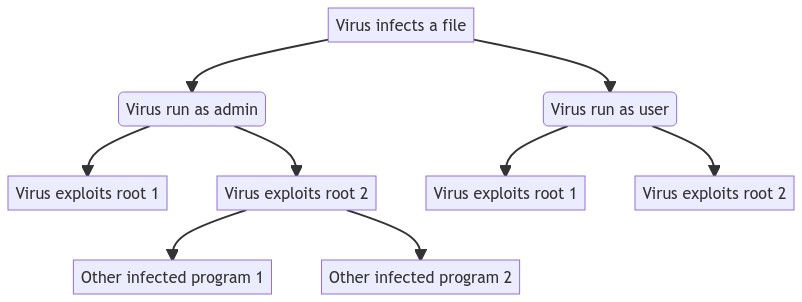
![Generic Attack Tree Structure [10] | Download Scientific Diagram](https://www.researchgate.net/publication/372137168/figure/fig3/AS:11431281172631939@1688614373774/Generic-Attack-Tree-Structure-10_Q320.jpg)







![An Example Attack Tree [16] | Download Scientific Diagram](https://www.researchgate.net/profile/Kennedy-Torkura/publication/322697698/figure/fig5/AS:637746691457041@1529062068422/Attack-Graph-for-Paths-3-4-and-6-of-the-Attack-Tree-Figure-4_Q320.jpg)











![An Example Attack Tree [16] | Download Scientific Diagram](https://www.researchgate.net/profile/Kennedy-Torkura/publication/322697698/figure/fig2/AS:637746691452938@1529062068324/An-Example-Attack-Tree-16_Q640.jpg)




























![Evolution of 7C's generative framework [3] | Download Scientific Diagram](https://www.researchgate.net/profile/Sharmila-Sinha-3/publication/335796984/figure/fig1/AS:802756231188481@1568403408584/Evolution-of-7Cs-generative-framework-3_Q640.jpg)