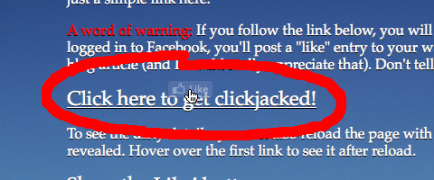
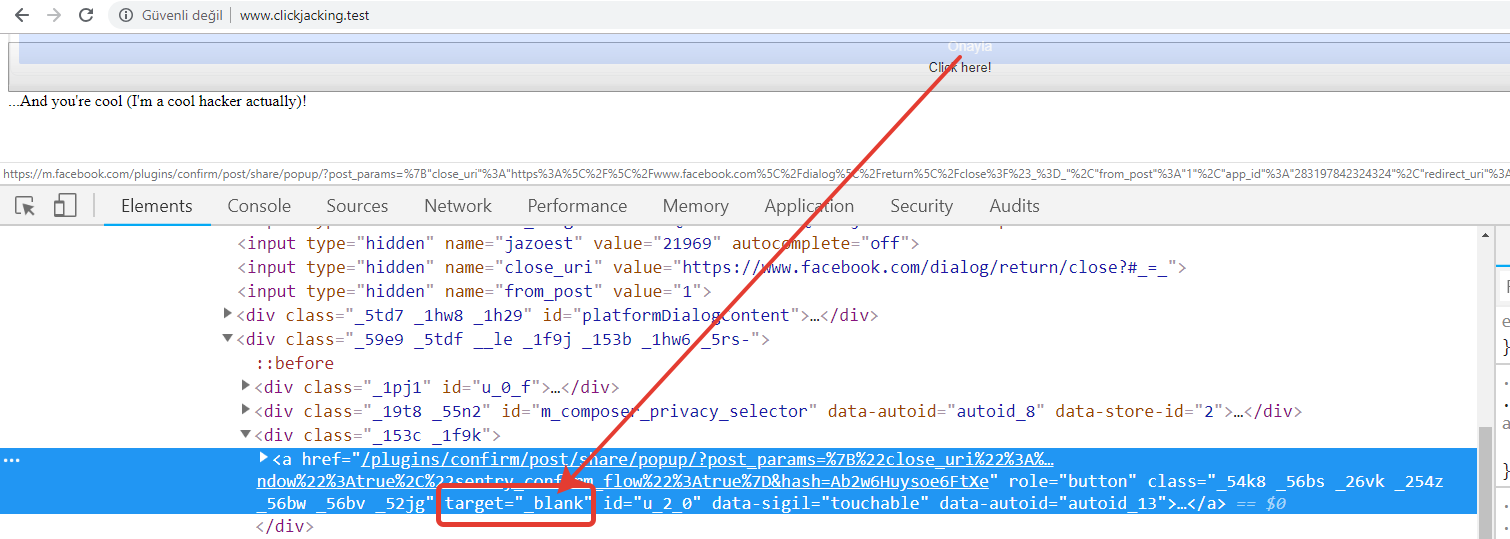
Drive innovation with our technology an example of likejacking (facebook clickjacking) | zscaler gallery of countless digital images. innovatively presenting photography, images, and pictures. ideal for innovation showcases and presentations. Our an example of likejacking (facebook clickjacking) | zscaler collection features high-quality images with excellent detail and clarity. Suitable for various applications including web design, social media, personal projects, and digital content creation All an example of likejacking (facebook clickjacking) | zscaler images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Explore the versatility of our an example of likejacking (facebook clickjacking) | zscaler collection for various creative and professional projects. Advanced search capabilities make finding the perfect an example of likejacking (facebook clickjacking) | zscaler image effortless and efficient. The an example of likejacking (facebook clickjacking) | zscaler archive serves professionals, educators, and creatives across diverse industries. Comprehensive tagging systems facilitate quick discovery of relevant an example of likejacking (facebook clickjacking) | zscaler content. Cost-effective licensing makes professional an example of likejacking (facebook clickjacking) | zscaler photography accessible to all budgets. Diverse style options within the an example of likejacking (facebook clickjacking) | zscaler collection suit various aesthetic preferences. Multiple resolution options ensure optimal performance across different platforms and applications.





![What is a Clickjacking Attack? [+Examples & Prevention]](https://cdn.prod.website-files.com/5e3d3268a134a79339be8368/6218ffe6d2e33946ea3a863c_tJc7QRvvQzP7xl-PVl_YfcZNva3nFr1WYojhjk-kdpCBqMaEolvNVif9yANCBevu-UsBmEfvo9bbAtzdhX2aQdh9EY5upY2a1J4zxA9Y7QZoIoy4f_NcjGtKs60uyg.png)






![What is a Clickjacking Attack? [+Examples & Prevention]](https://cdn.prod.website-files.com/5e3d3268a134a79339be8368/6218ffe81407f1b009c178f7_JC2somFAvkQkEKfSy6ZLNOZwa1Q_-64HgwawhTHGG_75sLd9JbrkWoi90s5rFCBVg24jAlhQ6sjbDxbqI6HiboiNcnXcy8XKojfxbn14ayMzlFKiPJDbk-iMWq26VA.png)









![What is a Clickjacking Attack? [+Examples & Prevention]](https://cdn.prod.website-files.com/5e3d3268a134a79339be8368/6218ffe97ffa67c23aa0cdef_vDXC5Y-FyolHePWmheulqOviuanYKVt80JkdEbXa_1D_J0yCWHeBPbscf2Lz0Lyv9sQbfUXPelmccuWvcgOKtpl0dN3lQ63QGCrX19VRQGDg0F401RvmWwwo5iX-xBHtZ_-tYk0v.png)









.png)





![[WebSec3, Video 10] Clickjacking Definition, Examples - YouTube](https://i.ytimg.com/vi/lJtjo6Me3Ng/maxresdefault.jpg?sqp=-oaymwEmCIAKENAF8quKqQMa8AEB-AH-CYAC0AWKAgwIABABGBMgSyh_MA8=&rs=AOn4CLAwluGJ9LJjHDNR_h0lOkSTKnBFBw)







![What is a Clickjacking Attack? [+Examples & Prevention]](https://cdn.prod.website-files.com/5e3d3268a134a79339be8368/6218ffe8d465fe45d01889d2_hjBQXybrmr8OYTU2rfxXLsDC1-zsk8nldxTDUFu0pK_wbGrpkulPI1naRJL9v408Cz4ogIKMOKl88TK-a59laJ_4LiYqcs6pFhi52JQu0UQdGxHvGKJcO1tEMlynnM77Tk5i4ihT.png)
![What is a Clickjacking Attack? [+Examples & Prevention]](https://cdn.prod.website-files.com/5e3d3268a134a79339be8368/6218ffe84954e87ac6721bde_GRLSmQO7zM3ffhHwyOtFvXAEtsbKjnjPm_l63dWAJ4RFqu6IGH9Vjq8BhZQozCK8RXF9FNrljjSEc4N2NcYNQtZhVJdregvityz_XoNpXrIeTvEo_OoR2a1YRNsz11aFLCznTOl6.png)