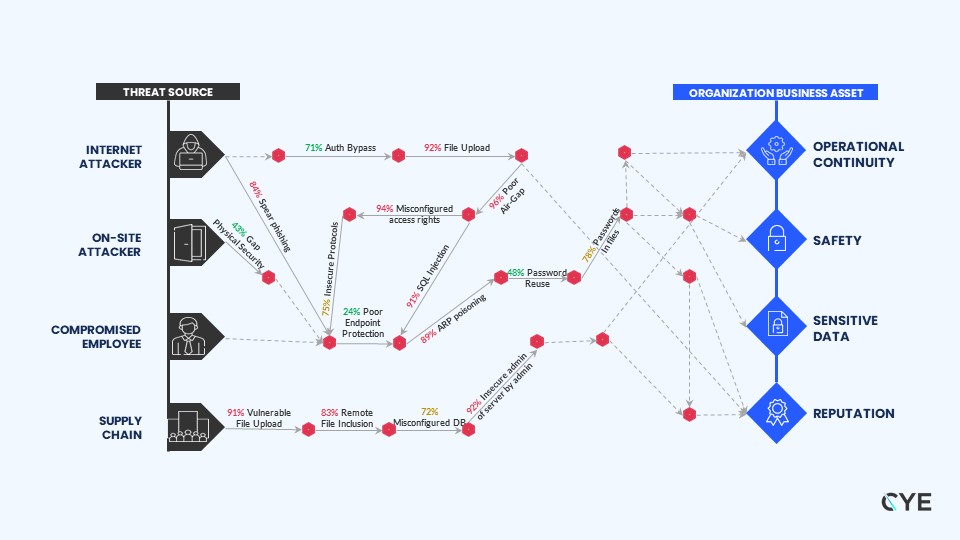
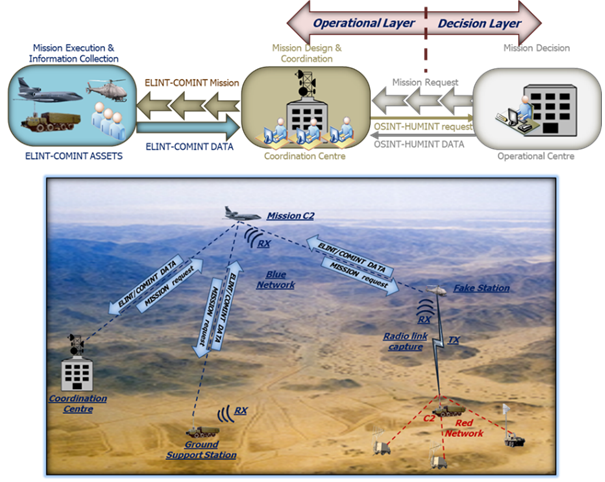
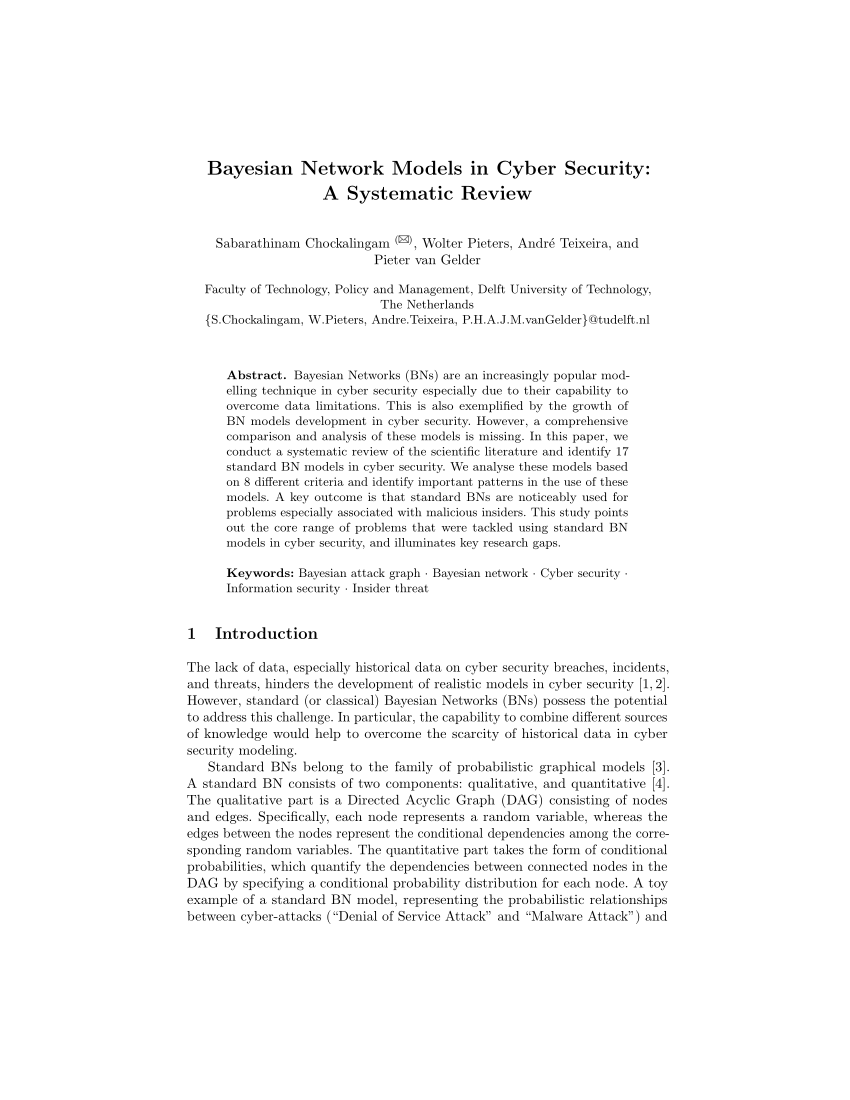
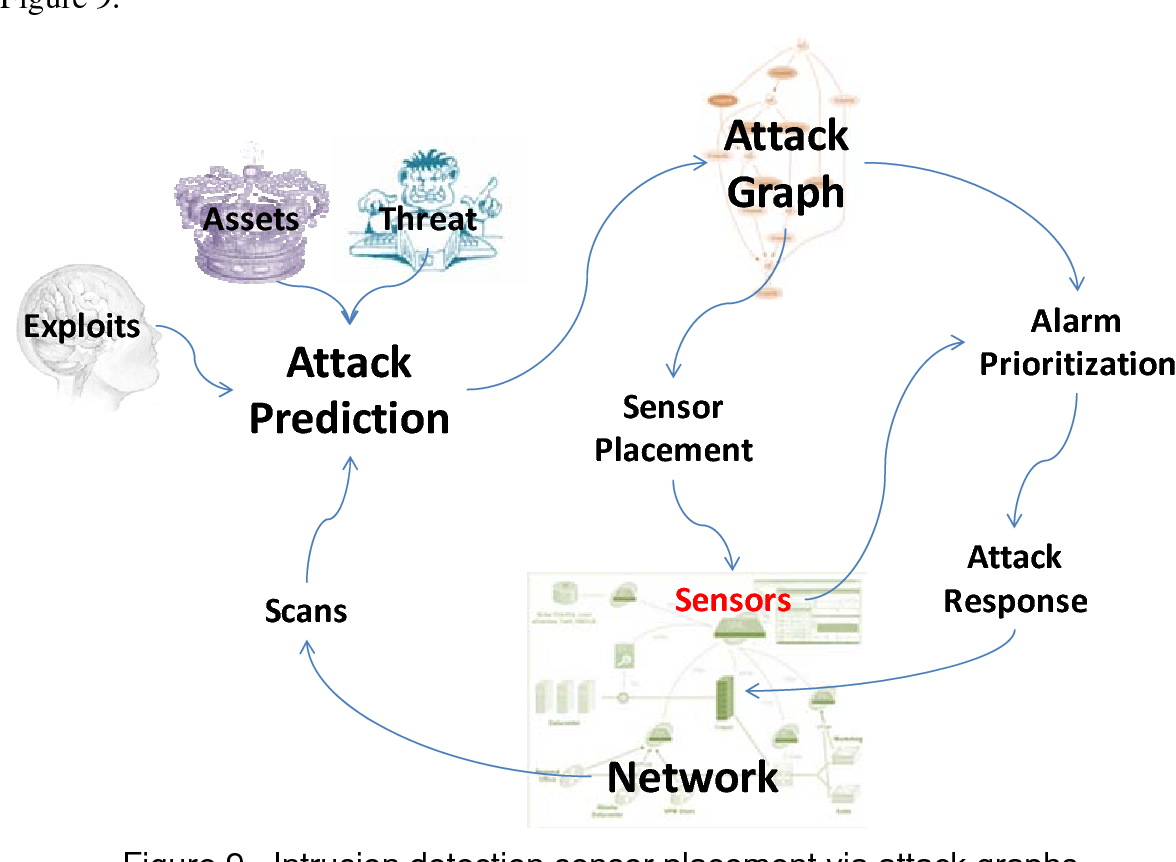
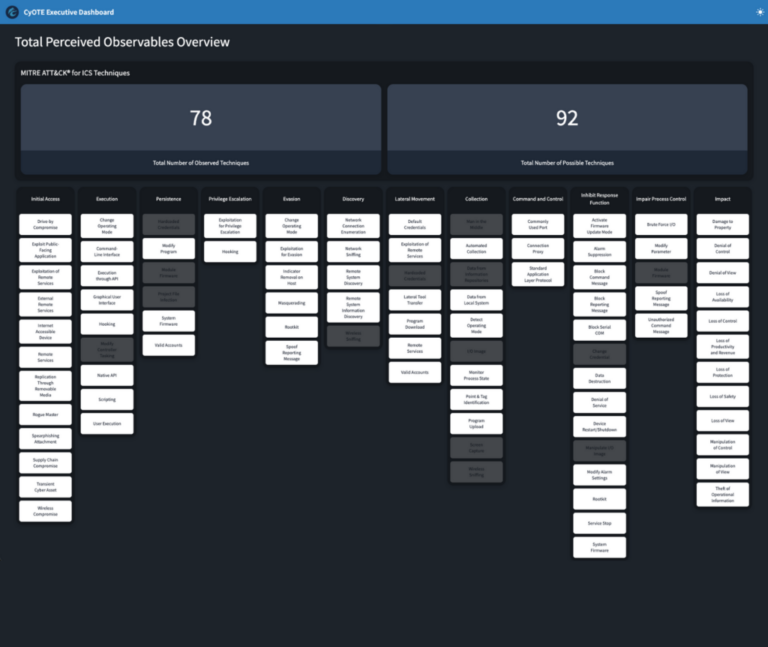
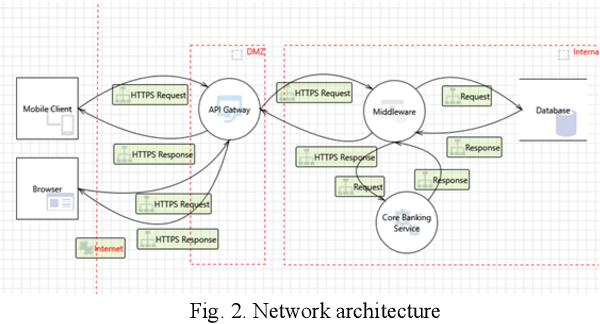
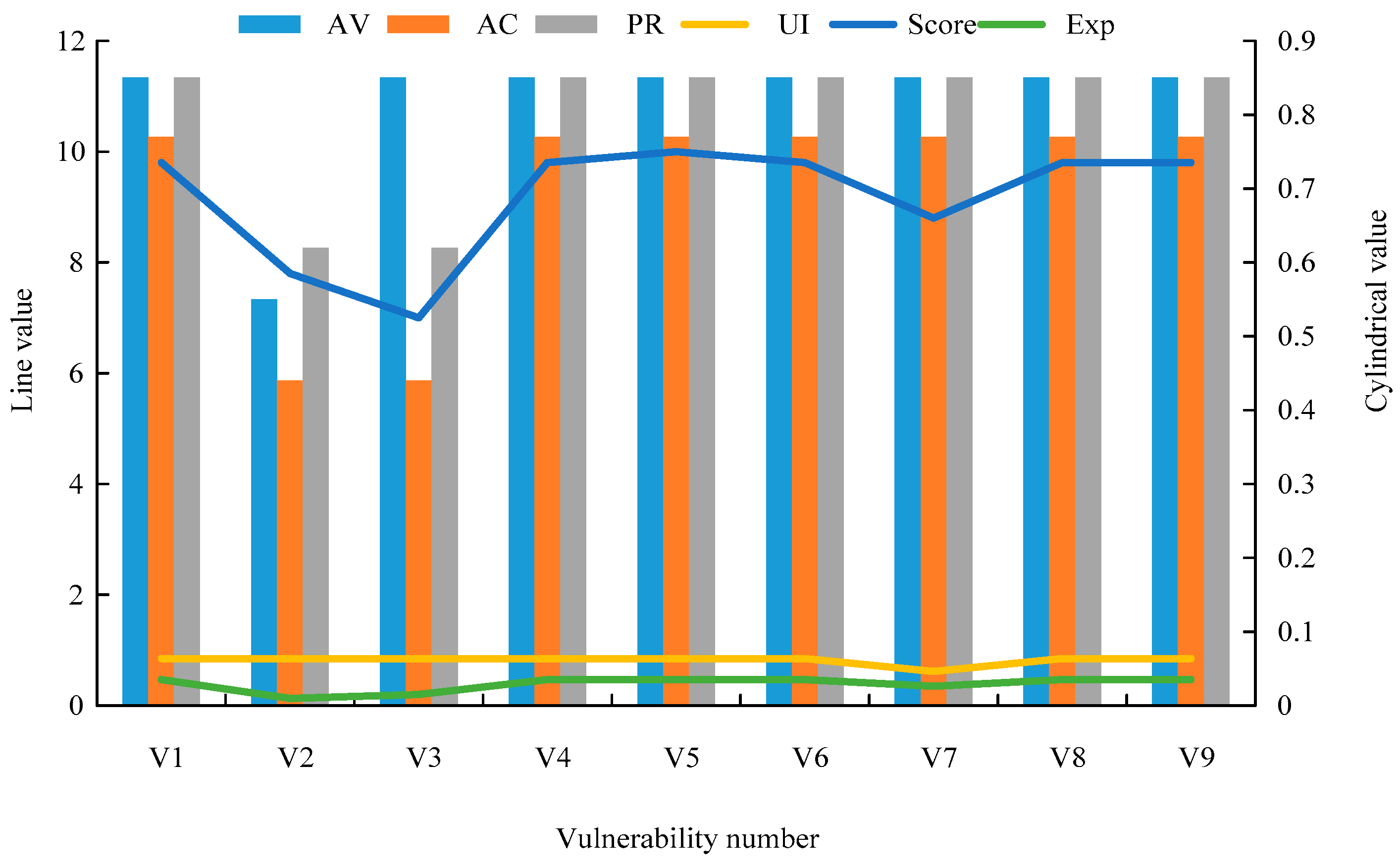
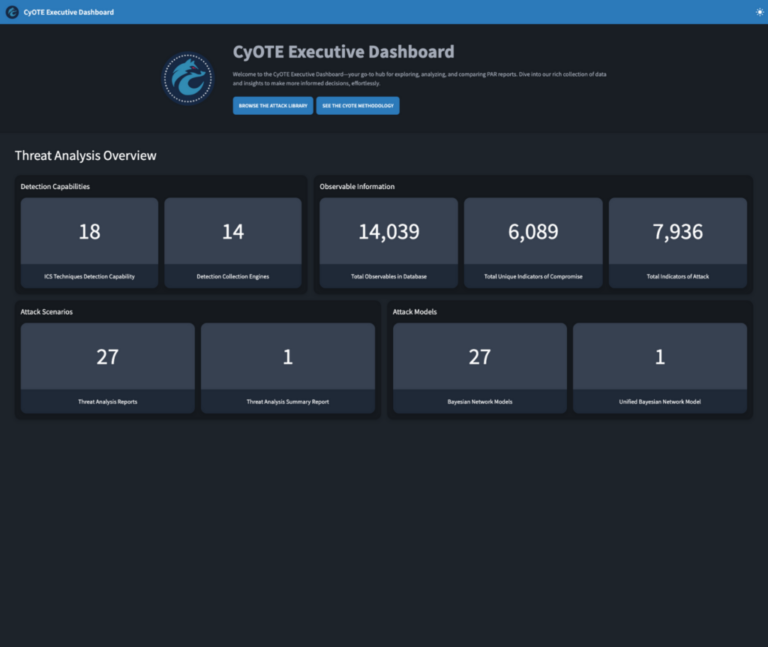
Connect with nature through our remarkable bayesian attack model (bam) - cyote: cybersecurity for the operational collection of substantial collections of natural images. capturing the essence of photography, images, and pictures in their natural habitat. perfect for environmental and conservation projects. Our bayesian attack model (bam) - cyote: cybersecurity for the operational collection features high-quality images with excellent detail and clarity. Suitable for various applications including web design, social media, personal projects, and digital content creation All bayesian attack model (bam) - cyote: cybersecurity for the operational images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Discover the perfect bayesian attack model (bam) - cyote: cybersecurity for the operational images to enhance your visual communication needs. Reliable customer support ensures smooth experience throughout the bayesian attack model (bam) - cyote: cybersecurity for the operational selection process. Comprehensive tagging systems facilitate quick discovery of relevant bayesian attack model (bam) - cyote: cybersecurity for the operational content. Regular updates keep the bayesian attack model (bam) - cyote: cybersecurity for the operational collection current with contemporary trends and styles. Advanced search capabilities make finding the perfect bayesian attack model (bam) - cyote: cybersecurity for the operational image effortless and efficient.

































![Illustration of a Bayesian network. Figure from Ref. [8]. | Download ...](https://www.researchgate.net/publication/365081454/figure/fig1/AS:11431281094628070@1667532218181/Illustration-of-a-Bayesian-network-Figure-from-Ref-8.png)