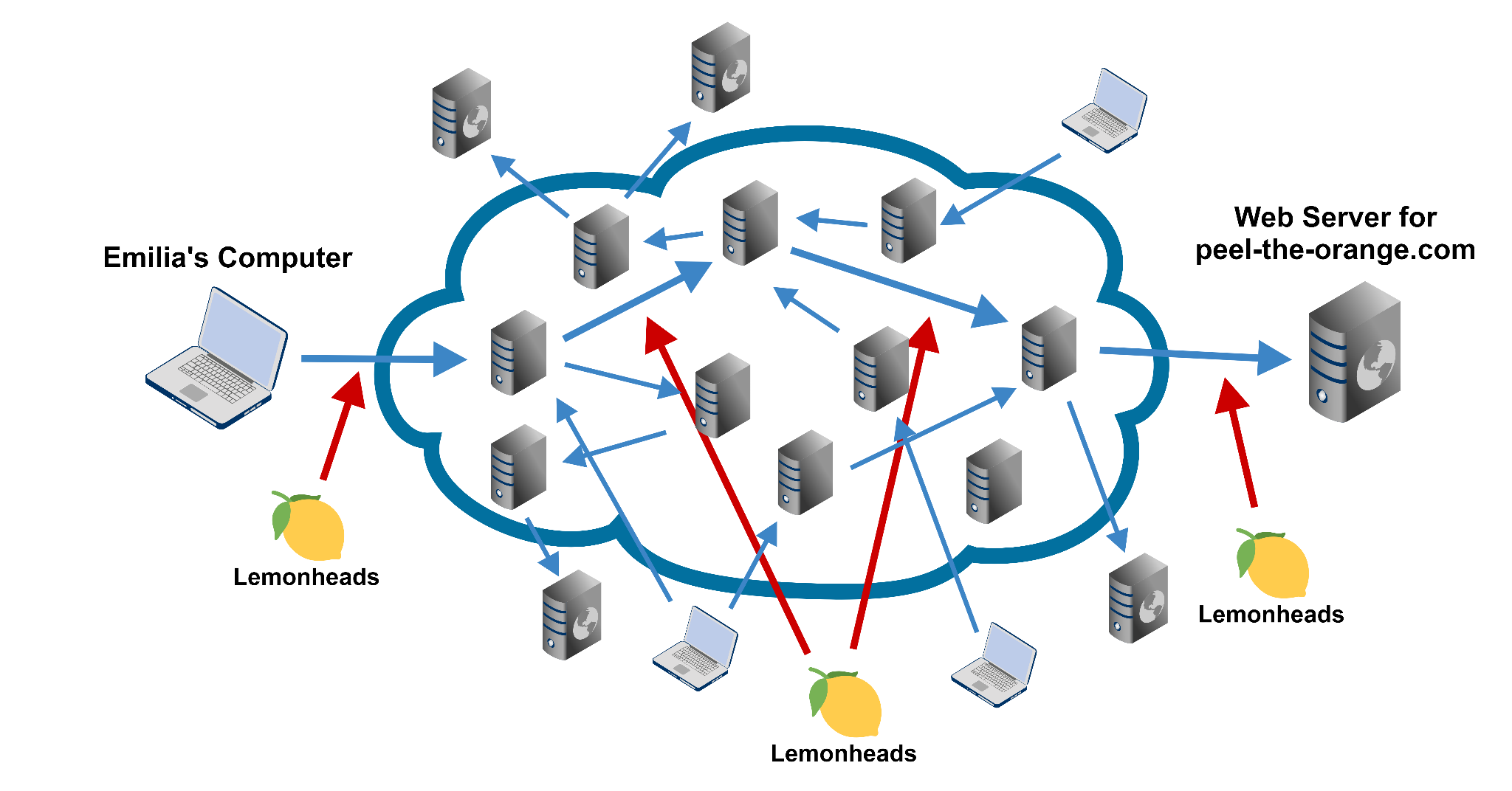
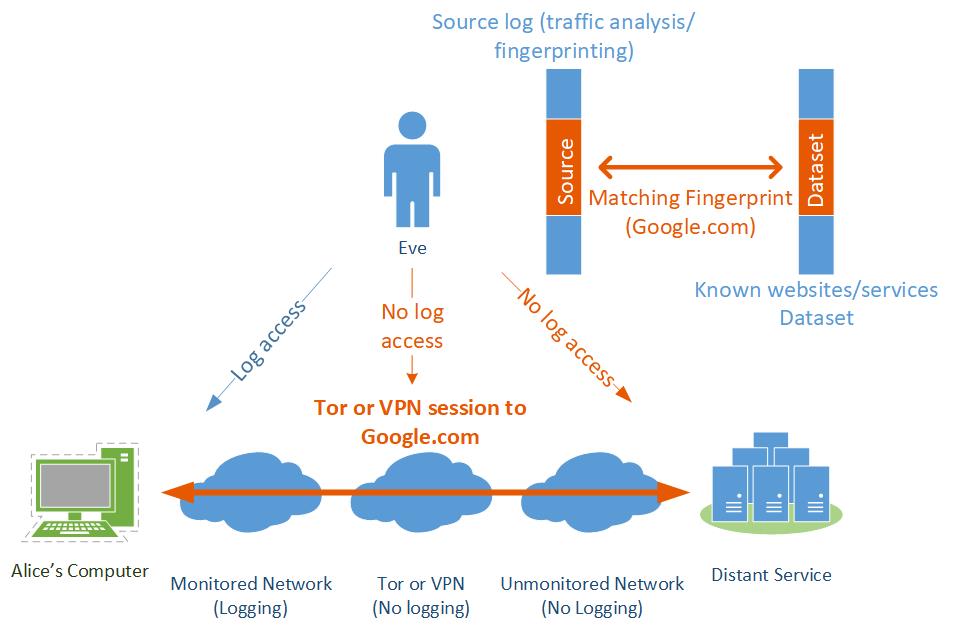
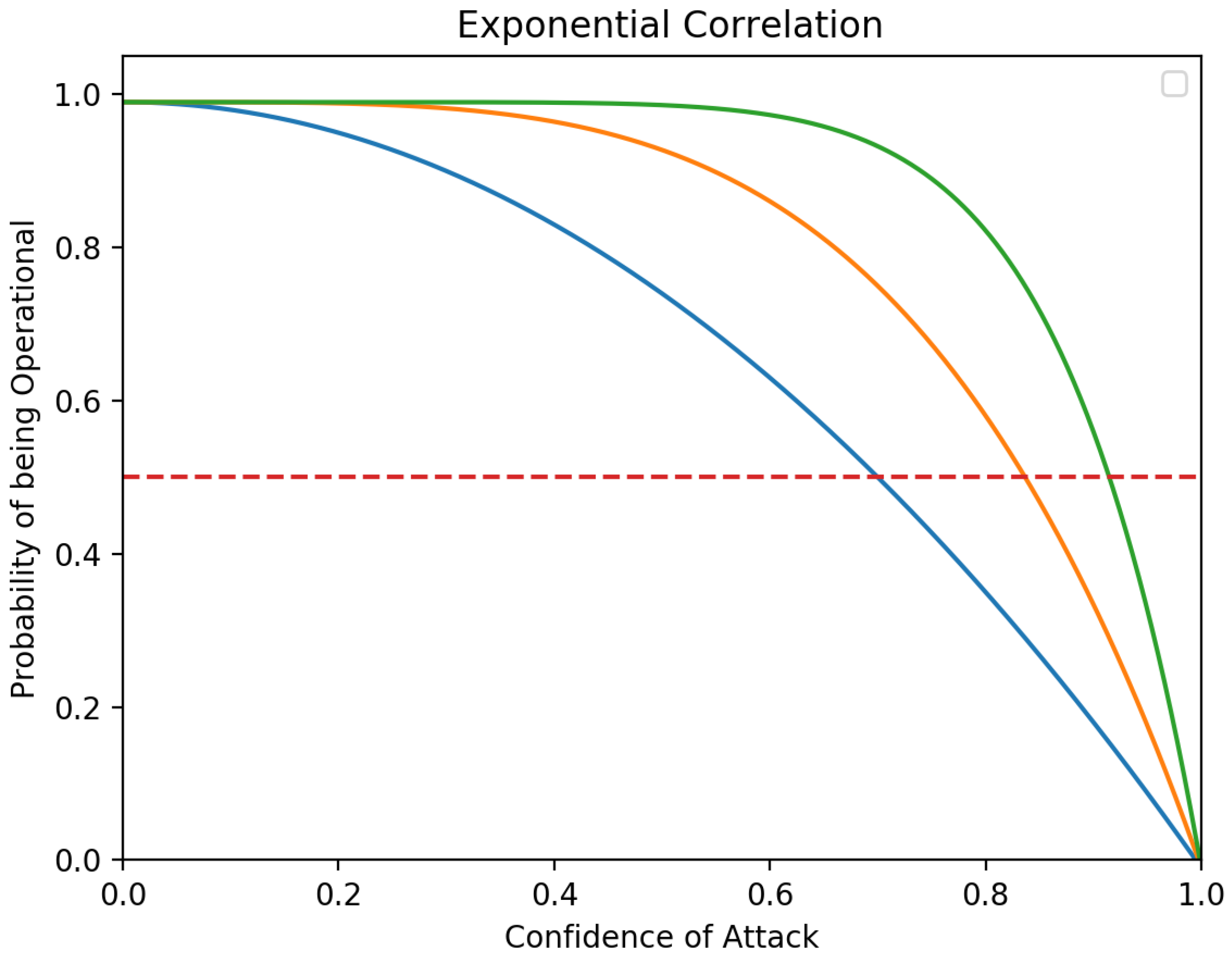
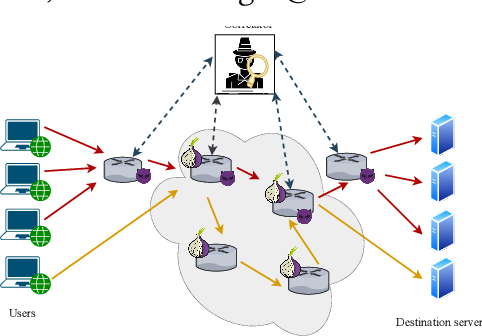
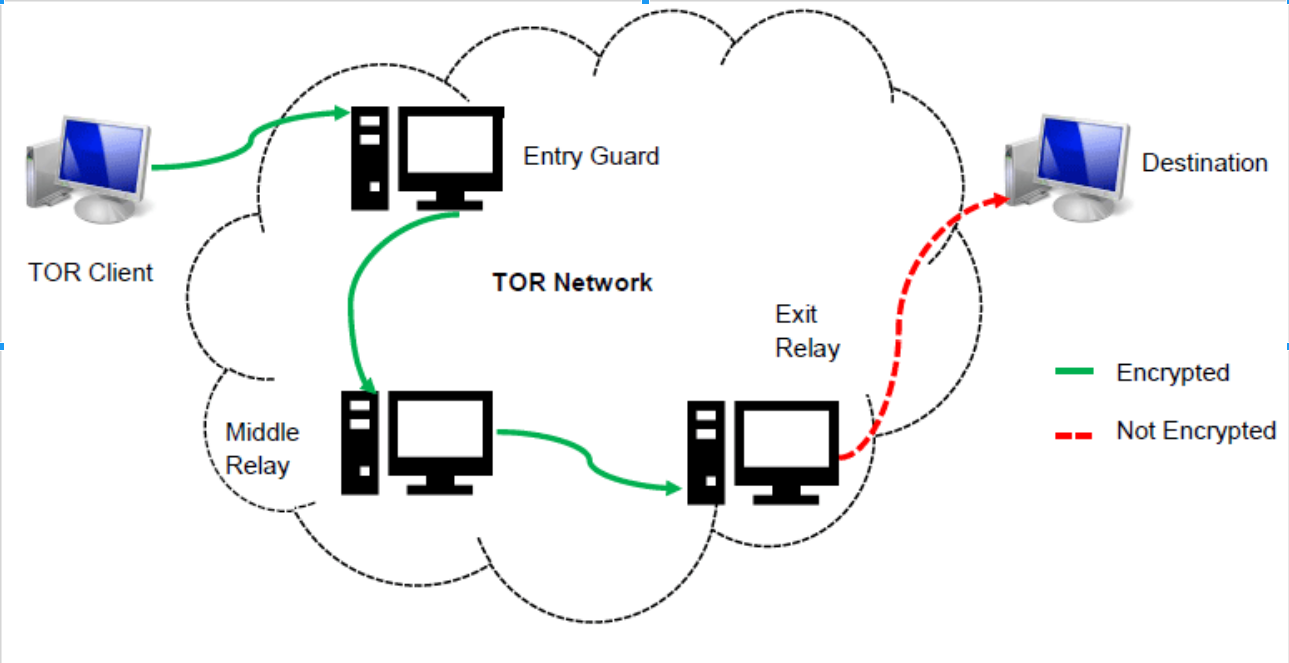
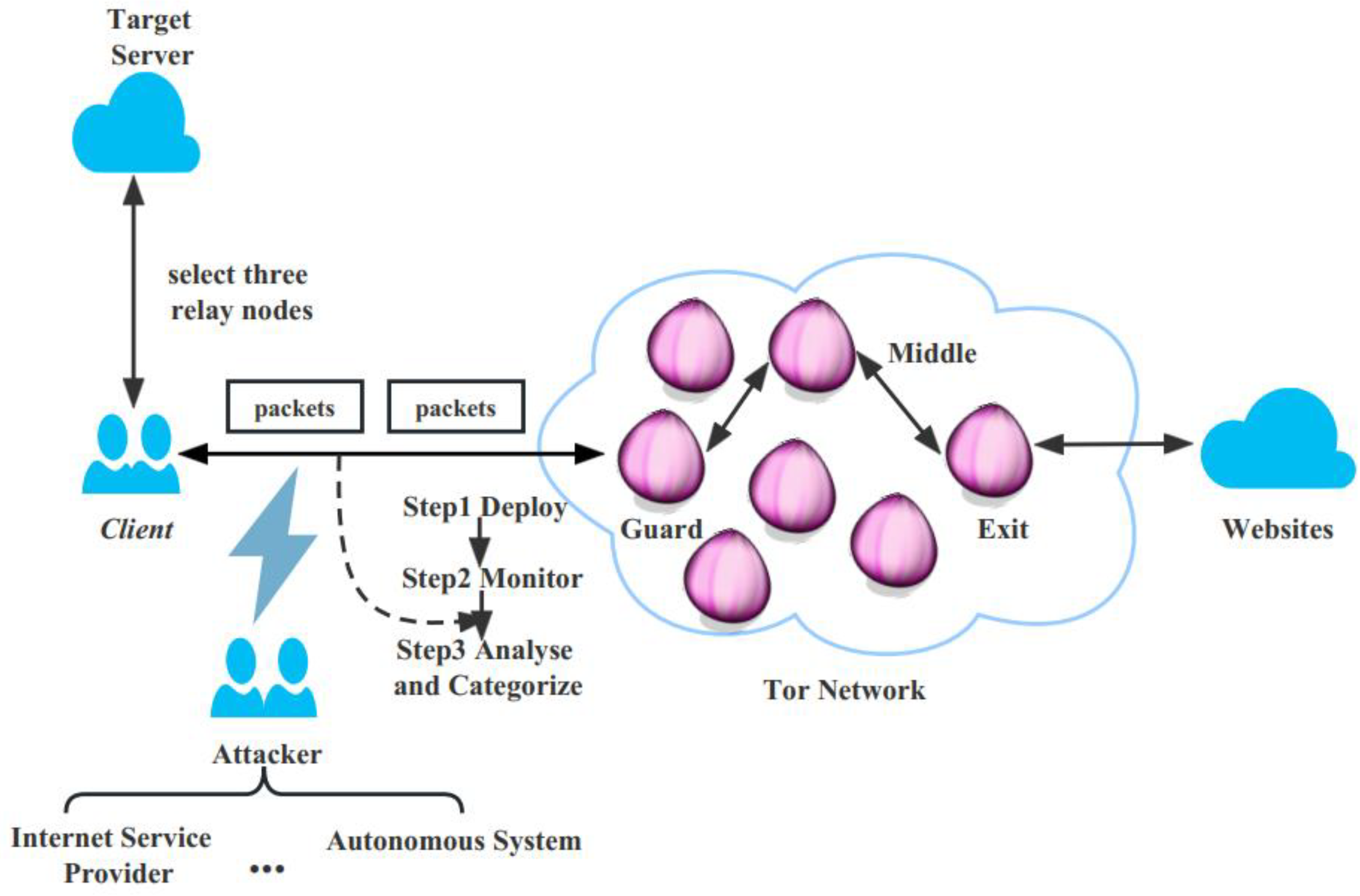
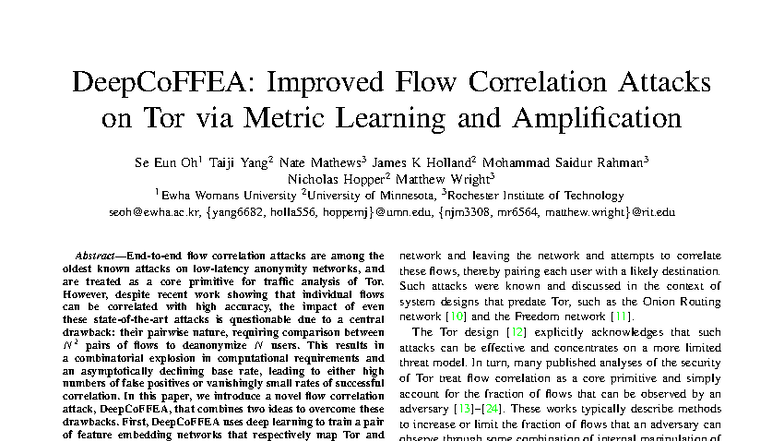
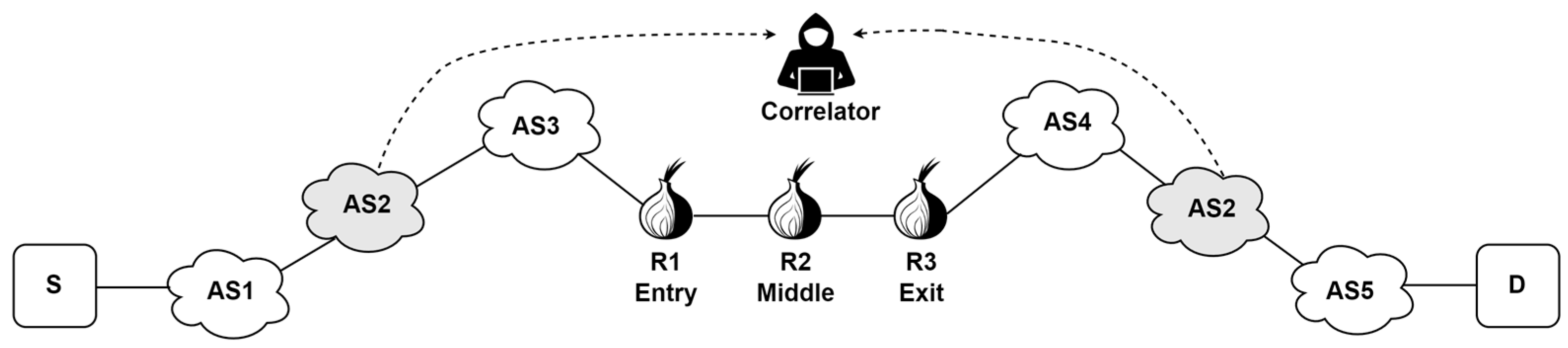
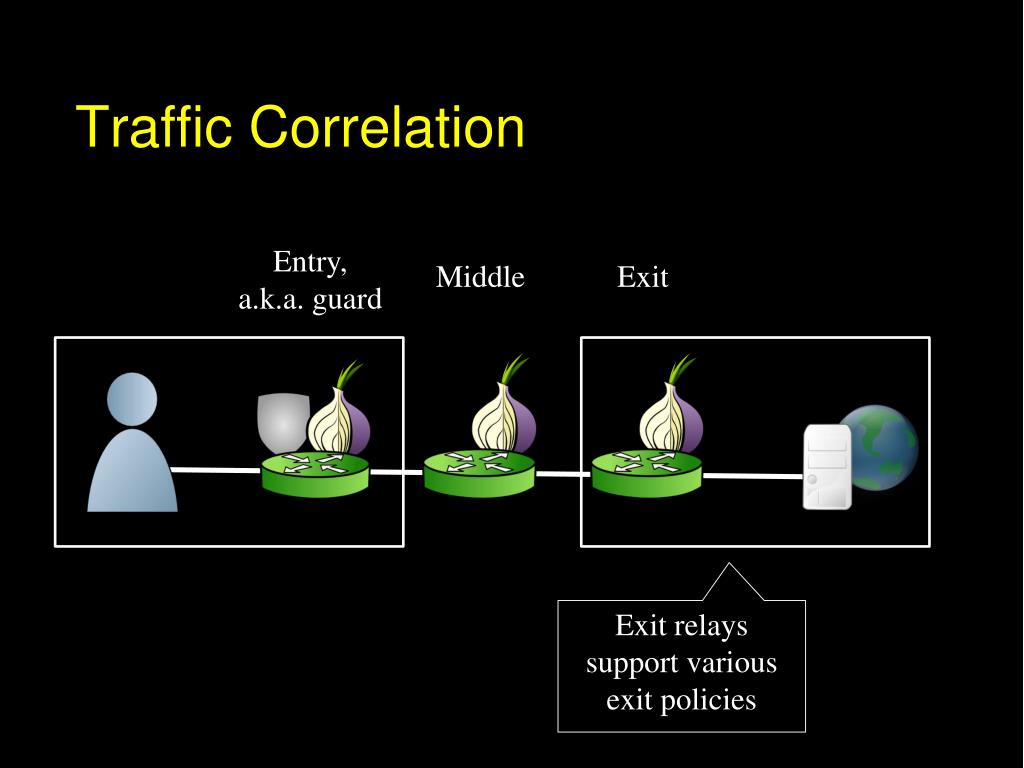
Explore the simplicity of the main process of flow correlation attack on tor. the adversary through vast arrays of elegant photographs. featuring understated examples of computer, digital, and electronic. designed to emphasize clarity and focus. Our the main process of flow correlation attack on tor. the adversary collection features high-quality images with excellent detail and clarity. Suitable for various applications including web design, social media, personal projects, and digital content creation All the main process of flow correlation attack on tor. the adversary images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Explore the versatility of our the main process of flow correlation attack on tor. the adversary collection for various creative and professional projects. Professional licensing options accommodate both commercial and educational usage requirements. Whether for commercial projects or personal use, our the main process of flow correlation attack on tor. the adversary collection delivers consistent excellence. Cost-effective licensing makes professional the main process of flow correlation attack on tor. the adversary photography accessible to all budgets. Instant download capabilities enable immediate access to chosen the main process of flow correlation attack on tor. the adversary images.






























![Quantized correlation encoding attack flow by Xu et al. [29] | Download ...](https://www.researchgate.net/publication/351357734/figure/fig19/AS:1020381724942348@1620289369909/Quantized-correlation-encoding-attack-flow-by-Xu-et-al-29.png)