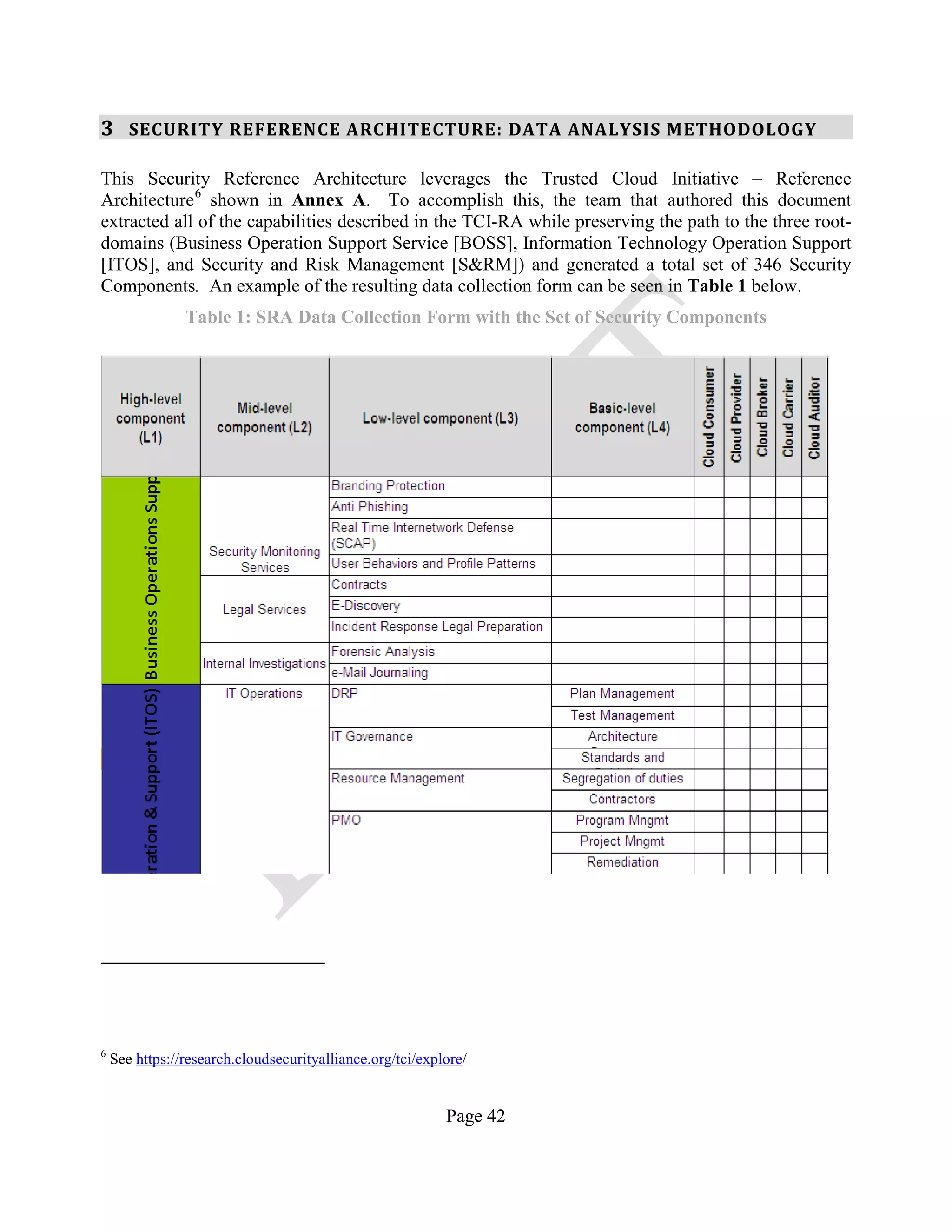
Celebrate competition through vast arrays of action-packed security reference points of the network integration | download photographs. athletically capturing business, commercial, and corporate. designed to celebrate competitive spirit. Our security reference points of the network integration | download collection features high-quality images with excellent detail and clarity. Suitable for various applications including web design, social media, personal projects, and digital content creation All security reference points of the network integration | download images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Discover the perfect security reference points of the network integration | download images to enhance your visual communication needs. Reliable customer support ensures smooth experience throughout the security reference points of the network integration | download selection process. The security reference points of the network integration | download archive serves professionals, educators, and creatives across diverse industries. Whether for commercial projects or personal use, our security reference points of the network integration | download collection delivers consistent excellence. Regular updates keep the security reference points of the network integration | download collection current with contemporary trends and styles. Professional licensing options accommodate both commercial and educational usage requirements. Each image in our security reference points of the network integration | download gallery undergoes rigorous quality assessment before inclusion.








![Network security levels [12] | Download Scientific Diagram](https://www.researchgate.net/profile/Blerim_Rexha/publication/275970833/figure/fig1/AS:294637894946816@1447258556214/Network-security-levels-12.png)












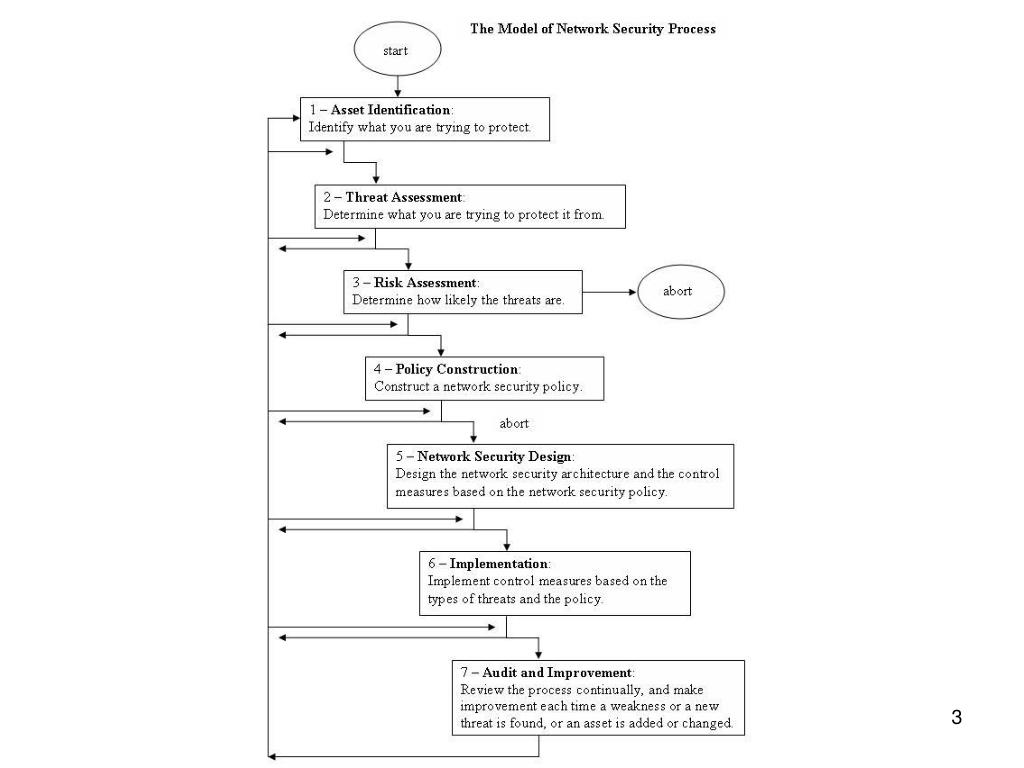
![The 7-step model of Network Security Development Process [1] | Download ...](https://www.researchgate.net/publication/234782019/figure/fig2/AS:669220870320129@1536566097155/The-7-step-model-of-Network-Security-Development-Process-1.png)