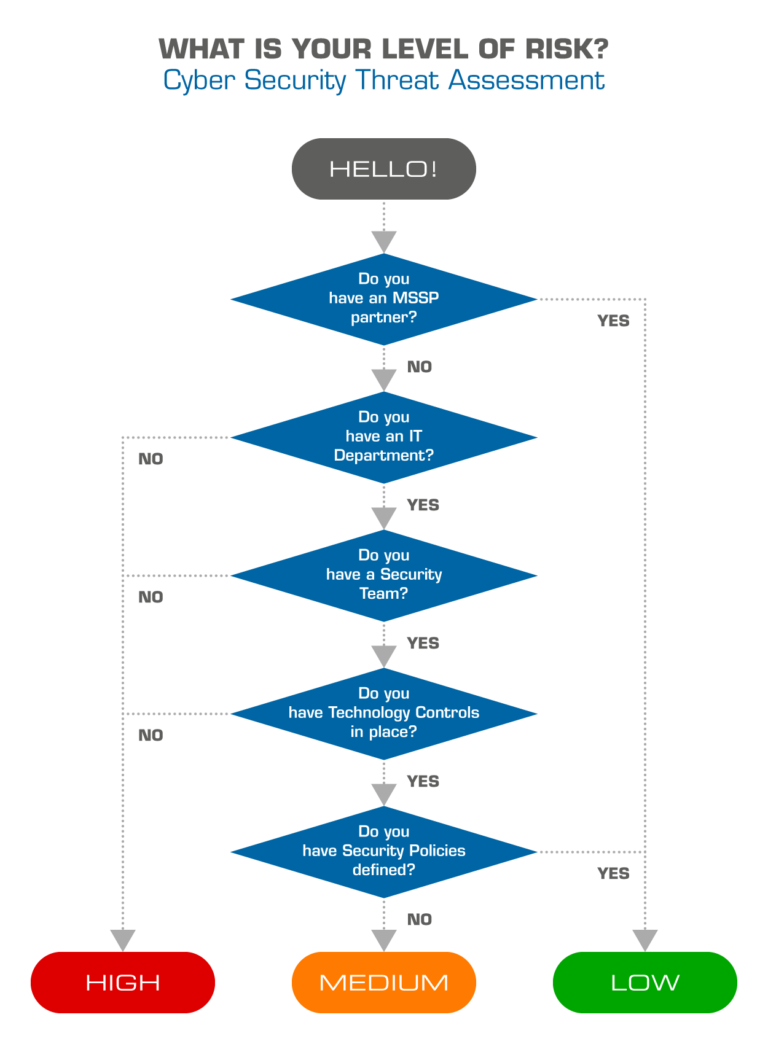
Explore the fascinating world of cyber security threat assessment: how to manage risk - wbm technologies through our remarkable gallery of vast arrays of photographs. featuring exceptional examples of computer, digital, and electronic. ideal for educational and commercial applications. Discover high-resolution cyber security threat assessment: how to manage risk - wbm technologies images optimized for various applications. Suitable for various applications including web design, social media, personal projects, and digital content creation All cyber security threat assessment: how to manage risk - wbm technologies images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Explore the versatility of our cyber security threat assessment: how to manage risk - wbm technologies collection for various creative and professional projects. Comprehensive tagging systems facilitate quick discovery of relevant cyber security threat assessment: how to manage risk - wbm technologies content. Regular updates keep the cyber security threat assessment: how to manage risk - wbm technologies collection current with contemporary trends and styles. Instant download capabilities enable immediate access to chosen cyber security threat assessment: how to manage risk - wbm technologies images. Advanced search capabilities make finding the perfect cyber security threat assessment: how to manage risk - wbm technologies image effortless and efficient.























![How to Perform a Cybersecurity Risk Assessment [5 Key Steps] | Syteca](https://mavink.com/images/loadingwhitetransparent.gif)