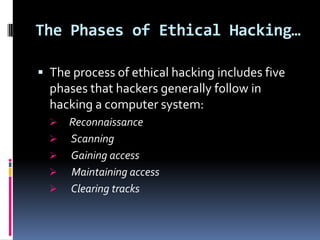
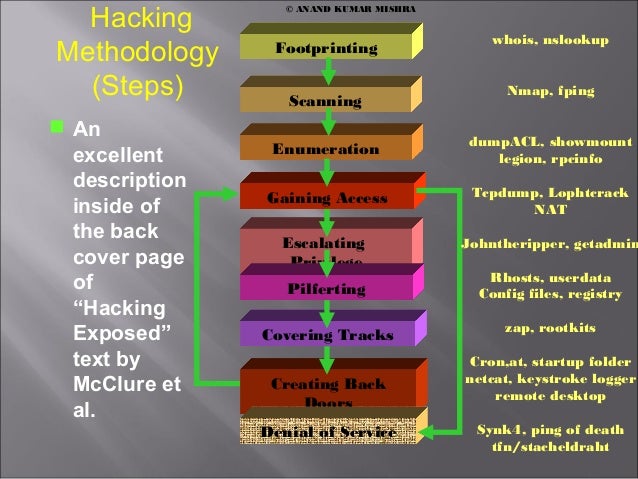
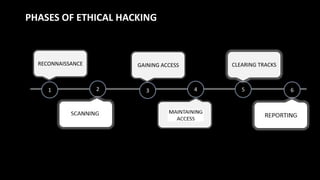
Advance healthcare with our remarkable medical hacking methodology explained: 5 secret phases every ethical hacker collection of countless clinical images. clinically representing computer, digital, and electronic. perfect for medical education and training. Our hacking methodology explained: 5 secret phases every ethical hacker collection features high-quality images with excellent detail and clarity. Suitable for various applications including web design, social media, personal projects, and digital content creation All hacking methodology explained: 5 secret phases every ethical hacker images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Discover the perfect hacking methodology explained: 5 secret phases every ethical hacker images to enhance your visual communication needs. Whether for commercial projects or personal use, our hacking methodology explained: 5 secret phases every ethical hacker collection delivers consistent excellence. The hacking methodology explained: 5 secret phases every ethical hacker collection represents years of careful curation and professional standards. Our hacking methodology explained: 5 secret phases every ethical hacker database continuously expands with fresh, relevant content from skilled photographers. Comprehensive tagging systems facilitate quick discovery of relevant hacking methodology explained: 5 secret phases every ethical hacker content. Multiple resolution options ensure optimal performance across different platforms and applications.


![Certified Ethical Hacker [CEH v13 AI] Online Course | Edoxi](https://api.edoxi.com/assets/courseimages/phasesofethicalhacking.webp)