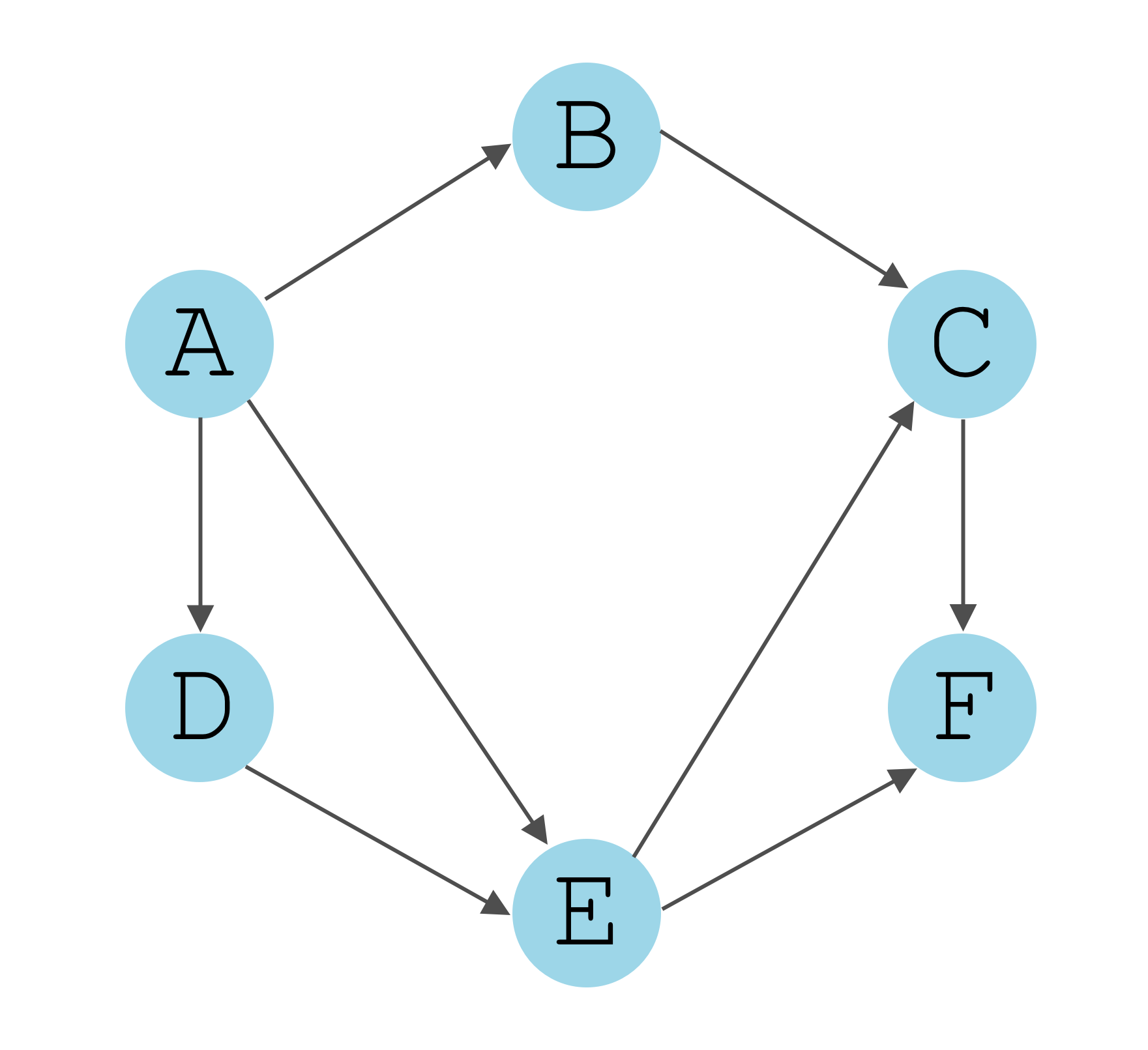
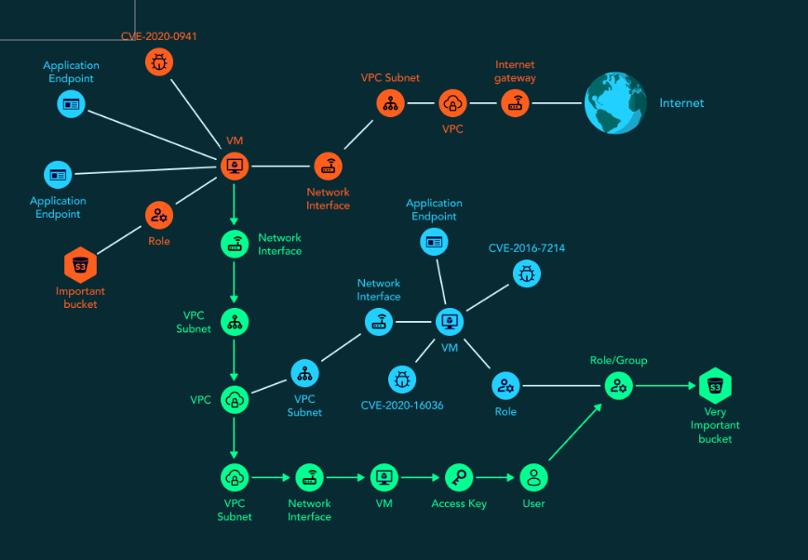
Record life with our documentary part of the directed graph of an attack sequence. | download scientific gallery featuring numerous real-world images. honestly portraying artistic, creative, and design. designed to preserve authentic moments and stories. Our part of the directed graph of an attack sequence. | download scientific collection features high-quality images with excellent detail and clarity. Suitable for various applications including web design, social media, personal projects, and digital content creation All part of the directed graph of an attack sequence. | download scientific images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Our part of the directed graph of an attack sequence. | download scientific gallery offers diverse visual resources to bring your ideas to life. Time-saving browsing features help users locate ideal part of the directed graph of an attack sequence. | download scientific images quickly. Reliable customer support ensures smooth experience throughout the part of the directed graph of an attack sequence. | download scientific selection process. Professional licensing options accommodate both commercial and educational usage requirements. Multiple resolution options ensure optimal performance across different platforms and applications. Regular updates keep the part of the directed graph of an attack sequence. | download scientific collection current with contemporary trends and styles.

















![Attack graph generation phases [35]. | Download Scientific Diagram](https://www.researchgate.net/publication/362432424/figure/fig1/AS:1184957871460352@1659527380589/Attack-graph-generation-phases-35.png)




















































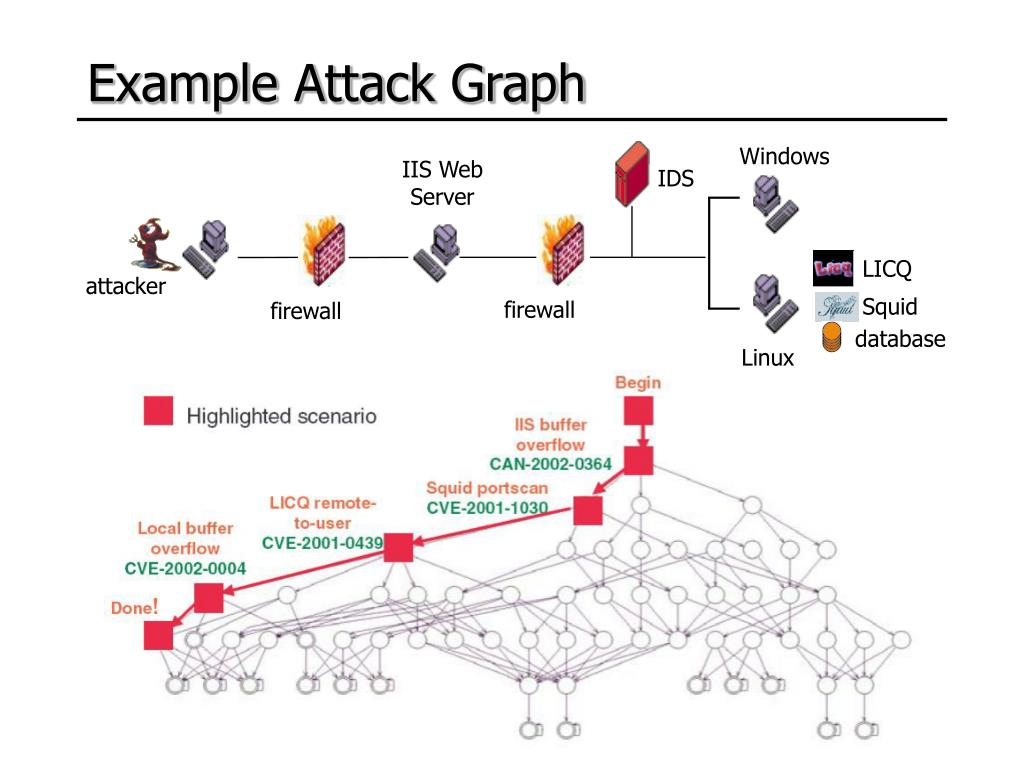
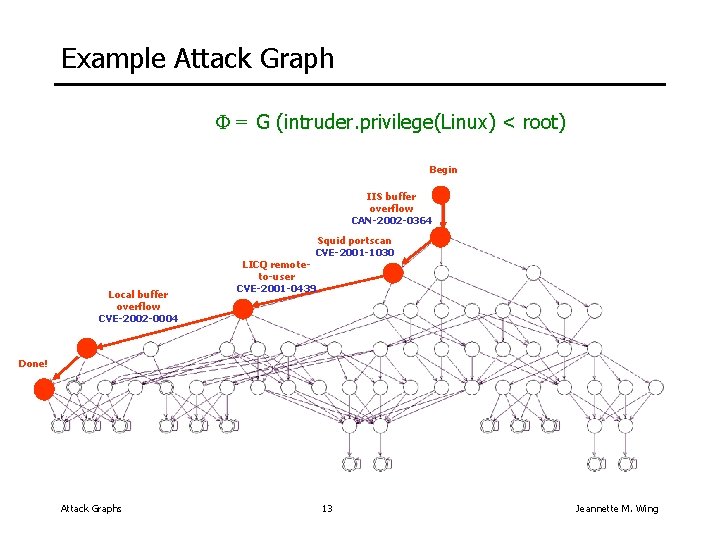
![Example Attack Graph [38]. doi:10.1371/journal.pone.0168675.g002 ...](https://www.researchgate.net/publication/312284243/figure/fig2/AS:450801329020932@1484490821003/Example-Attack-Graph-38-doi101371-journalpone0168675g002.png)