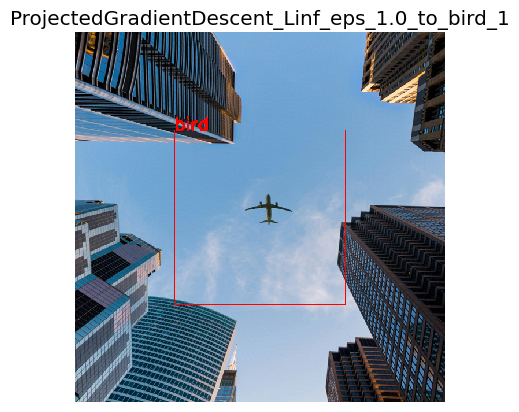
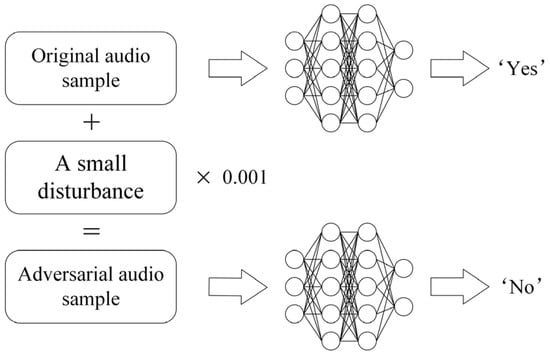
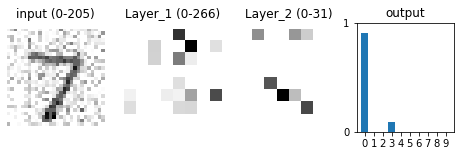
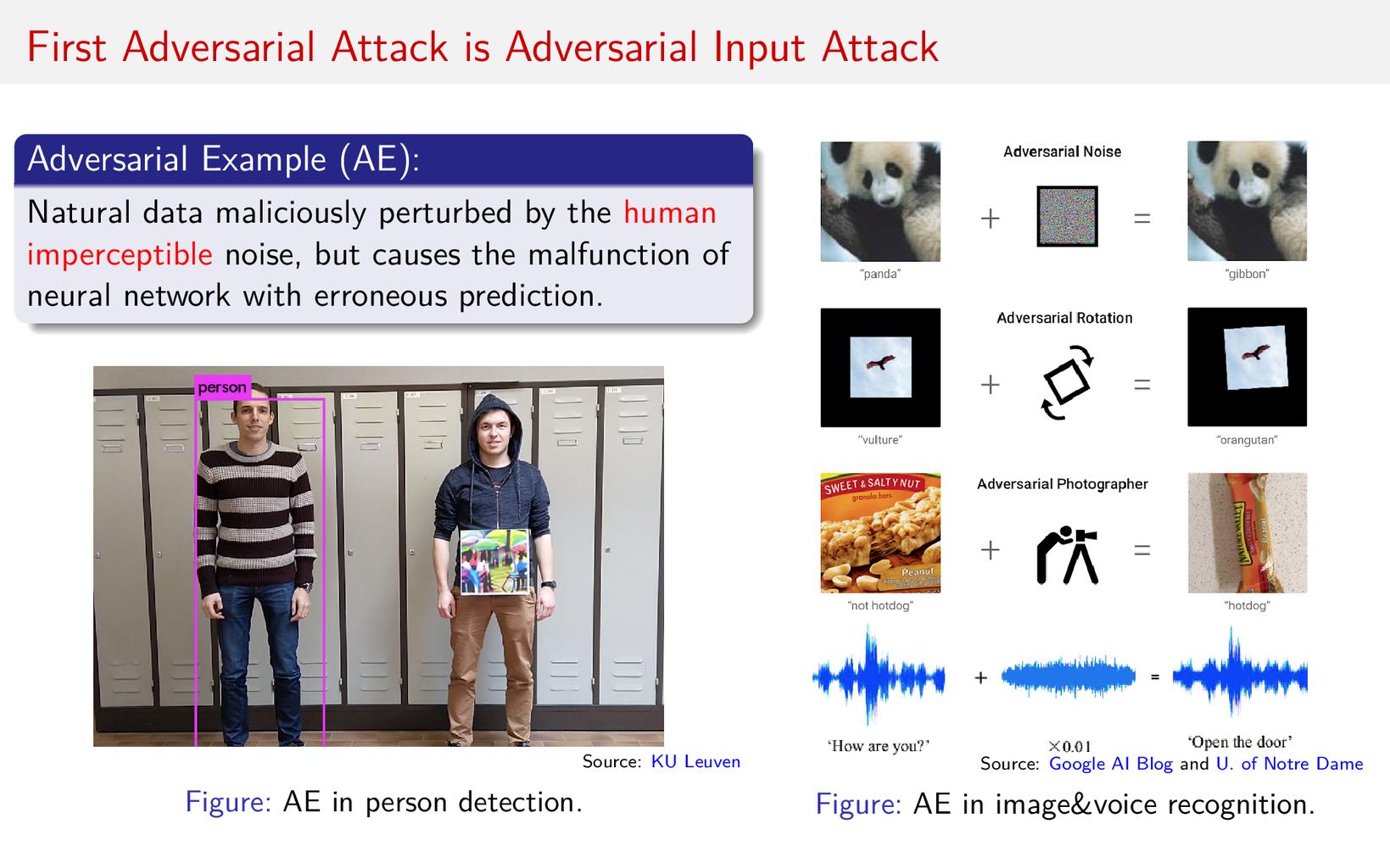
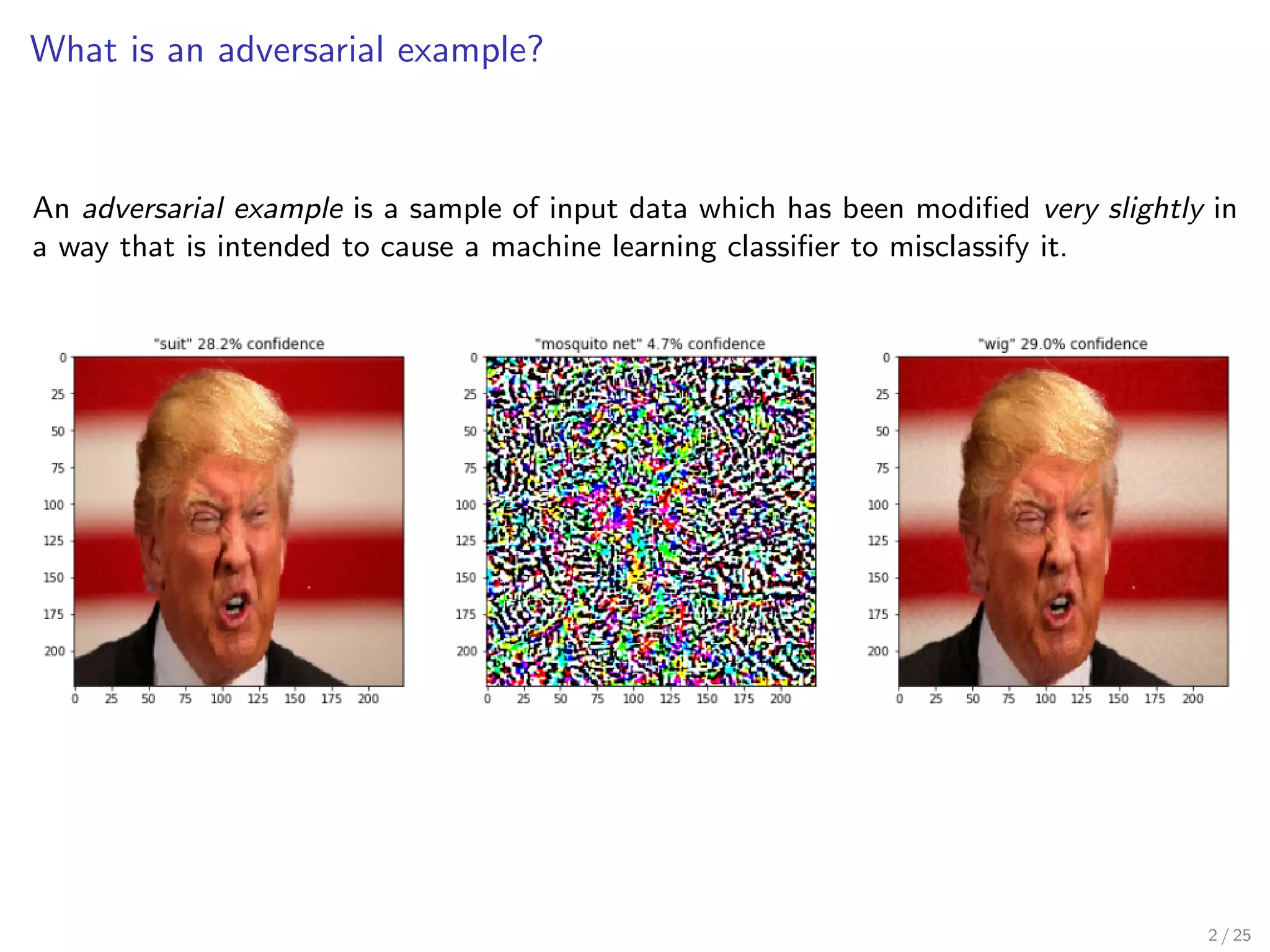
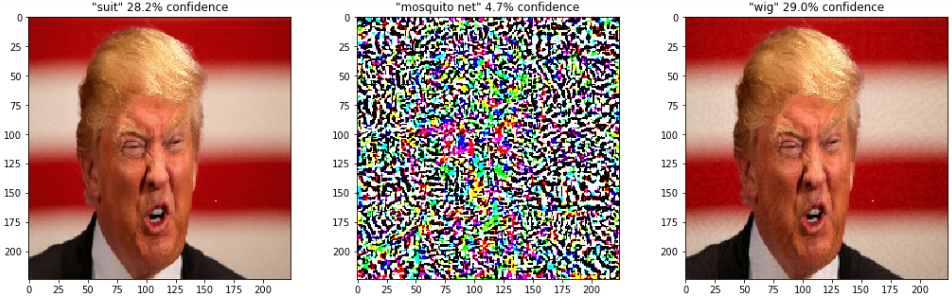
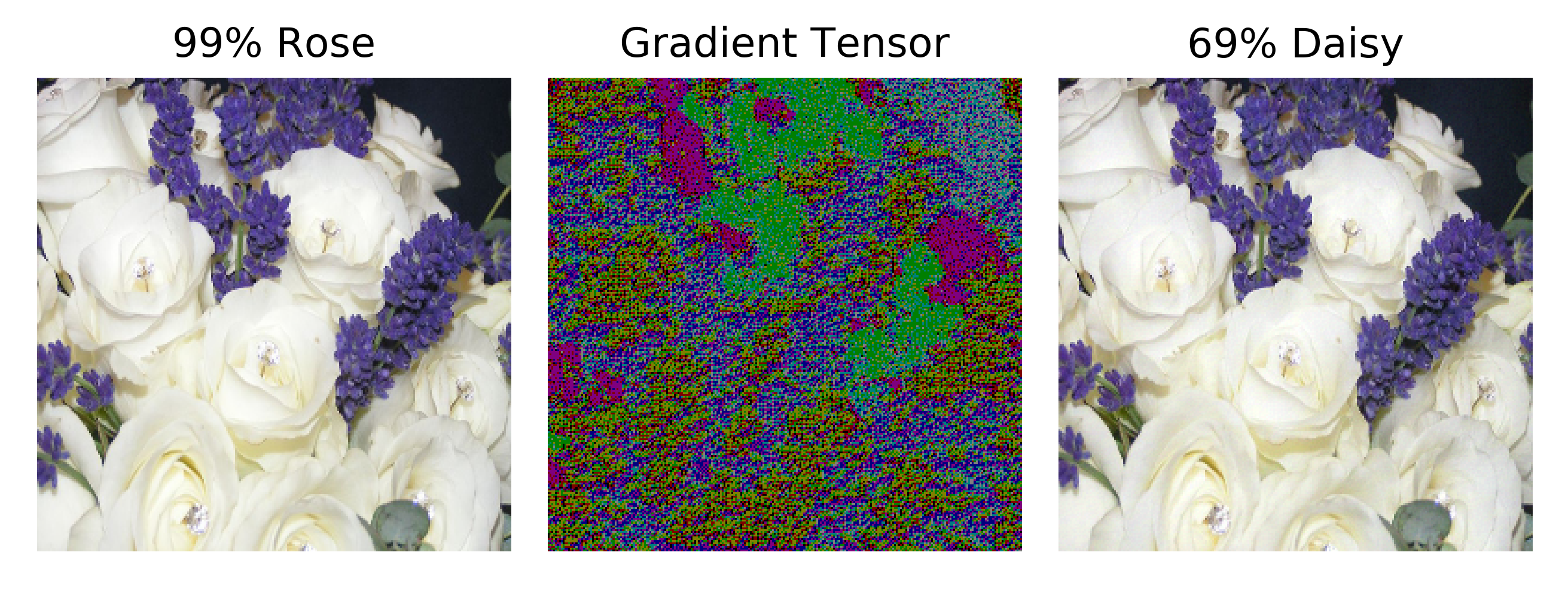
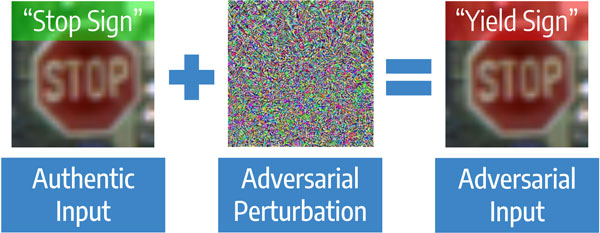
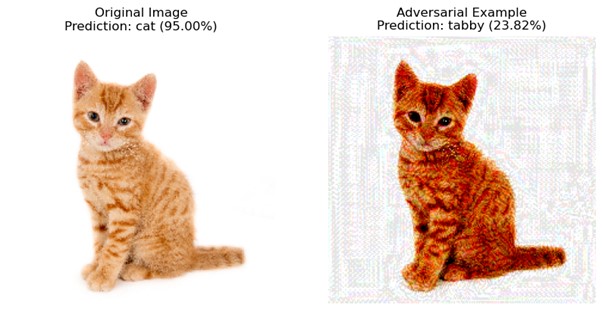
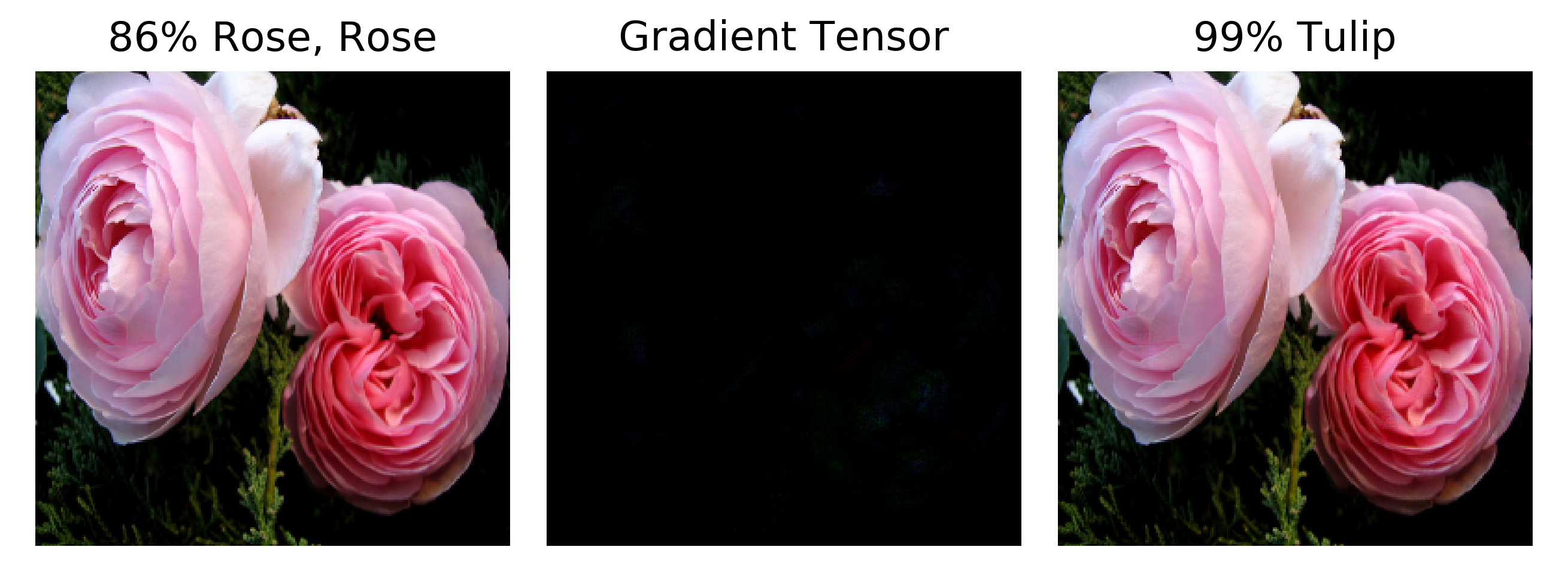
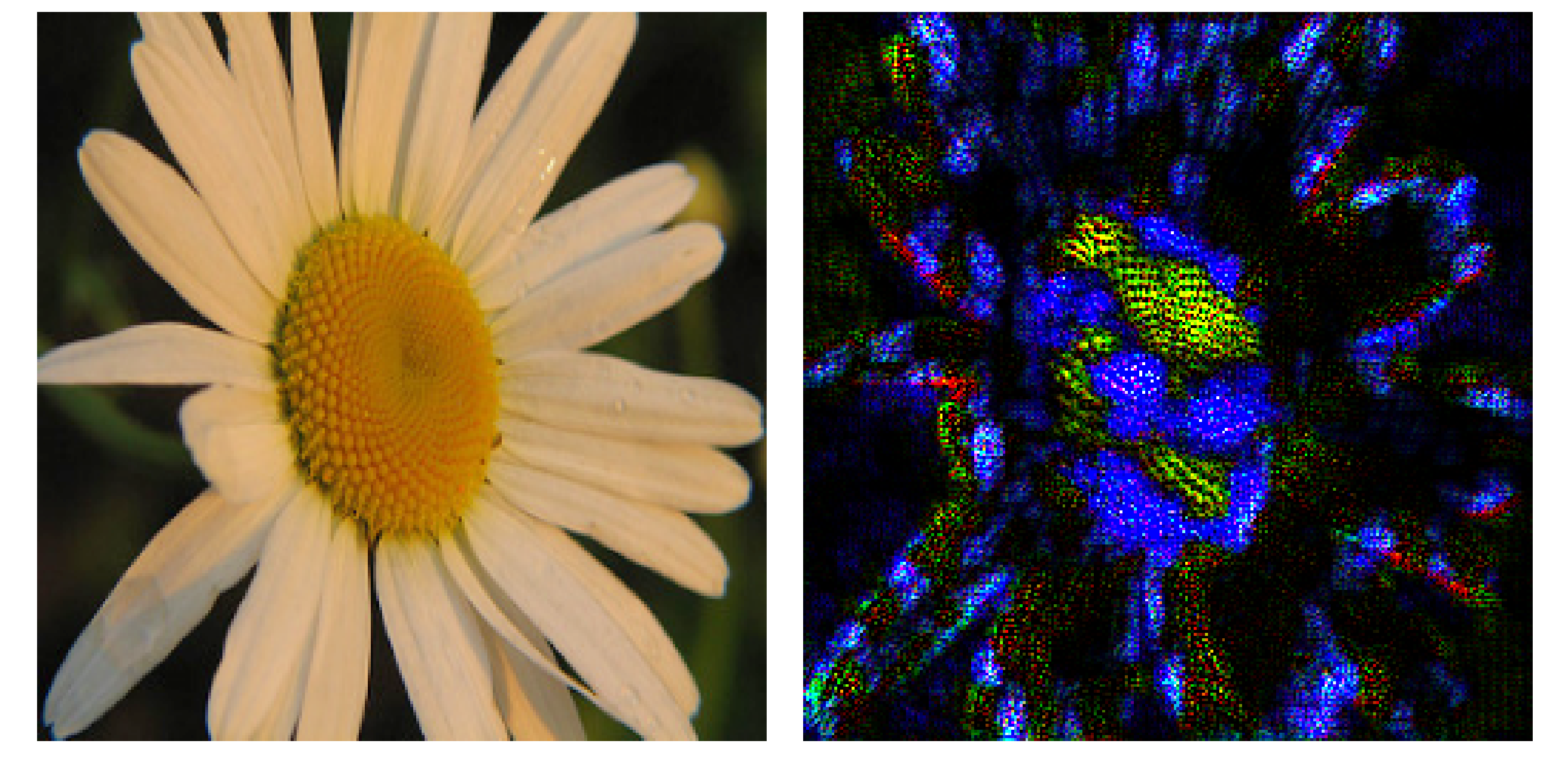
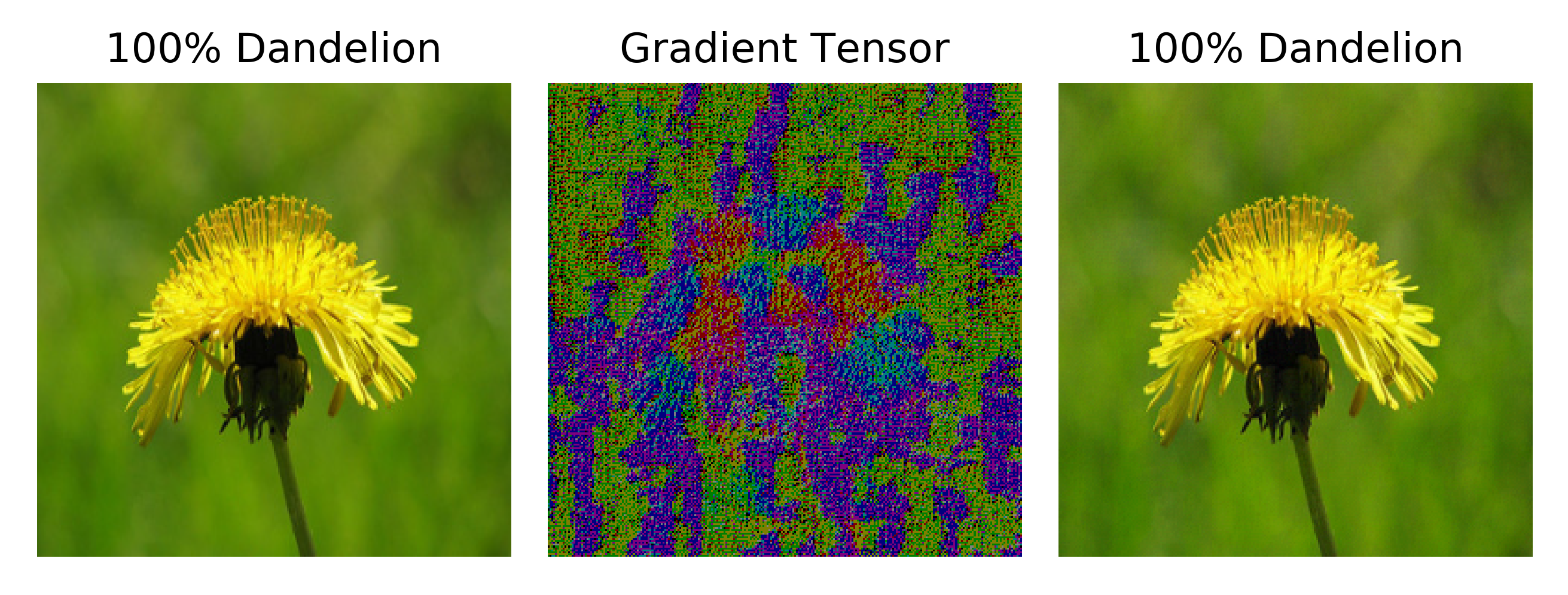
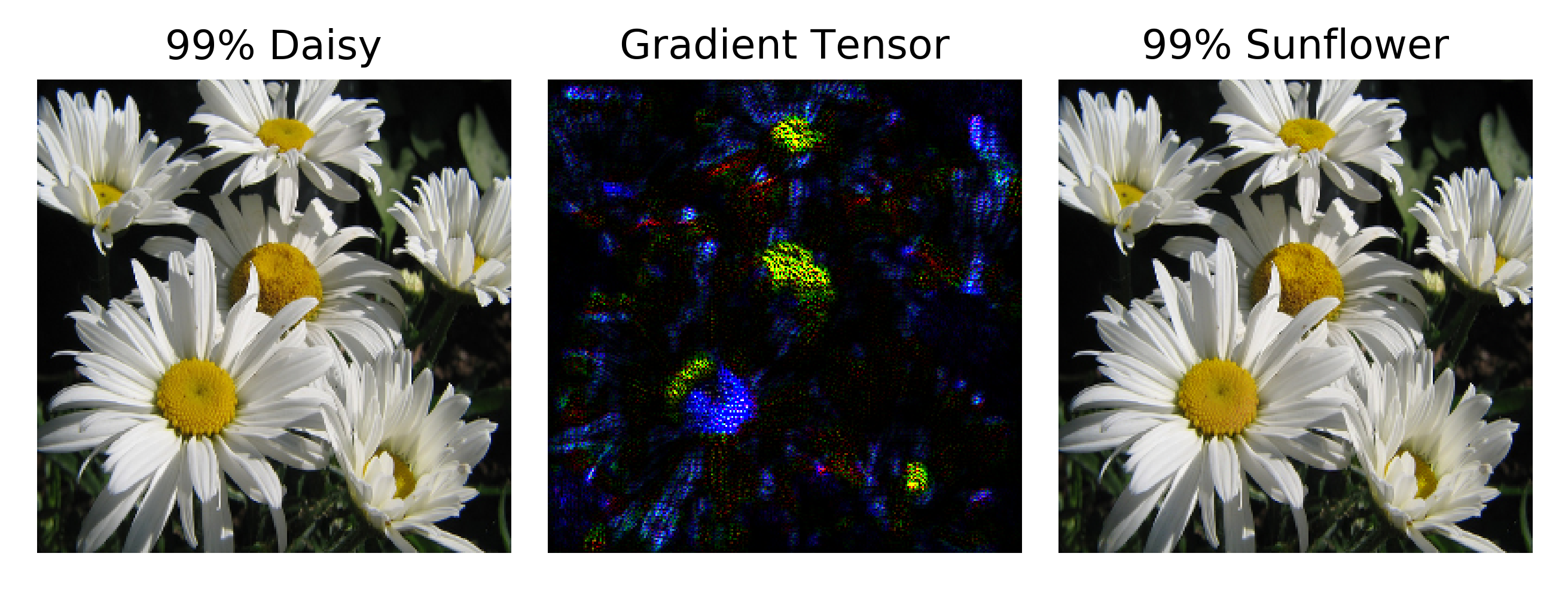
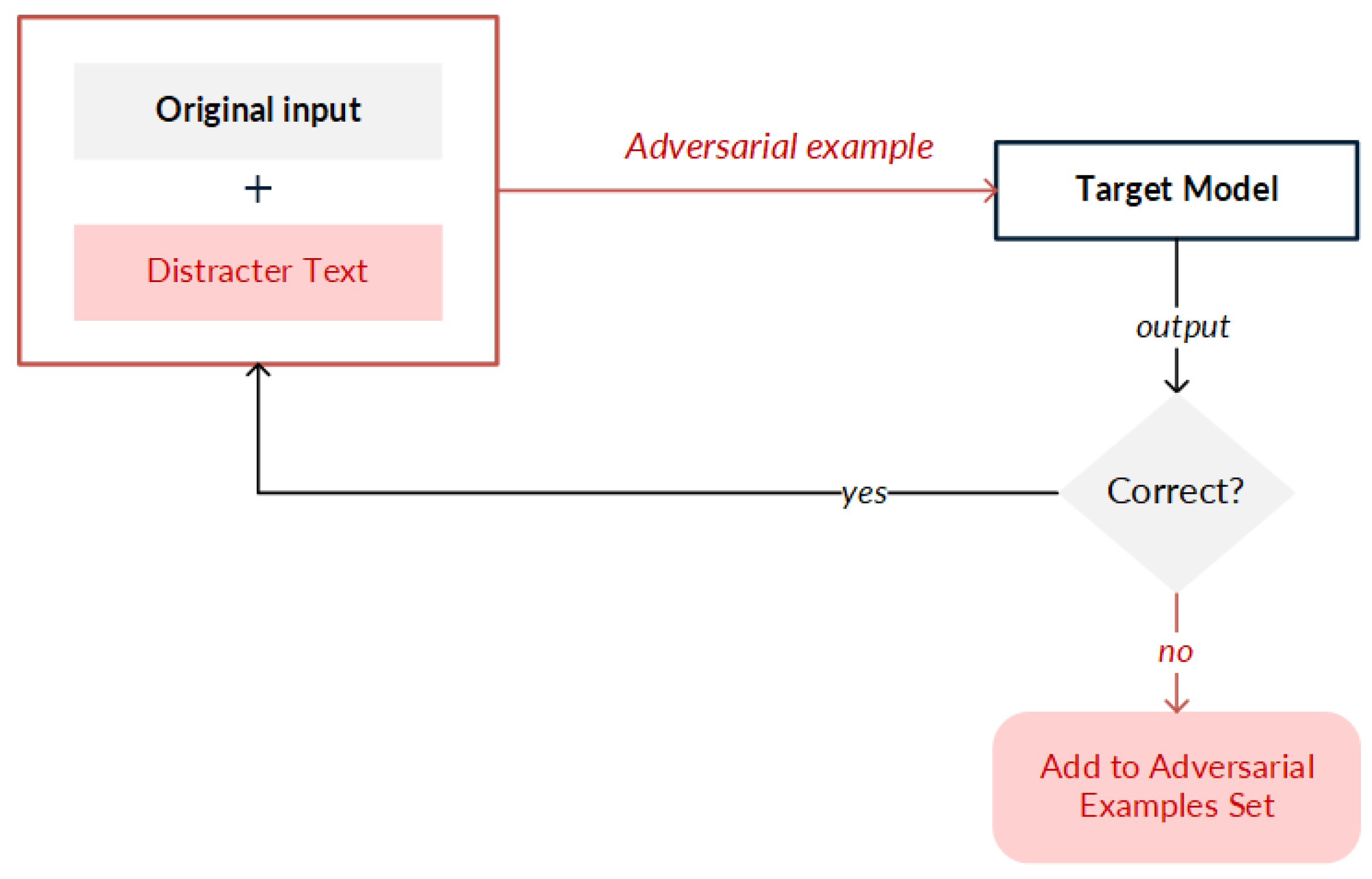
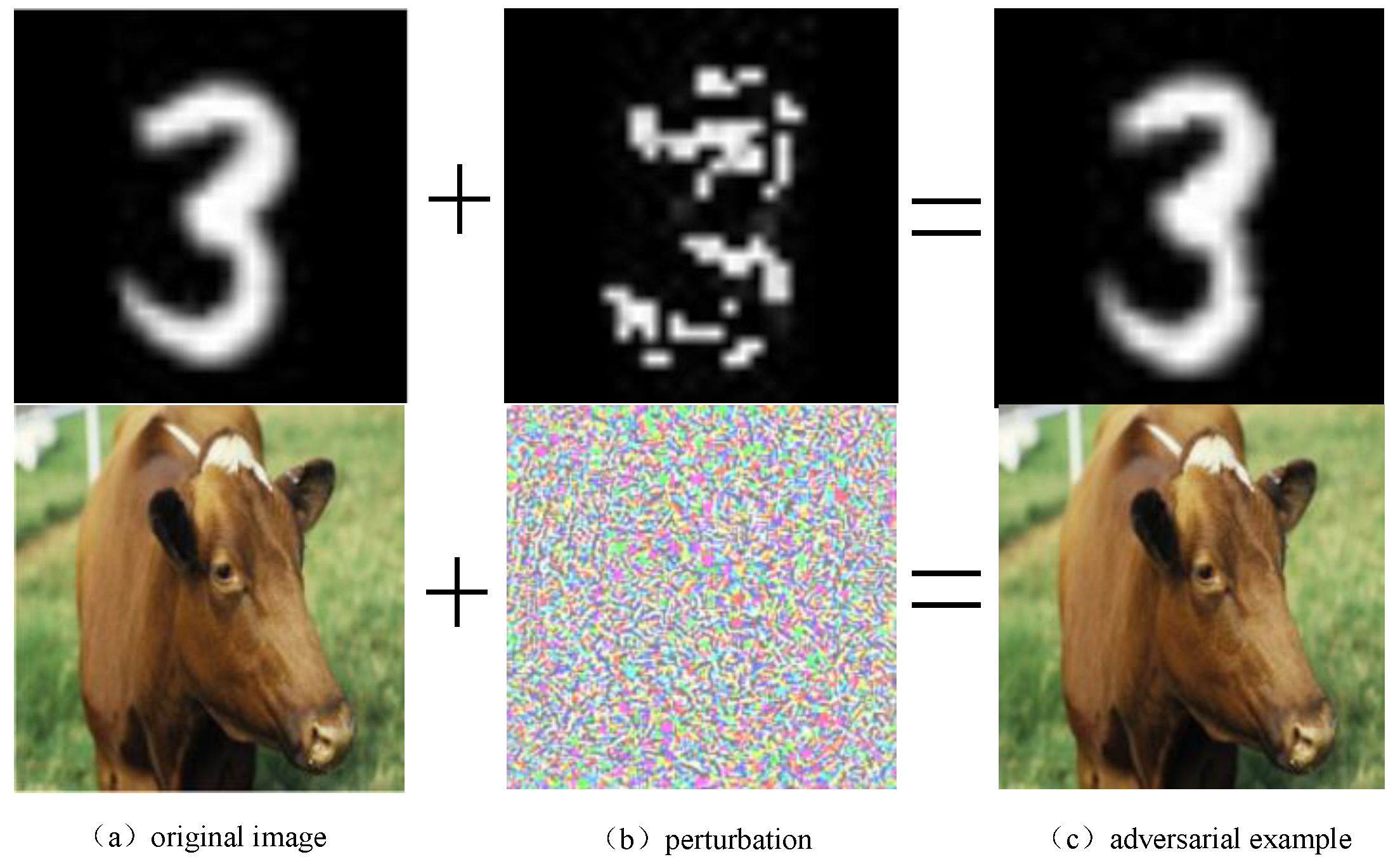
Experience the unique perspectives of [1] an adversarial example; an adversarial input, overlaid on a typical with our abstract gallery of countless images. featuring creative examples of computer, digital, and electronic. perfect for artistic and creative projects. Browse our premium [1] an adversarial example; an adversarial input, overlaid on a typical gallery featuring professionally curated photographs. Suitable for various applications including web design, social media, personal projects, and digital content creation All [1] an adversarial example; an adversarial input, overlaid on a typical images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Our [1] an adversarial example; an adversarial input, overlaid on a typical gallery offers diverse visual resources to bring your ideas to life. Diverse style options within the [1] an adversarial example; an adversarial input, overlaid on a typical collection suit various aesthetic preferences. The [1] an adversarial example; an adversarial input, overlaid on a typical archive serves professionals, educators, and creatives across diverse industries. Instant download capabilities enable immediate access to chosen [1] an adversarial example; an adversarial input, overlaid on a typical images. Multiple resolution options ensure optimal performance across different platforms and applications. Our [1] an adversarial example; an adversarial input, overlaid on a typical database continuously expands with fresh, relevant content from skilled photographers.
![[1] An adversarial example; an adversarial input, overlaid on a typical ... image.](https://www.researchgate.net/profile/Mouna-Dhaouadi/publication/338105748/figure/fig1/AS:838709389832192@1576975309667/1-An-adversarial-example-an-adversarial-input-overlaid-on-a-typical-image-can-cause_Q640.jpg)




















![[1] An adversarial example; an adversarial input, overlaid on a typical ...](https://www.researchgate.net/profile/Mouna-Dhaouadi/publication/338105748/figure/tbl1/AS:838709394042899@1576975310792/58_Q320.jpg)



![Adversarial example generated by FGSM from CIFAR10 [2] | Download ...](https://www.researchgate.net/profile/Jinhui-Chao/publication/362858642/figure/fig1/AS:11431281080259660@1661223905205/Adversarial-example-generated-by-FGSM-from-CIFAR10-2.png)
![[2211.15030] Imperceptible Adversarial Attack via Invertible Neural ...](https://ar5iv.labs.arxiv.org/html/2211.15030/assets/image/first_look_final.png)


![Adversarial example in input and representation space [145]. While the ...](https://www.researchgate.net/publication/343568307/figure/download/fig1/AS:923187600699392@1597116484031/Adversarial-example-in-input-and-representation-space-145-While-the-two-pictures-of.jpg)

![Adversarial example defense based on image reconstruction [PeerJ]](https://dfzljdn9uc3pi.cloudfront.net/2021/cs-811/1/fig-1-full.png)




![Adversarial example generated by FGSM from CIFAR10 [2] | Download ...](https://www.researchgate.net/profile/Jinhui-Chao/publication/362858642/figure/fig4/AS:11431281081157220@1661560716290/Adversarial-examples-generated-by-FGSM_Q640.jpg)














![[Adversarial Examples] Adversarial T-shirt / Inivisibility Cloak ...](https://pic3.zhimg.com/v2-c3971855aa57cc43a44ed657b943220e_b.png)
![Adversarial Example Crafting Framework [20] | Download Scientific Diagram](https://www.researchgate.net/publication/364627291/figure/fig1/AS:11431281092073238@1666690175091/Adversarial-Example-Crafting-Framework-20.png)
![[1605.07277] Transferability in Machine Learning: from Phenomena to ...](https://ar5iv.labs.arxiv.org/html/1605.07277/assets/x1.png)
![Adversarial example in input and representation space [145]. While the ...](https://www.researchgate.net/publication/343568307/figure/fig1/AS:923187600699392@1597116484031/Adversarial-example-in-input-and-representation-space-145-While-the-two-pictures-of_Q640.jpg)









![Adversarial example generated by FGSM from CIFAR10 [2] | Download ...](https://www.researchgate.net/profile/Jinhui-Chao/publication/362858642/figure/fig3/AS:11431281081176544@1661560684052/Adversarial-examples-generated-by-Szegedys-L-BFGS_Q640.jpg)