Token Based Lock
Elevate your brand with our commercial Token Based Lock gallery featuring numerous business-ready images. optimized for commercial use with photography, images, and pictures. ideal for corporate communications and branding. The Token Based Lock collection maintains consistent quality standards across all images. Suitable for various applications including web design, social media, personal projects, and digital content creation All Token Based Lock images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Discover the perfect Token Based Lock images to enhance your visual communication needs. Time-saving browsing features help users locate ideal Token Based Lock images quickly. The Token Based Lock archive serves professionals, educators, and creatives across diverse industries. Whether for commercial projects or personal use, our Token Based Lock collection delivers consistent excellence. Diverse style options within the Token Based Lock collection suit various aesthetic preferences. Our Token Based Lock database continuously expands with fresh, relevant content from skilled photographers. Reliable customer support ensures smooth experience throughout the Token Based Lock selection process. Professional licensing options accommodate both commercial and educational usage requirements. Each image in our Token Based Lock gallery undergoes rigorous quality assessment before inclusion.















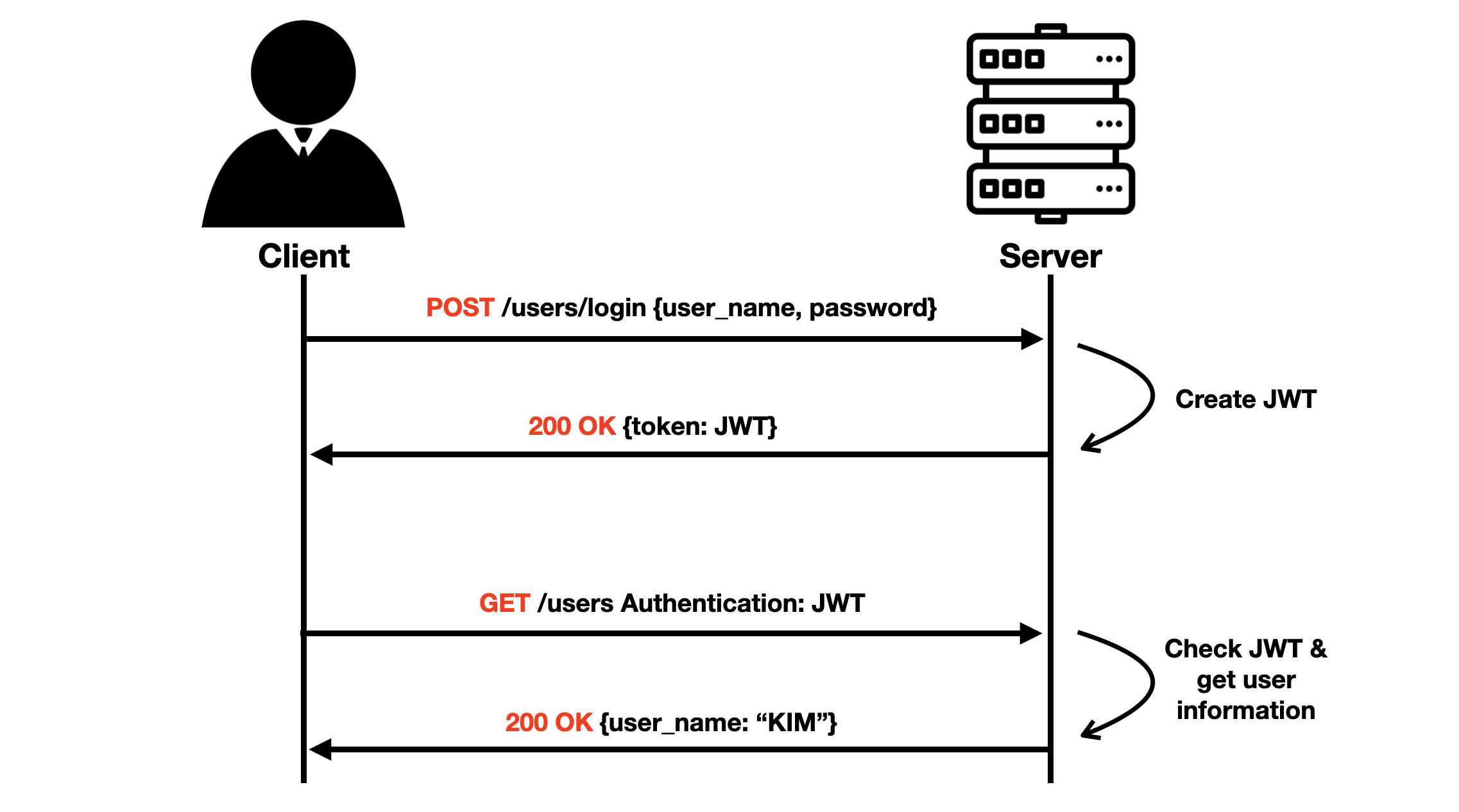


















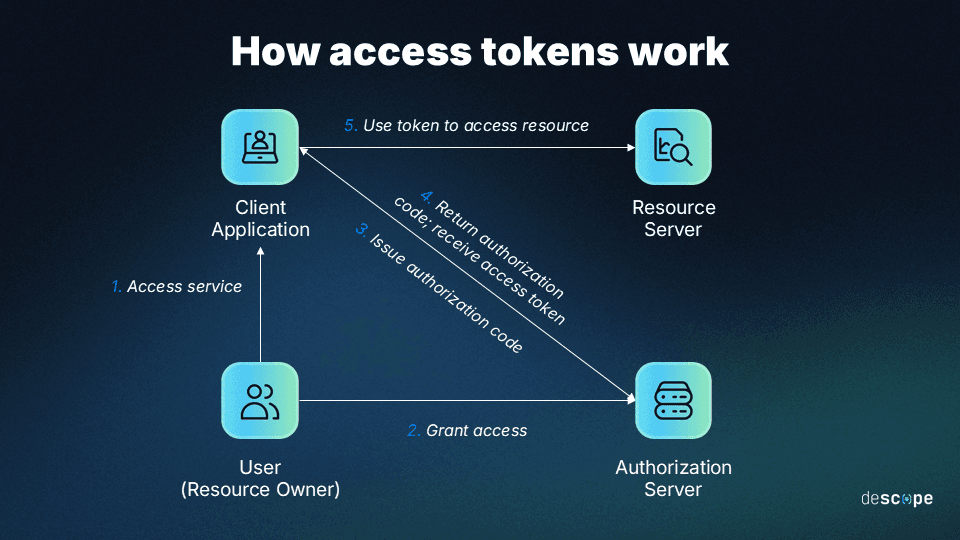
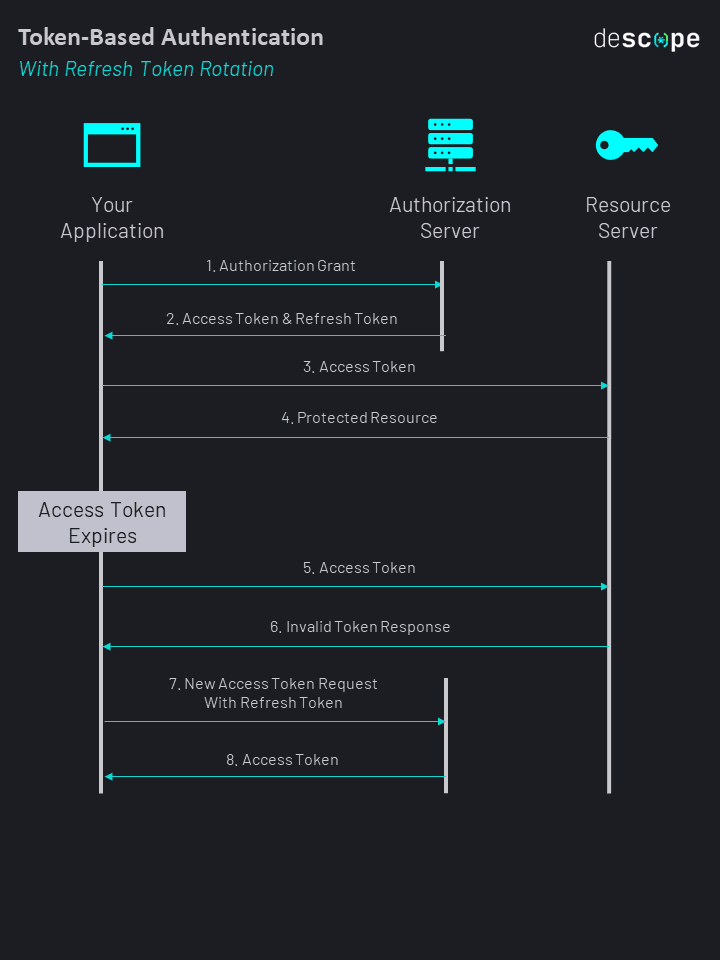
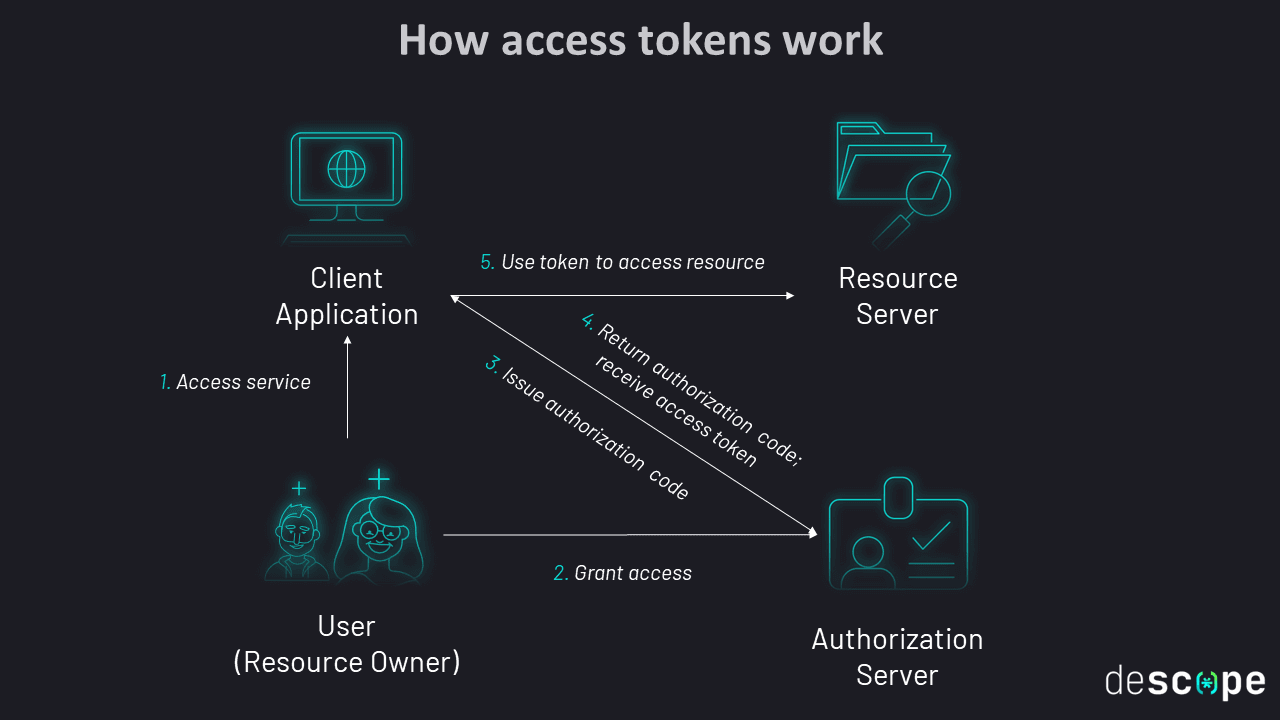






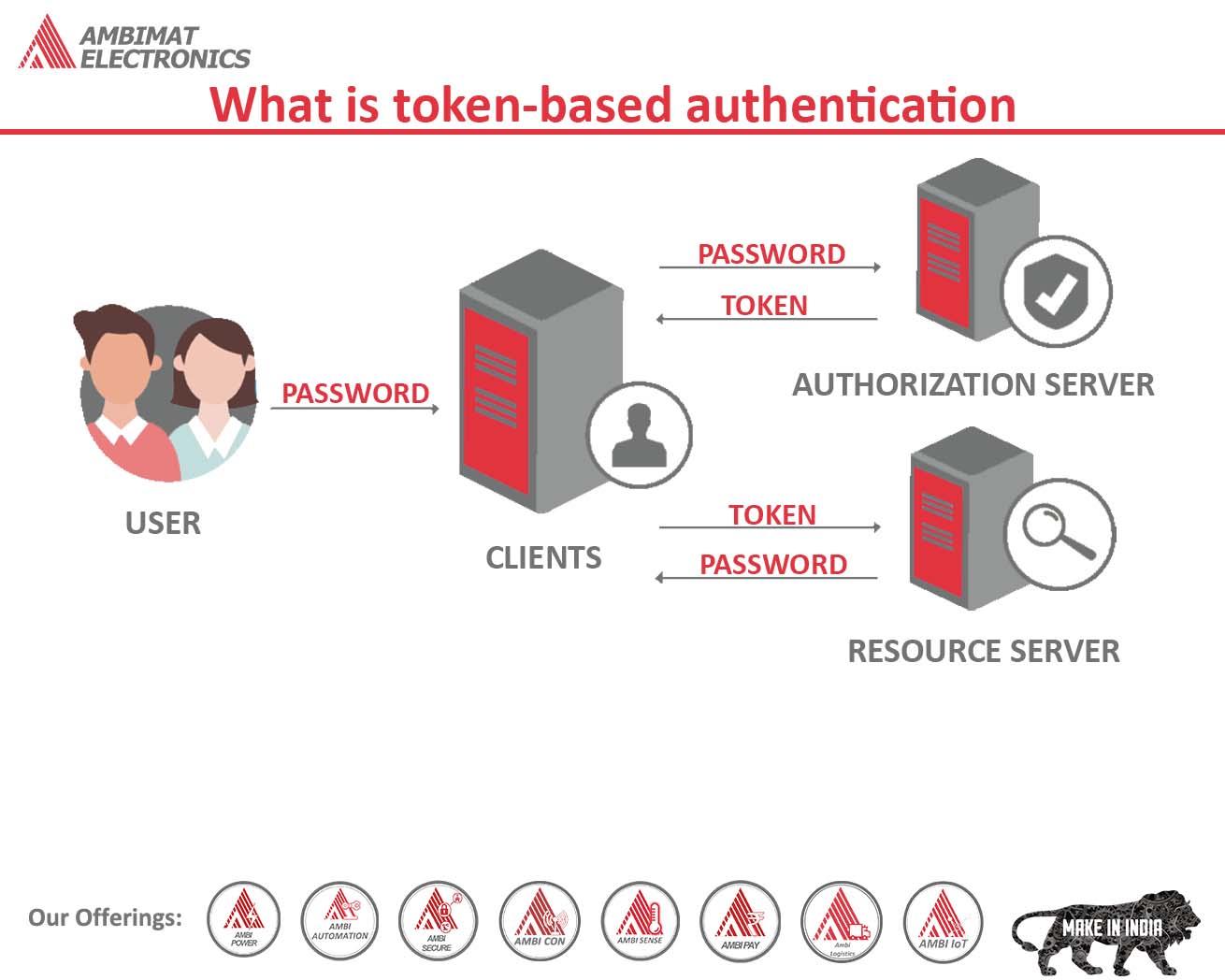






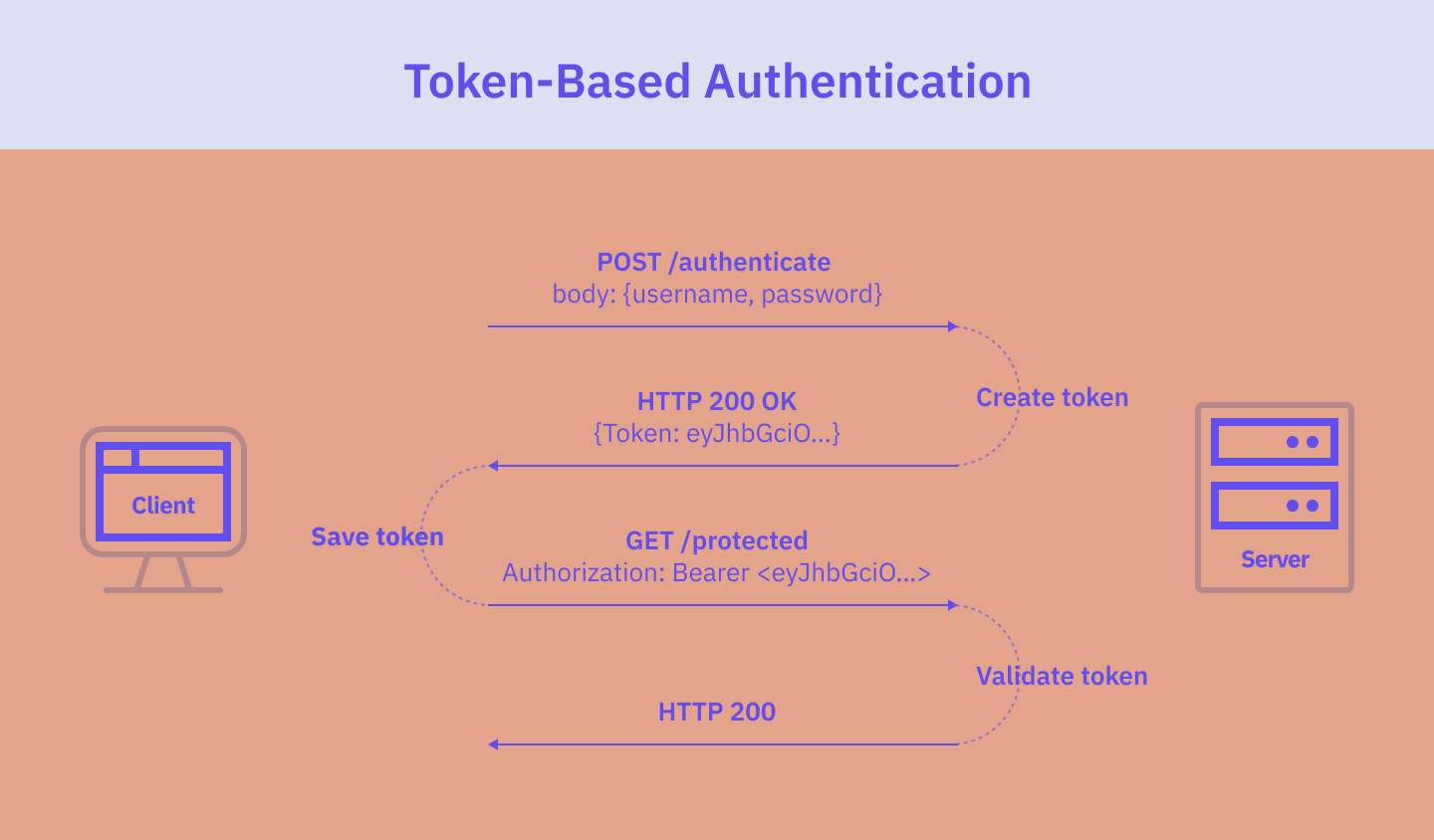
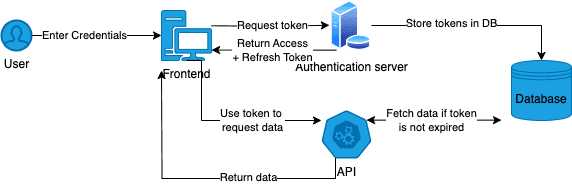





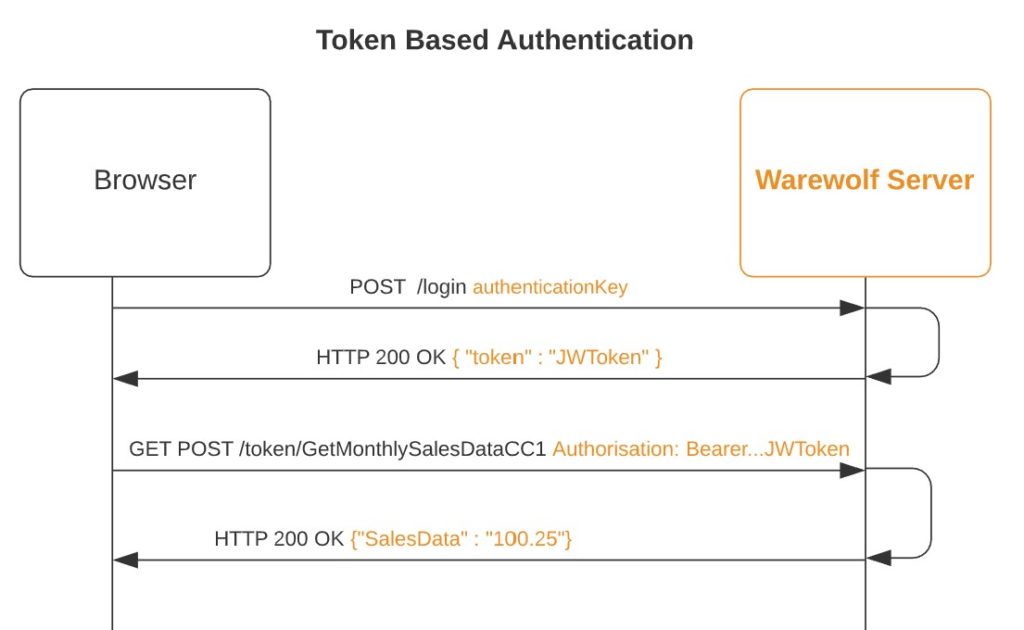

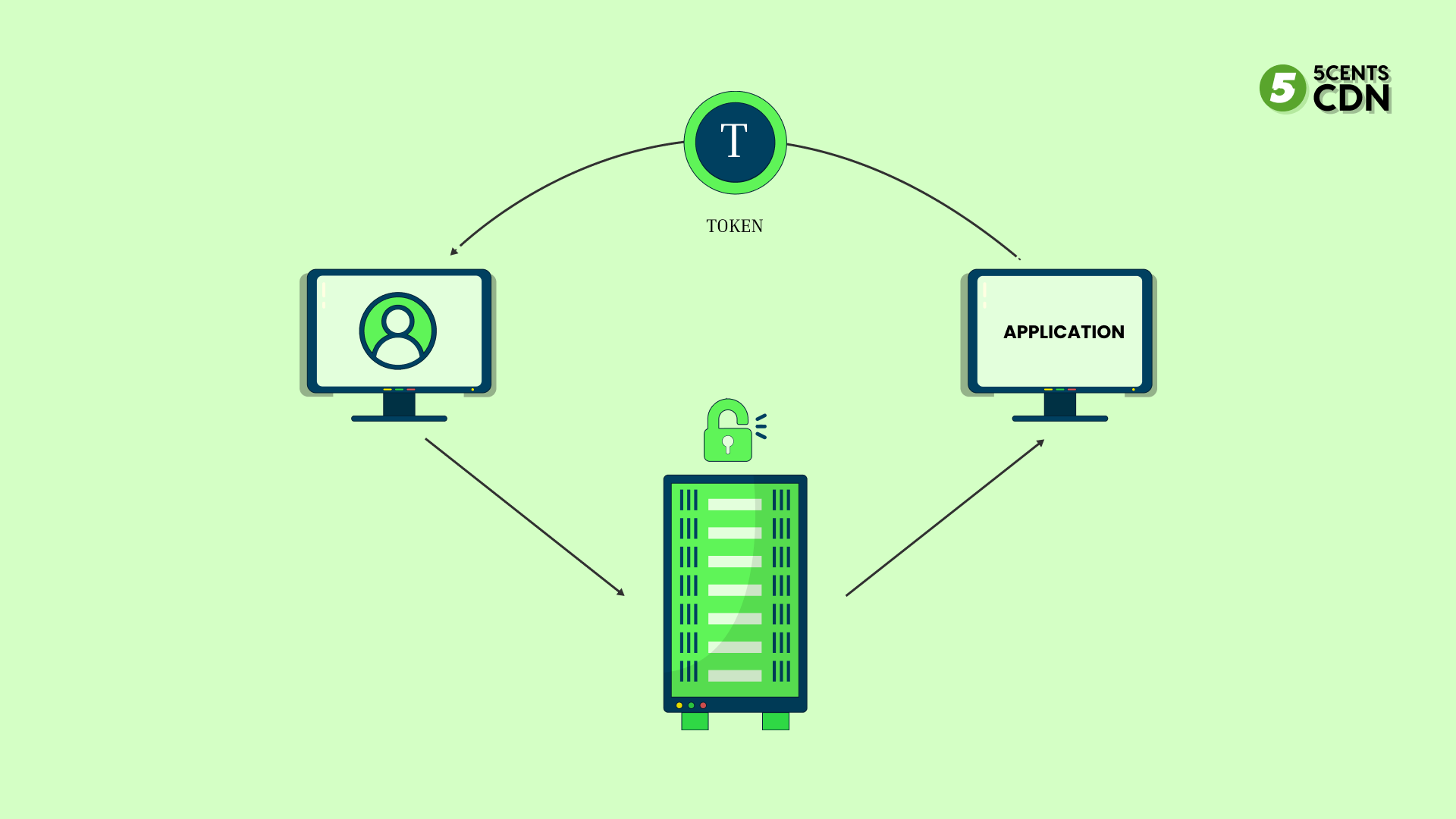






![Token-based Authentication [9] Fig 4. Illustrates the mechanism for ...](https://www.researchgate.net/profile/Taimoor-Syed/publication/370544582/figure/fig3/AS:11431281155962426@1683295954670/Token-based-Authentication-9-Fig-4-Illustrates-the-mechanism-for-token-based.png)







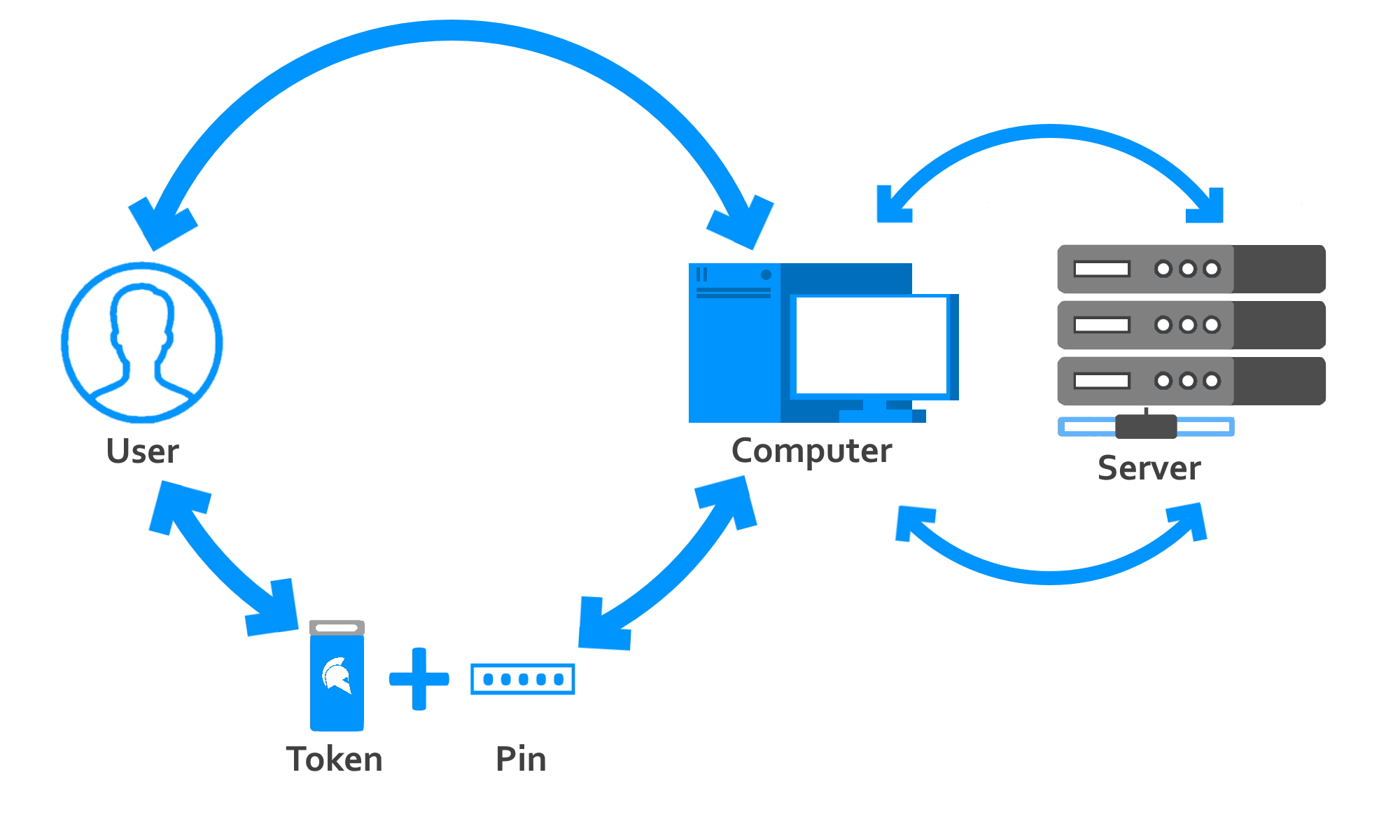



![Token-based Authentication [9] Fig 4. Illustrates the mechanism for ...](https://www.researchgate.net/profile/Taimoor-Syed/publication/370544582/figure/fig3/AS:11431281155962426@1683295954670/Token-based-Authentication-9-Fig-4-Illustrates-the-mechanism-for-token-based_Q320.jpg)