Spear Organization Strategy
Express style with our stunning fashion Spear Organization Strategy collection of hundreds of trendy images. stylishly presenting photography, images, and pictures. perfect for fashion marketing and magazines. Our Spear Organization Strategy collection features high-quality images with excellent detail and clarity. Suitable for various applications including web design, social media, personal projects, and digital content creation All Spear Organization Strategy images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Explore the versatility of our Spear Organization Strategy collection for various creative and professional projects. Professional licensing options accommodate both commercial and educational usage requirements. Advanced search capabilities make finding the perfect Spear Organization Strategy image effortless and efficient. Multiple resolution options ensure optimal performance across different platforms and applications. Cost-effective licensing makes professional Spear Organization Strategy photography accessible to all budgets. Time-saving browsing features help users locate ideal Spear Organization Strategy images quickly. Regular updates keep the Spear Organization Strategy collection current with contemporary trends and styles. Diverse style options within the Spear Organization Strategy collection suit various aesthetic preferences. Each image in our Spear Organization Strategy gallery undergoes rigorous quality assessment before inclusion. Comprehensive tagging systems facilitate quick discovery of relevant Spear Organization Strategy content.

























.webp)























.png?format=1000w)
























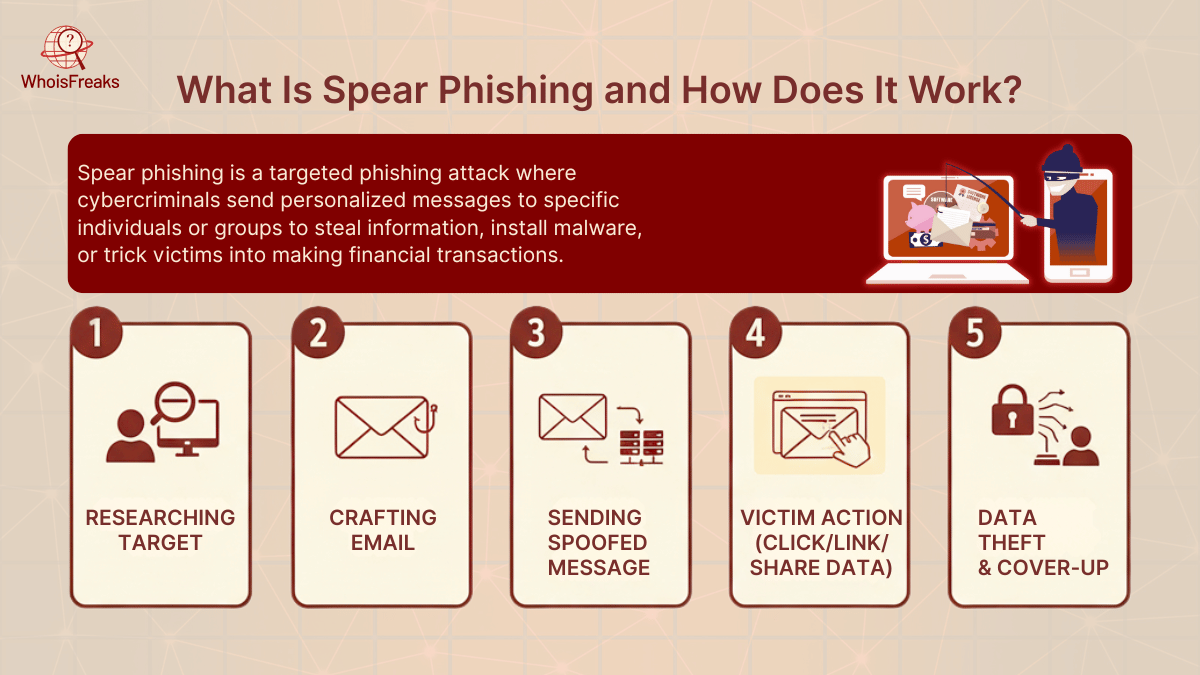
![[Spear Phishing] Understanding Targeted Attacks and Protection Strategies](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjqlKCQ-C8s80pRmyfZykc9hZxTAYuRSg0cNAyAc0OZxI-OVm40WvTYJep78lNN8C8RIFFDe6qxbBfLwvWJaDYFHWN1H5M-obmUYemx4xsGq69mQkflkAyU4ZfKQv91H_t5JaAPvQtbUkTYZfZIX_qKu42m0X2o4Na6YcZCN9jx8uQdjGwMqZwLeKh-jok/s1080/002.png)

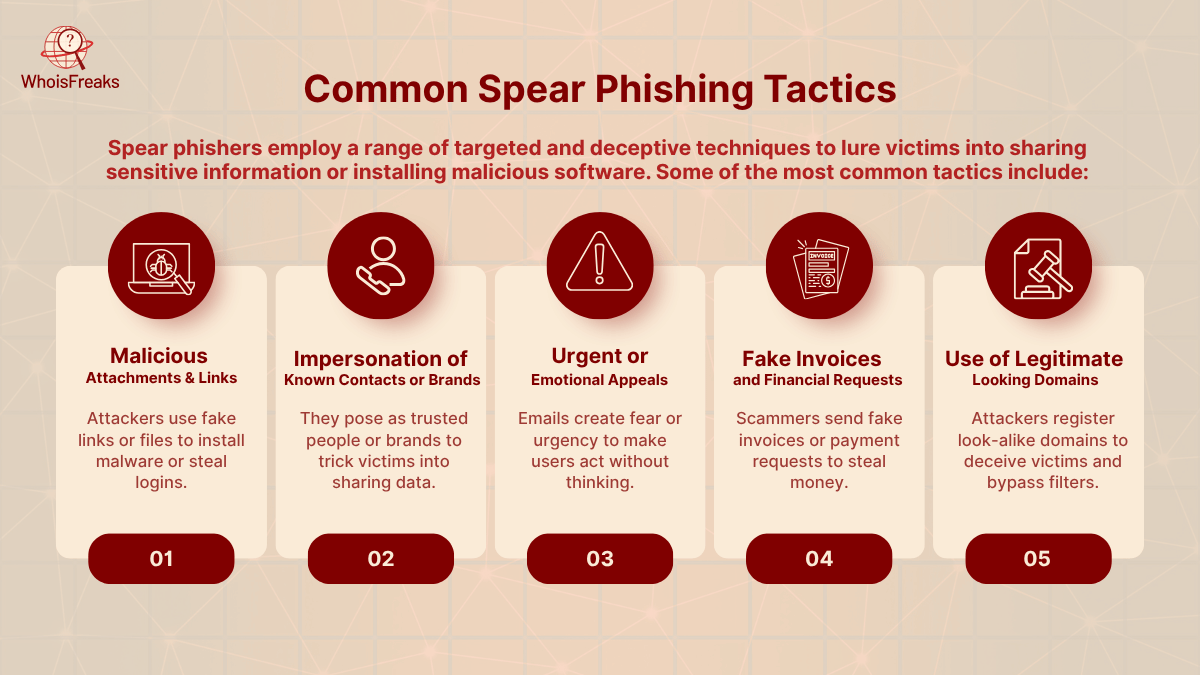
![[Spear Phishing] Understanding Targeted Attacks and Protection Strategies](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEi63O0kzF3-uxVHPD4XEMBNAXE8h_Y8LkRWh85oGt348e_HtKJlomd6eQY9UIpuPJatdPeEvlWk15fnI7_FCqsxsfnX3V-d0mY4pI_aZMYOT-hLXg3dq_Zj3uZ-moC-8jy3UoIZIbSCMJ3bmvxwgUoD1jvEXIcPFqnI6StvOQ0GhZeJDZ6GFwKlPTYIW_E/s1080/005.png)






![[Spear Phishing] Understanding Targeted Attacks and Protection Strategies](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEg1v7605QqH_aI3ivJAdVHrS0CLaxdET7jebUb0IgjzSKOPM24CmOE33nQ4_MmJxHvaOhSlwZzhzeKzVXw4YFt0eFSt7l2k1l1HpTs9wGEG9BIdzYihqnZpuihQSPyMRzYN2IJaHHN7I3rhvTFdJ8wamg_fsWnO3jUjgK0Xh9dR2JDrgL-zOxq7u5k49vM/s1080/003.png)