Security Development Approach
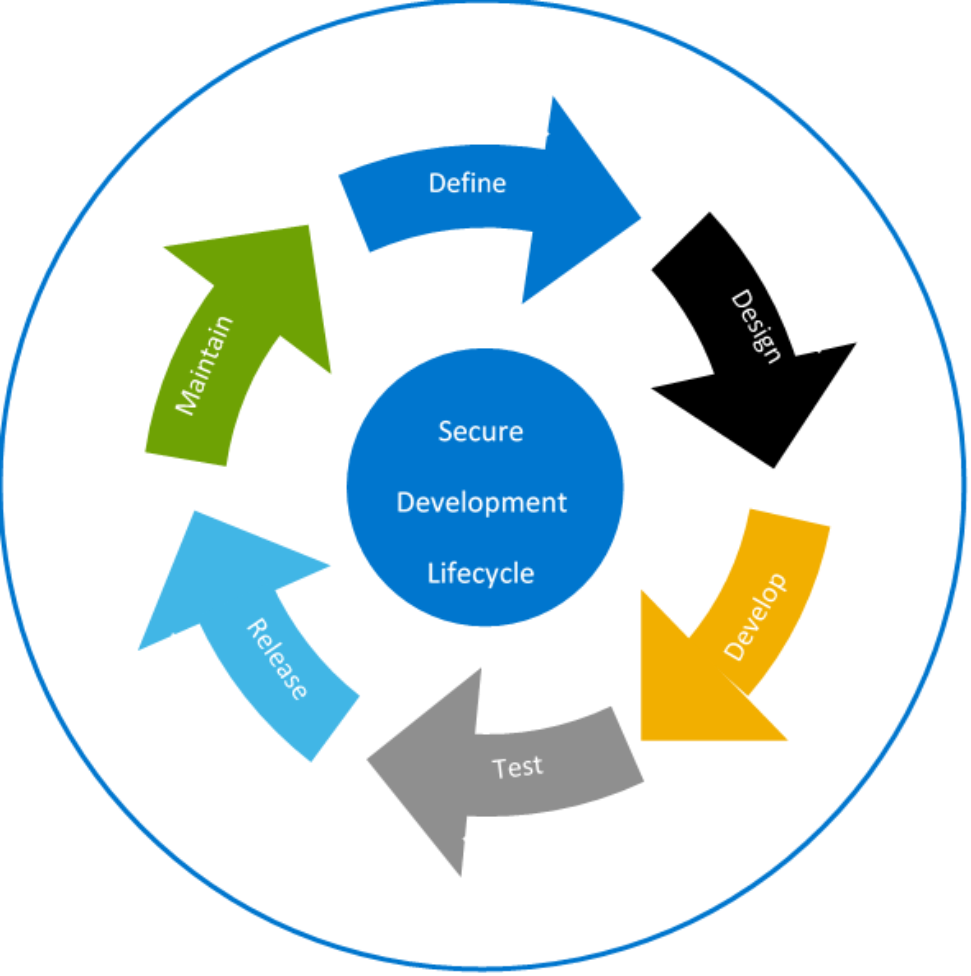
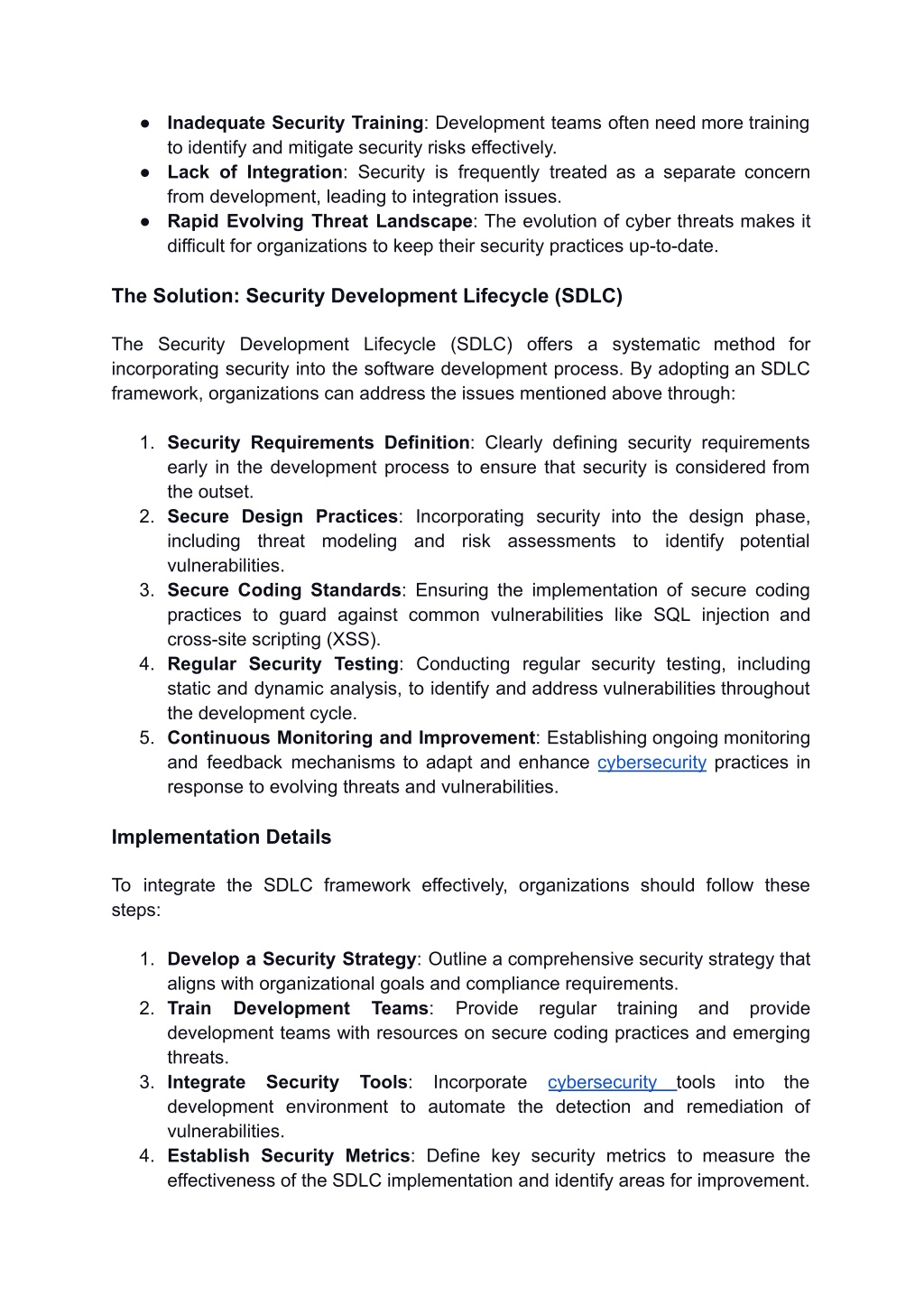
Experience the unique perspectives of Security Development Approach with our abstract gallery of substantial collections of images. showcasing the artistic expression of photography, images, and pictures. designed to inspire imagination and creativity. Each Security Development Approach image is carefully selected for superior visual impact and professional quality. Suitable for various applications including web design, social media, personal projects, and digital content creation All Security Development Approach images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Discover the perfect Security Development Approach images to enhance your visual communication needs. Time-saving browsing features help users locate ideal Security Development Approach images quickly. Professional licensing options accommodate both commercial and educational usage requirements. Whether for commercial projects or personal use, our Security Development Approach collection delivers consistent excellence. Regular updates keep the Security Development Approach collection current with contemporary trends and styles. Each image in our Security Development Approach gallery undergoes rigorous quality assessment before inclusion. The Security Development Approach collection represents years of careful curation and professional standards. Multiple resolution options ensure optimal performance across different platforms and applications. Cost-effective licensing makes professional Security Development Approach photography accessible to all budgets.










.jpg)

![Development Phases and Security Actions [35]. | Download Scientific Diagram](https://www.researchgate.net/publication/334028100/figure/tbl1/AS:773886832566279@1561520407933/Development-Phases-and-Security-Actions-35.png)
.webp)




































![What is Threat Modeling? All you need to know [OverView] | Updated 2025](https://www.acte.in/wp-content/uploads/2020/07/PASTA.png)






![[Cybersecurity Architecture] Strategic Planning & Roadmap Examples ...](https://i.postimg.cc/SRLg9s4M/Cyber-Security-Architecture-Roadmap-Development-Process.png)