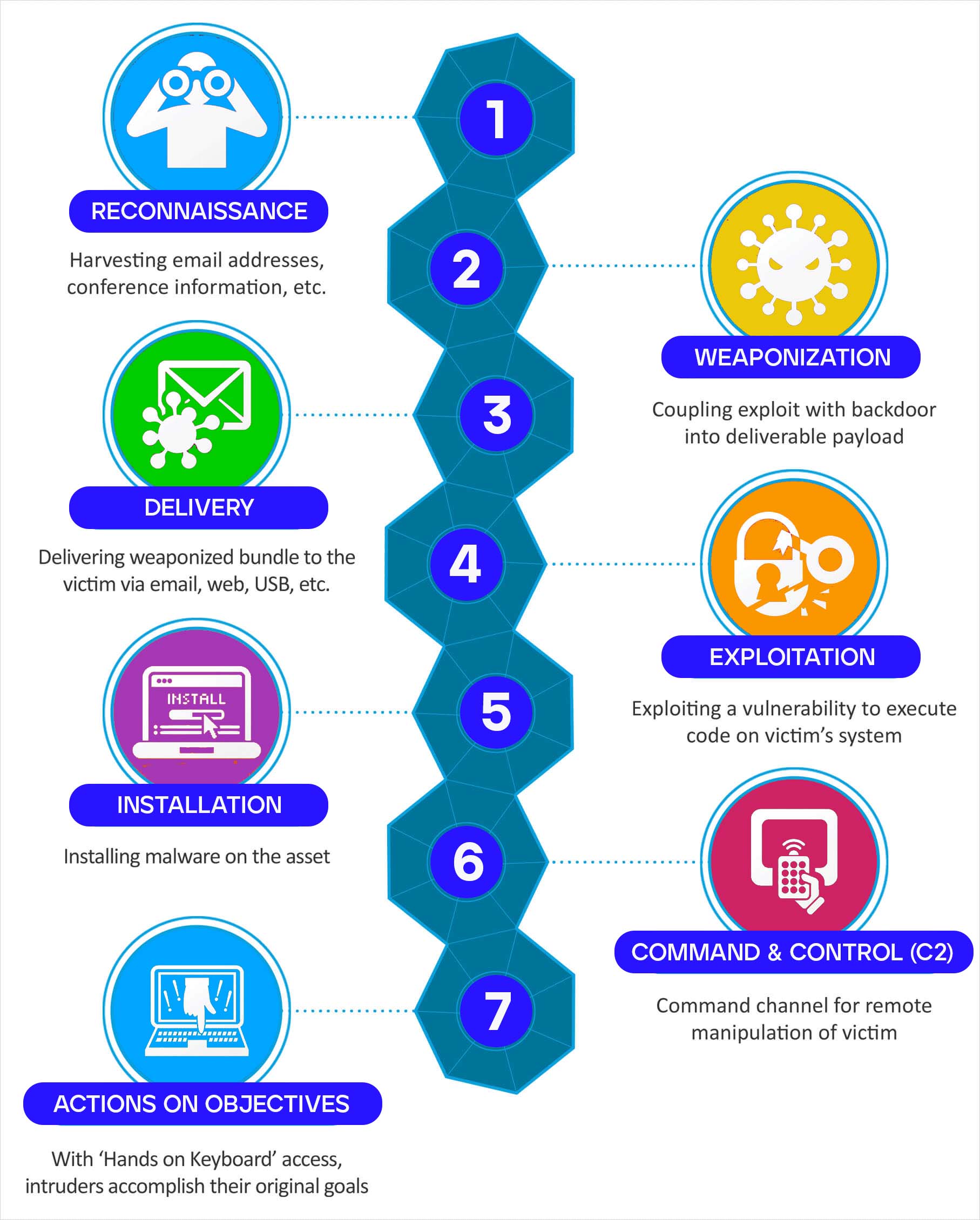
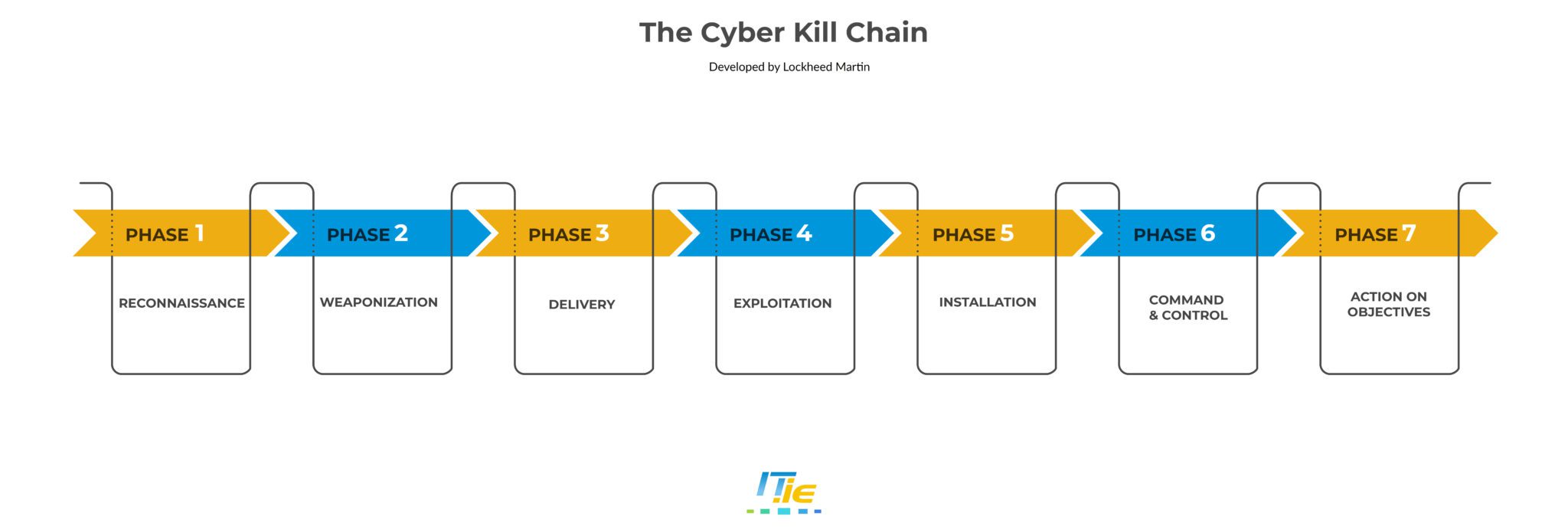
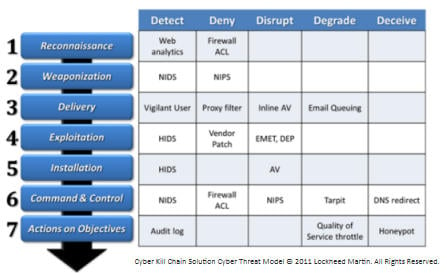
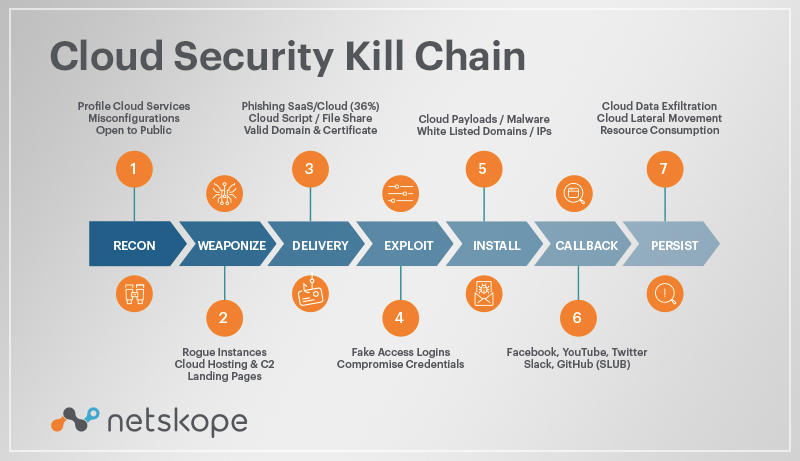
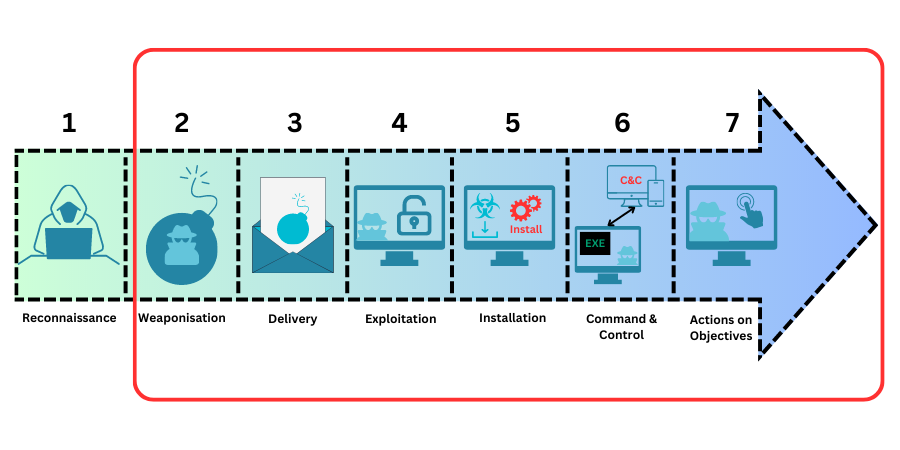
Lockheed Kill Chain
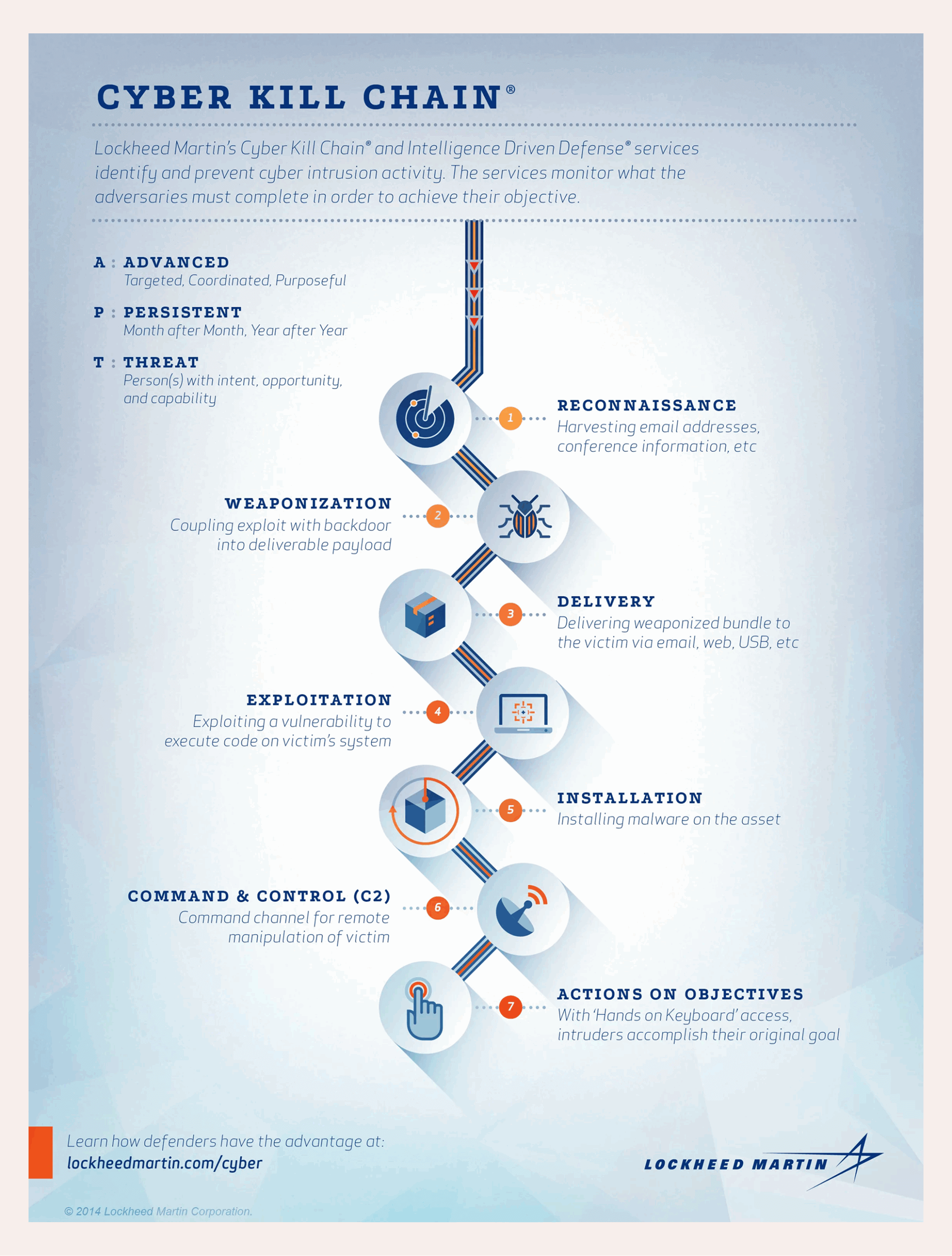
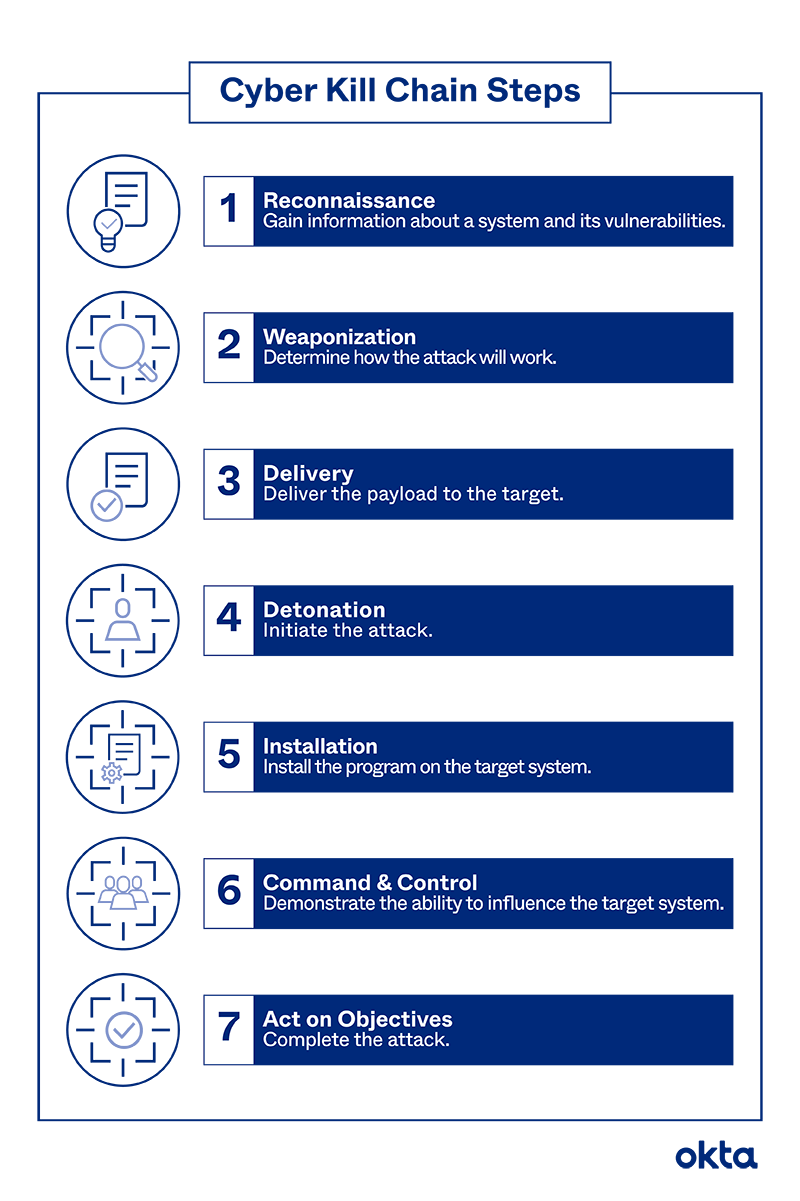
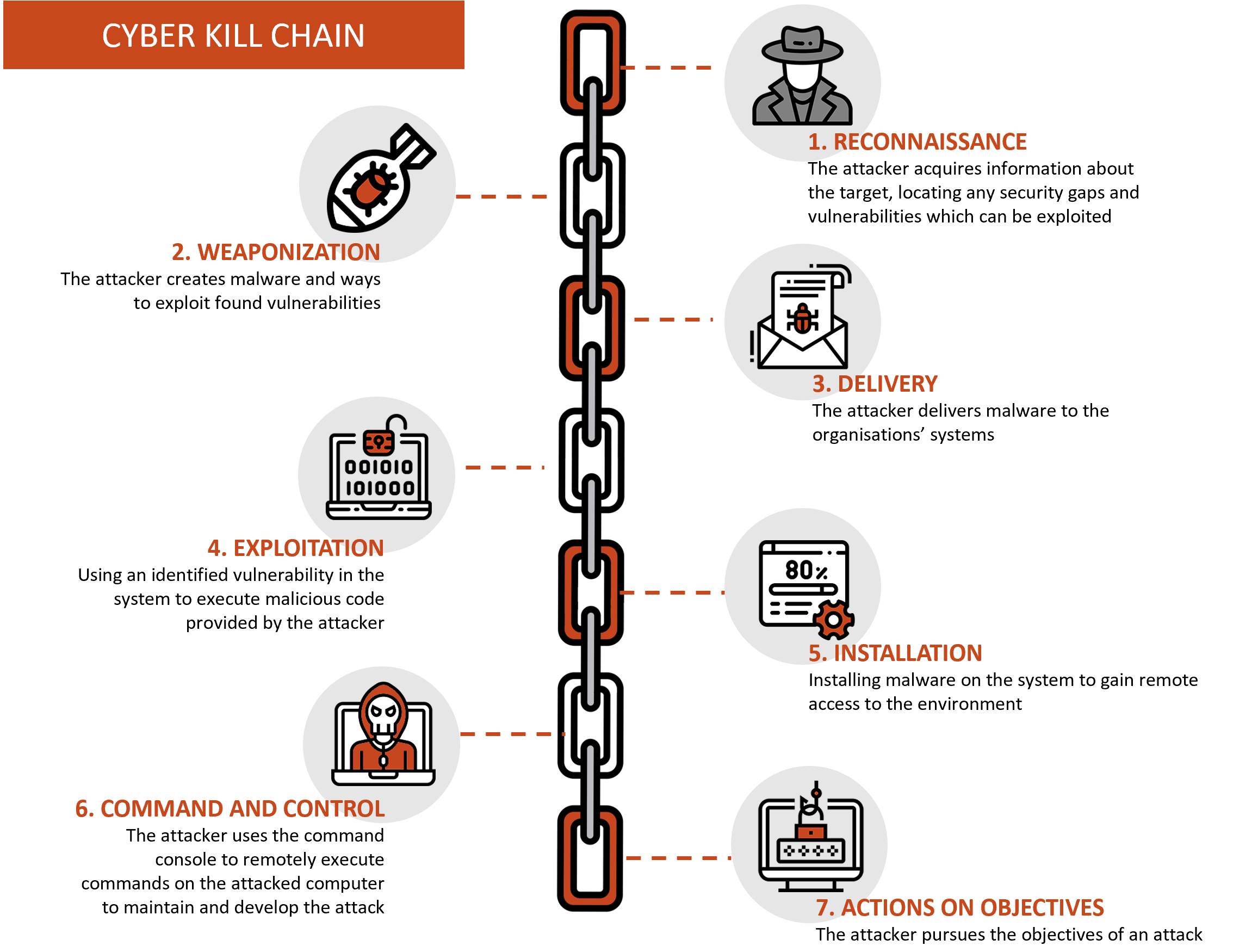
Explore the simplicity of Lockheed Kill Chain through substantial collections of elegant photographs. featuring understated examples of computer, digital, and electronic. designed to emphasize clarity and focus. Discover high-resolution Lockheed Kill Chain images optimized for various applications. Suitable for various applications including web design, social media, personal projects, and digital content creation All Lockheed Kill Chain images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Explore the versatility of our Lockheed Kill Chain collection for various creative and professional projects. Whether for commercial projects or personal use, our Lockheed Kill Chain collection delivers consistent excellence. The Lockheed Kill Chain archive serves professionals, educators, and creatives across diverse industries. Comprehensive tagging systems facilitate quick discovery of relevant Lockheed Kill Chain content. Advanced search capabilities make finding the perfect Lockheed Kill Chain image effortless and efficient. Instant download capabilities enable immediate access to chosen Lockheed Kill Chain images. Regular updates keep the Lockheed Kill Chain collection current with contemporary trends and styles. Time-saving browsing features help users locate ideal Lockheed Kill Chain images quickly. Multiple resolution options ensure optimal performance across different platforms and applications. Professional licensing options accommodate both commercial and educational usage requirements.




![Lockheed Martin’s cyber kill chain model [10] | Download Scientific Diagram](https://www.researchgate.net/publication/324275509/figure/fig2/AS:941748901642240@1601541843014/Lockheed-Martins-cyber-kill-chain-model-10.gif)





![Lockheed Martin Cyber Kill Chain (CKC) [22] seven steps. The part that ...](https://www.researchgate.net/publication/335024682/figure/fig1/AS:789313017098241@1565198296990/Lockheed-Martin-Cyber-Kill-Chain-CKC-22-seven-steps-The-part-that-is-specified-with.png)
![Lockheed Martin’s cyber kill chain model [10] | Download Scientific Diagram](https://www.researchgate.net/publication/324275509/figure/fig4/AS:941748901658634@1601541843181/Command-Fives-cyber-kill-chain-model-6_Q320.jpg)















![Lockheed martin cyber kill chain model [22] | Download Scientific Diagram](https://www.researchgate.net/publication/357778471/figure/fig3/AS:1140232191770625@1648863947395/The-structure-of-AHP_Q320.jpg)



![Lockheed Martin’s cyber kill chain model [10] | Download Scientific Diagram](https://www.researchgate.net/publication/324275509/figure/fig1/AS:941748897464370@1601541842947/Example-of-multimedia-service-architecture-in-the-context-of-IoT-28_Q640.jpg)





![Lockheed martin cyber kill chain model [22] | Download Scientific Diagram](https://www.researchgate.net/publication/357778471/figure/fig1/AS:1140232191774720@1648863947364/Lockheed-martin-cyber-kill-chain-model-22.png)


![Lockheed Martin Cyber Kill Chain (CKC) [22] seven steps. The part that ...](https://www.researchgate.net/publication/335024682/figure/tbl1/AS:789313021280256@1565198297045/Mapping-between-the-collected-Ransomware-features-and-the-proposed-taxonomy_Q640.jpg)




![Lockheed Martin Cyber Kill Chain (CKC) [22] seven steps. The part that ...](https://www.researchgate.net/publication/351433803/figure/fig2/AS:1024358420062208@1621237487097/Data-usage-versus-domain_Q640.jpg)




















![Overview of the Cyber Kill Chain [TM] | PDF](https://image.slidesharecdn.com/cybersecuritykillchain8-161209191549/85/Overview-of-the-Cyber-Kill-Chain-TM-8-320.jpg)








![Lockheed Martin course of actions matrix [22]. The rows specify the CKC ...](https://www.researchgate.net/publication/335024682/figure/fig1/AS:789313017098241@1565198296990/Lockheed-Martin-Cyber-Kill-Chain-CKC-22-seven-steps-The-part-that-is-specified-with_Q320.jpg)