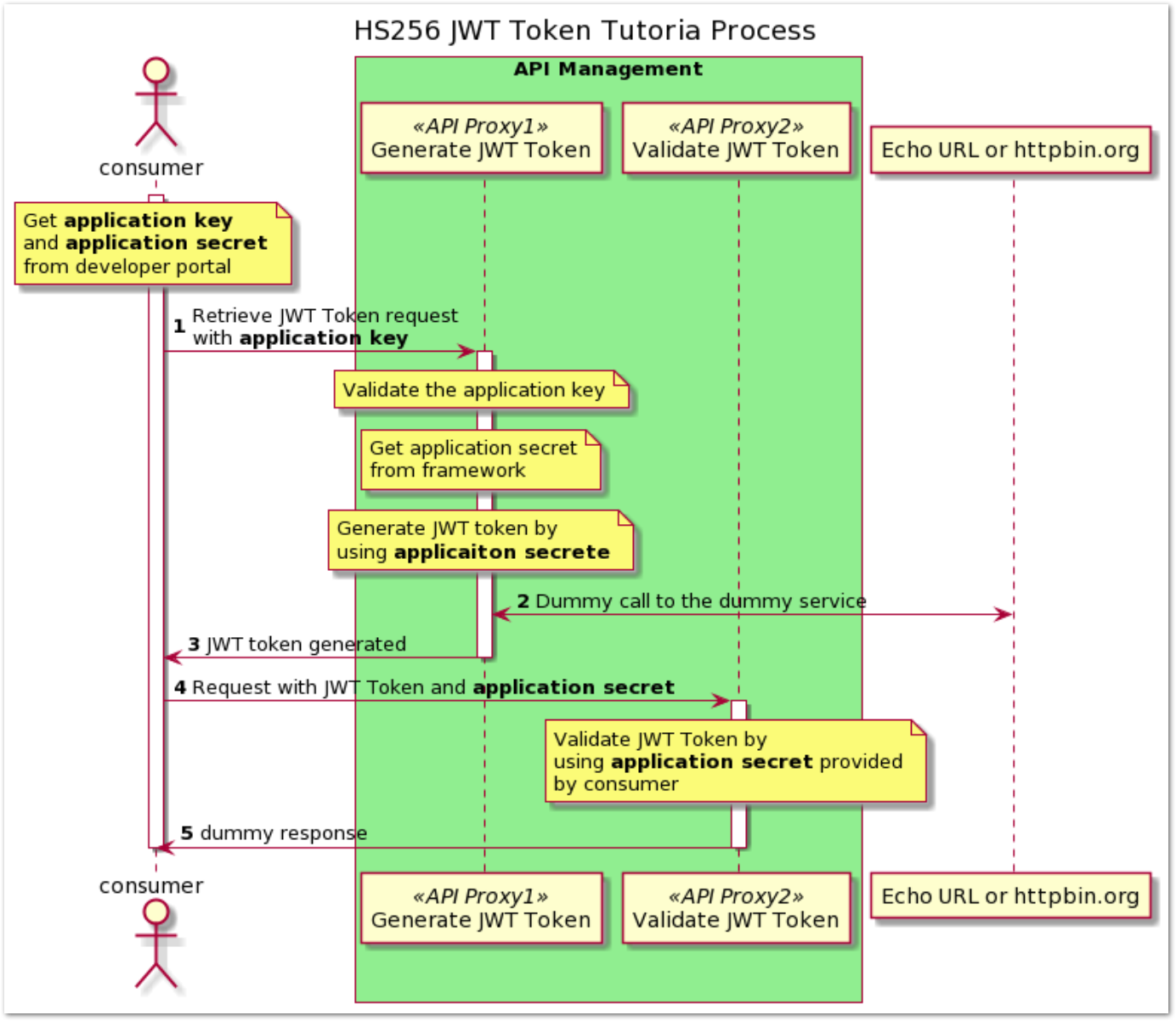
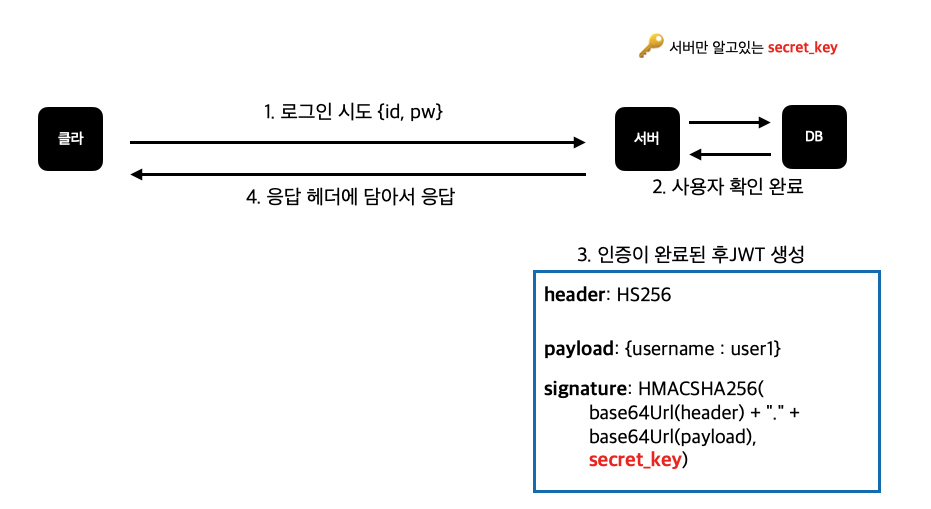
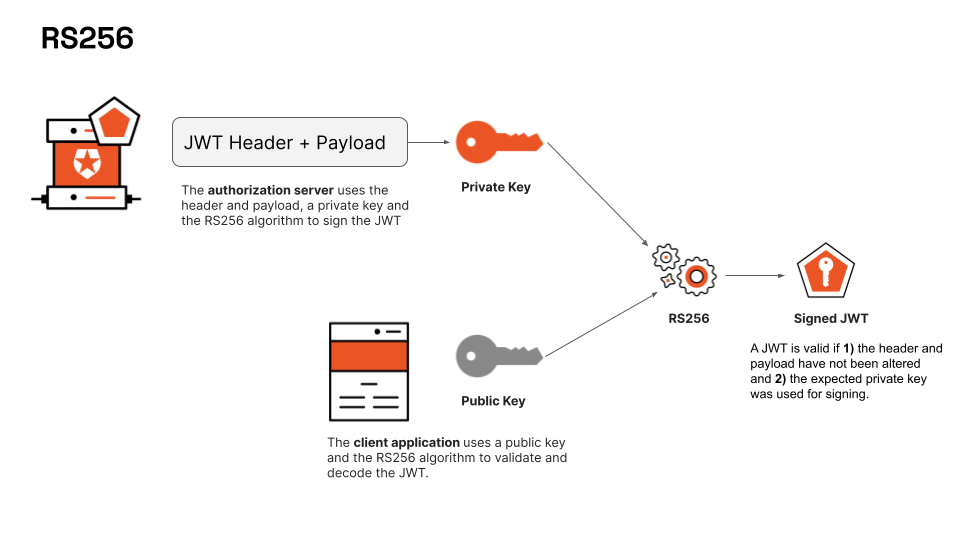
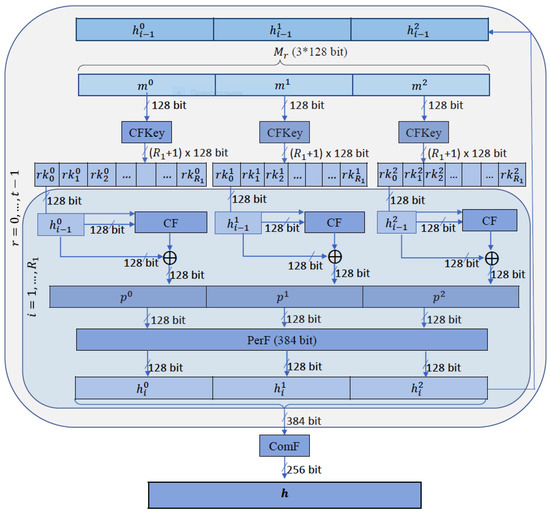
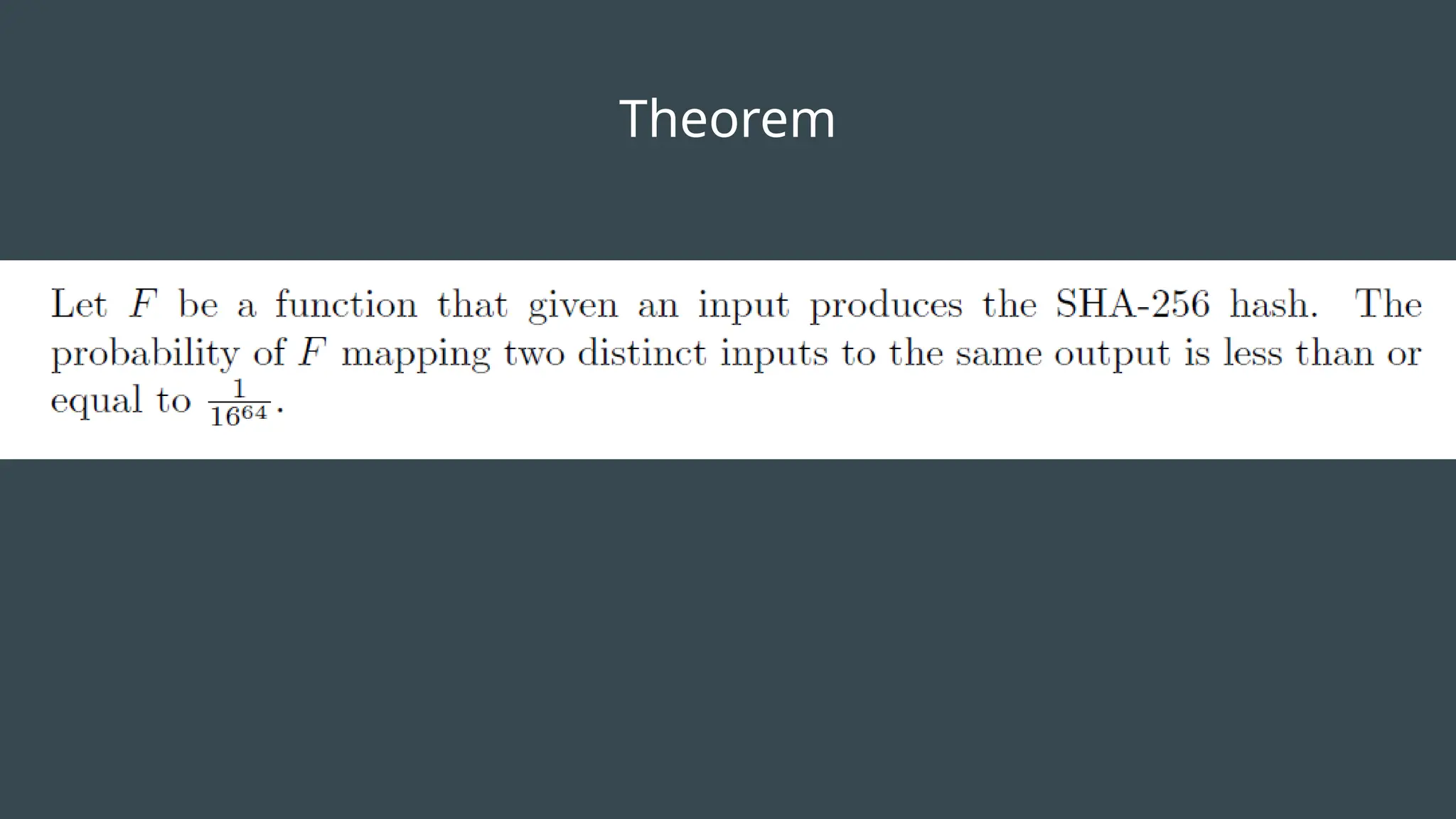
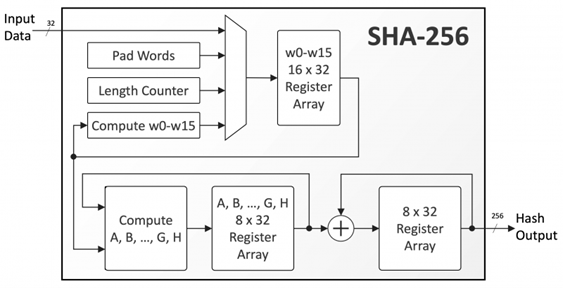
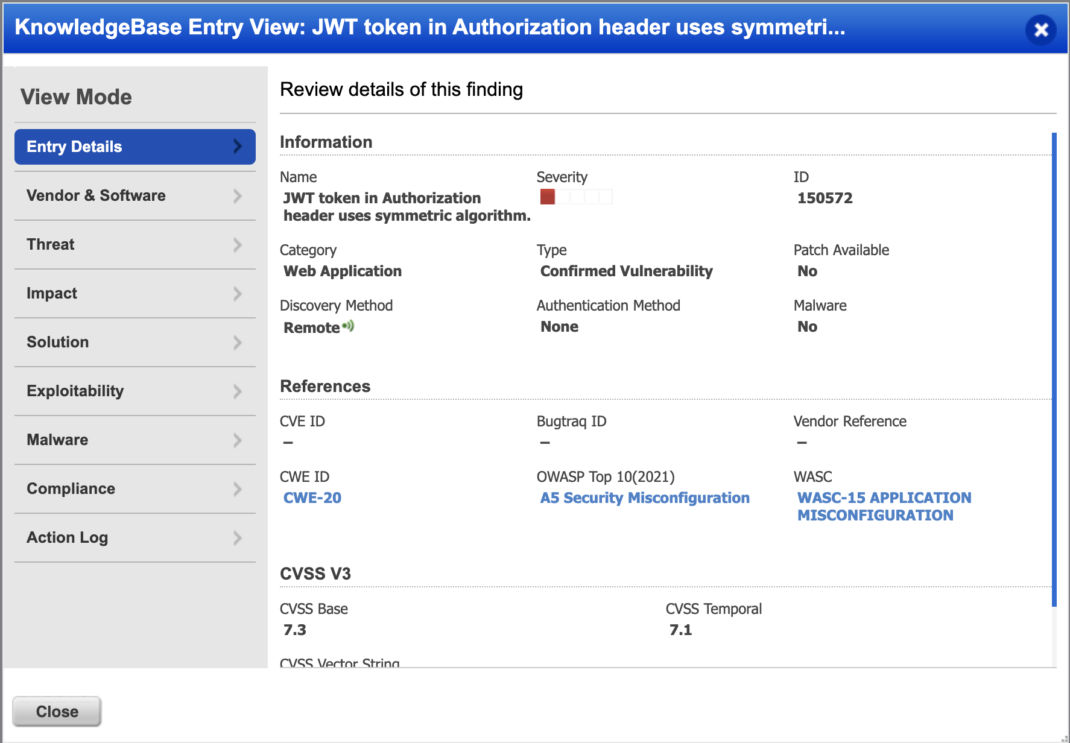
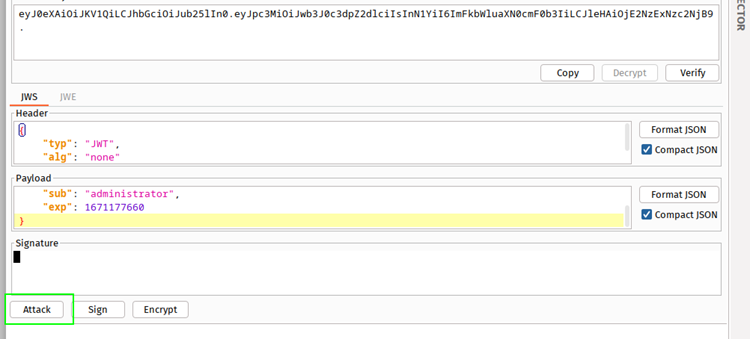
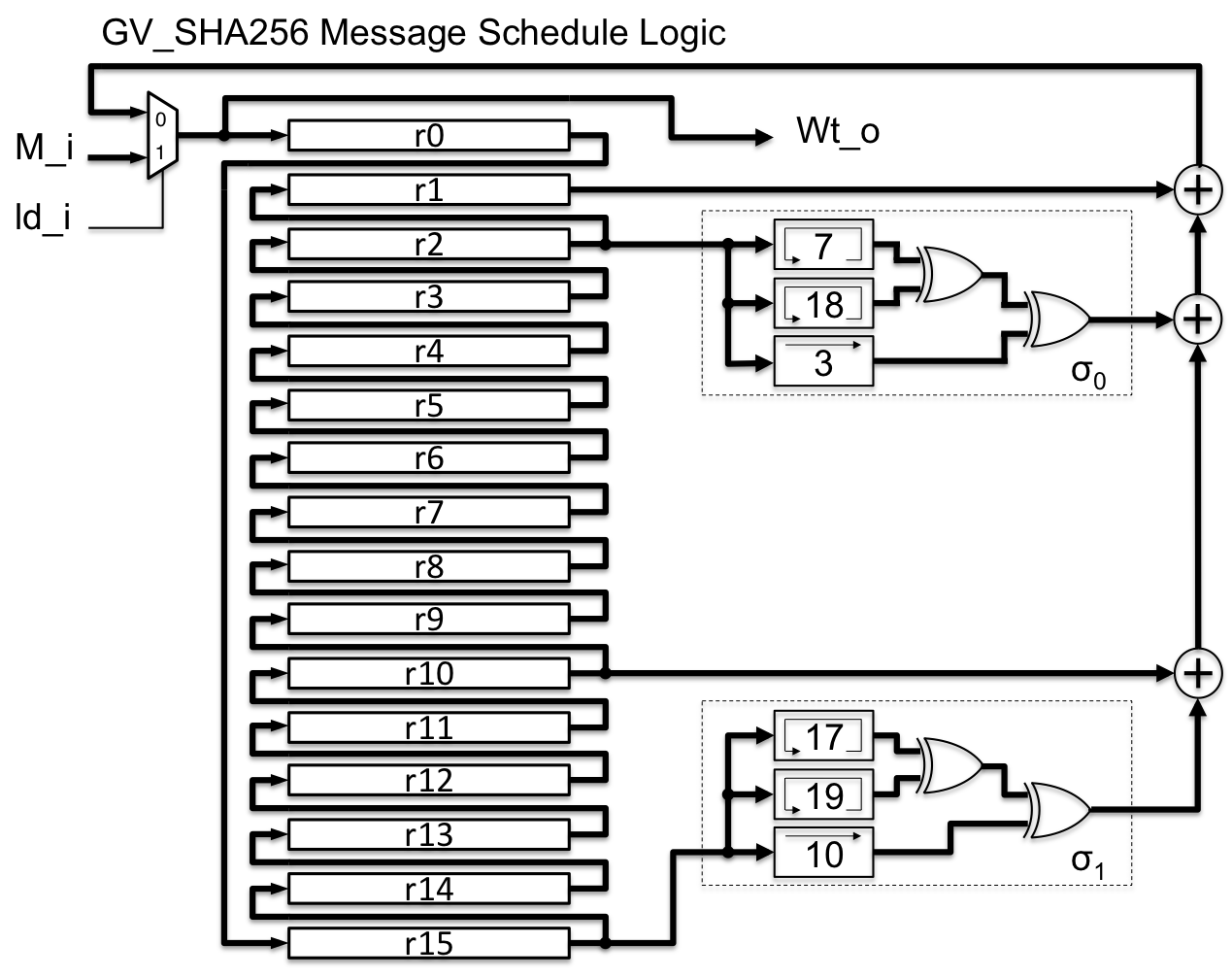
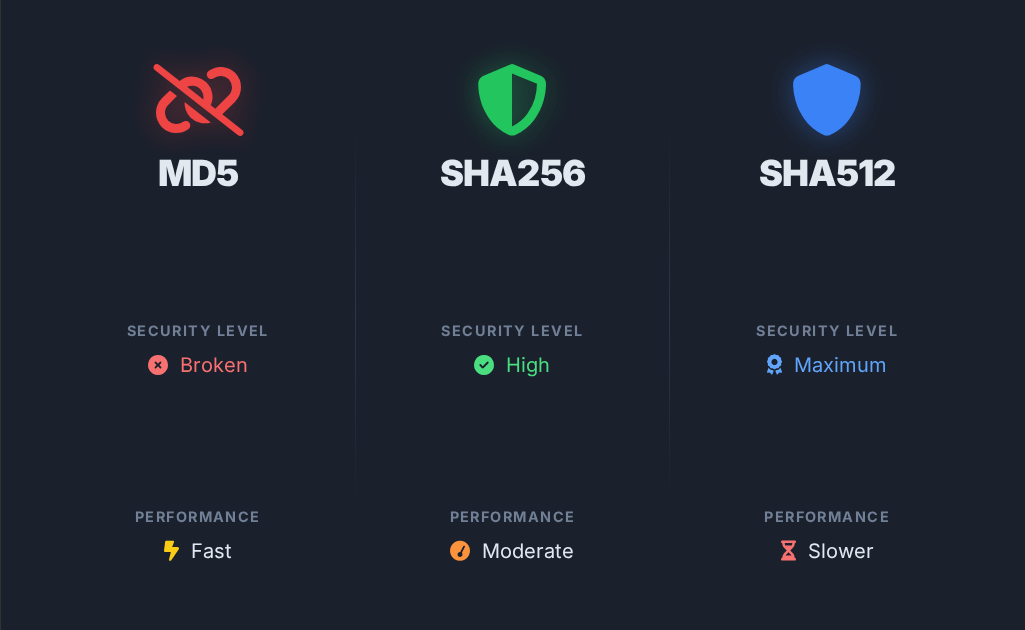
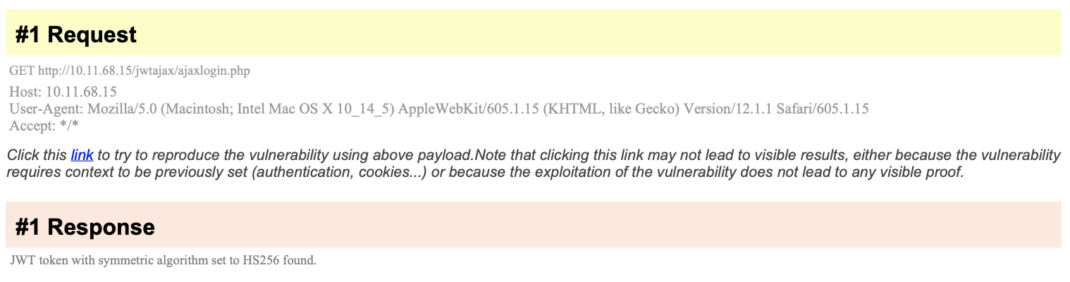
Hs256 Algorithm Explain
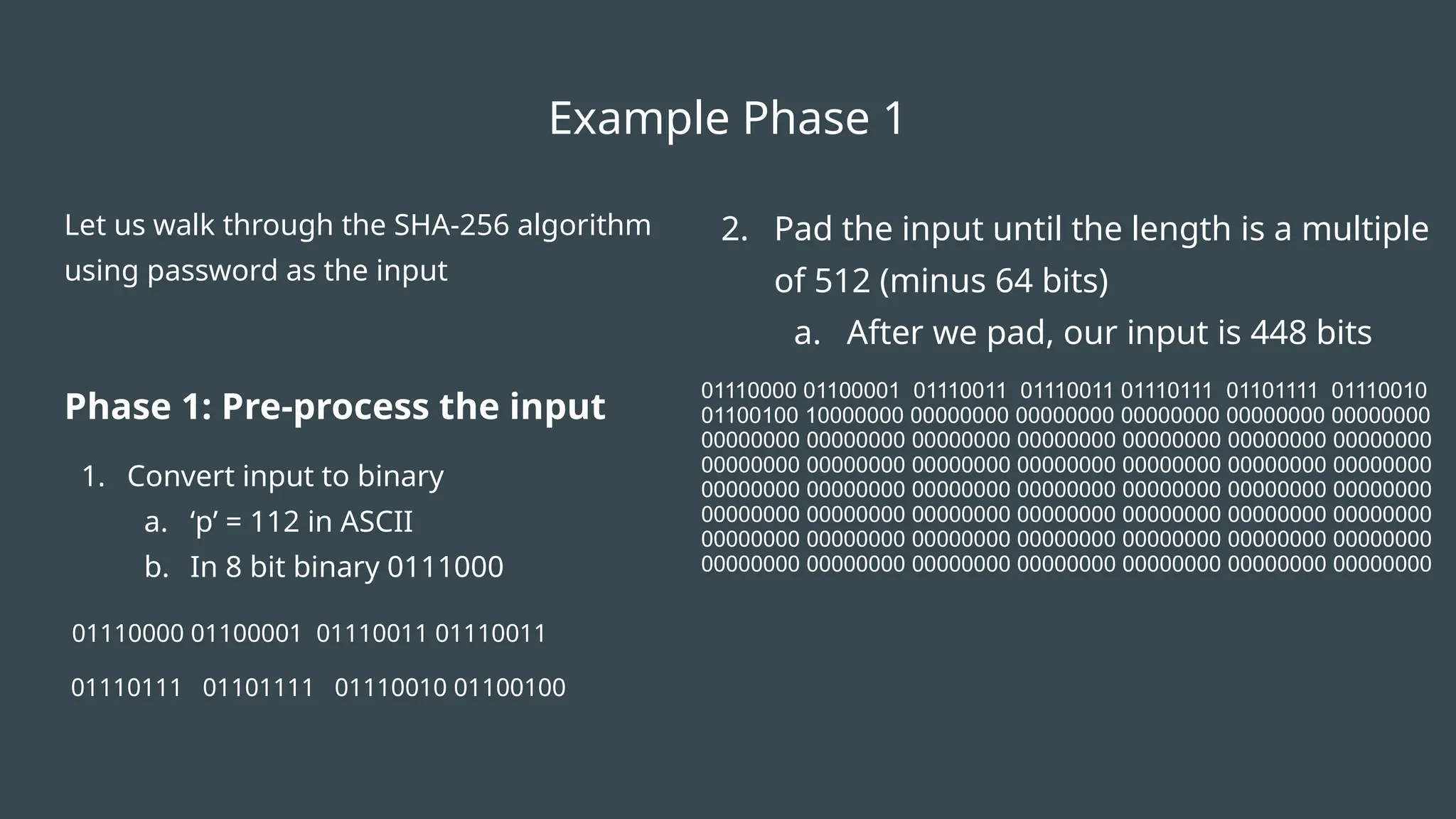
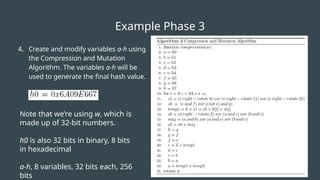
Enhance your understanding of Hs256 Algorithm Explain with substantial collections of carefully selected educational photographs. designed to support various learning styles and educational approaches. bridging theoretical knowledge with practical visual examples. Our Hs256 Algorithm Explain collection features high-quality images with excellent detail and clarity. Excellent for educational materials, academic research, teaching resources, and learning activities All Hs256 Algorithm Explain images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. The Hs256 Algorithm Explain collection serves as a valuable educational resource for teachers and students. Whether for commercial projects or personal use, our Hs256 Algorithm Explain collection delivers consistent excellence. Comprehensive tagging systems facilitate quick discovery of relevant Hs256 Algorithm Explain content. Reliable customer support ensures smooth experience throughout the Hs256 Algorithm Explain selection process. Regular updates keep the Hs256 Algorithm Explain collection current with contemporary trends and styles. Instant download capabilities enable immediate access to chosen Hs256 Algorithm Explain images. Diverse style options within the Hs256 Algorithm Explain collection suit various aesthetic preferences. Advanced search capabilities make finding the perfect Hs256 Algorithm Explain image effortless and efficient. Multiple resolution options ensure optimal performance across different platforms and applications.






![7): SHA -256 Hash Algorithm .[15] | Download Scientific Diagram](https://www.researchgate.net/profile/Hani-Bakeer/publication/365655714/figure/fig7/AS:11431281098939278@1669160243998/Figure-27-SHA-256-Hash-Algorithm-15.png)






![[PDF] Optimising the SHA256 Hashing Algorithm for Faster and More ...](https://figures.semanticscholar.org/8e98b5e6f88594abe209125bdf30f898819bab89/17-Figure2-1.png)
























%2Fimages%2Fimage1.png&w=1920&q=75)






![[OPD 2019] Attacking JWT tokens | PDF](https://image.slidesharecdn.com/attackingjwttokens-191021171156/85/OPD-2019-Attacking-JWT-tokens-16-320.jpg)


