Graph Based Investigation Computer System
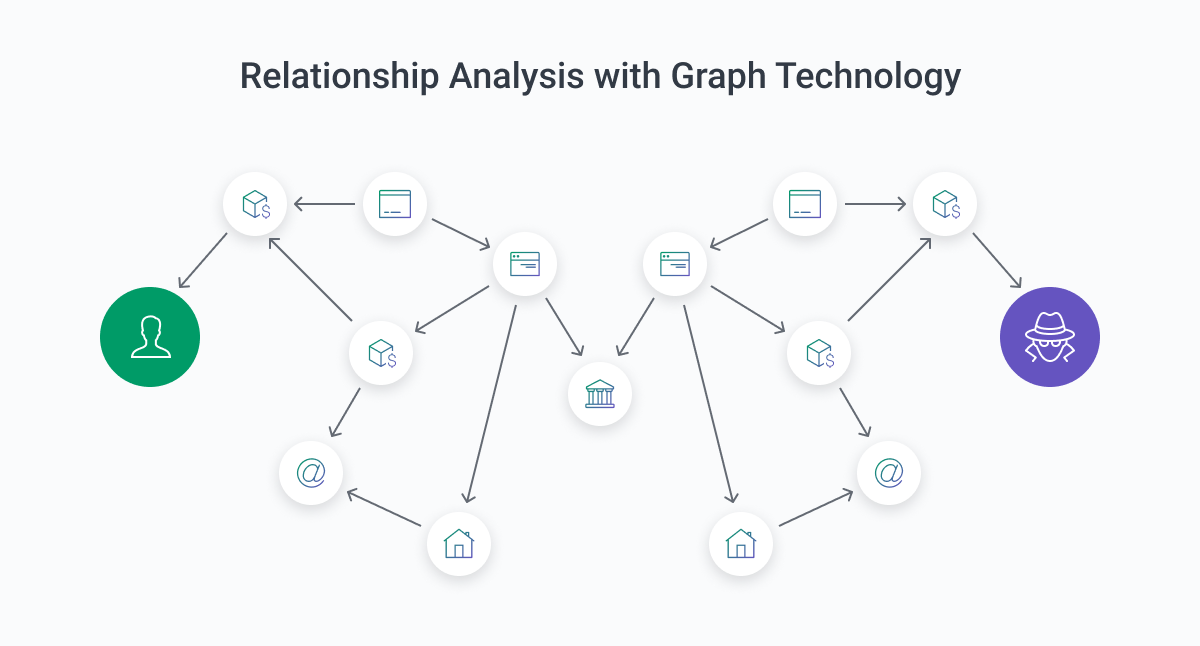
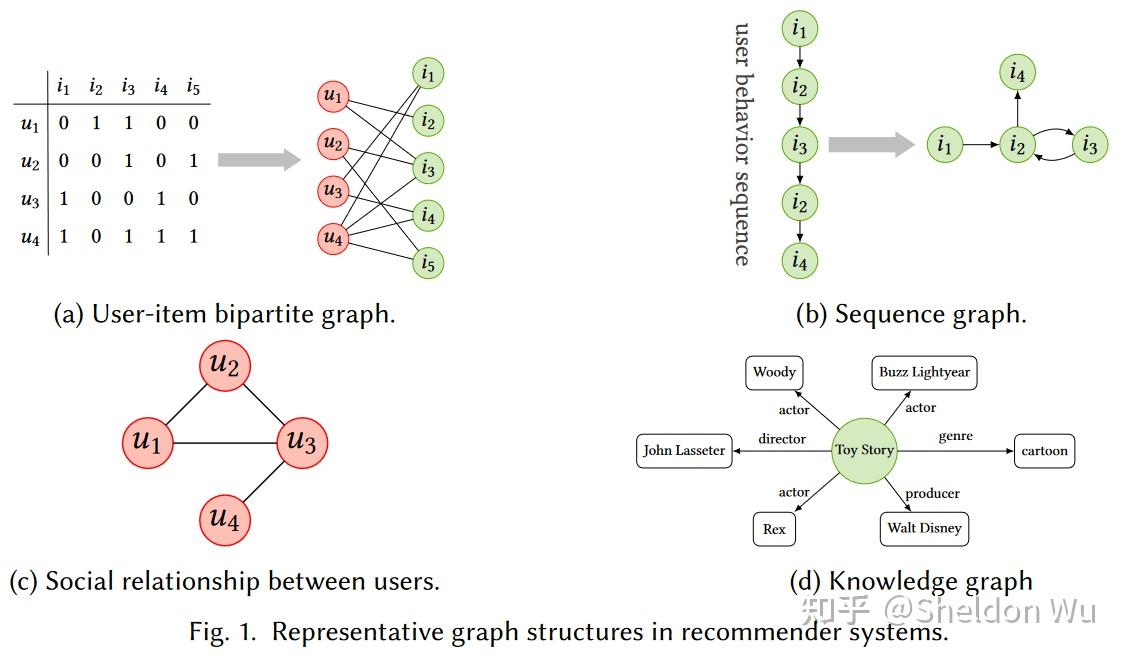
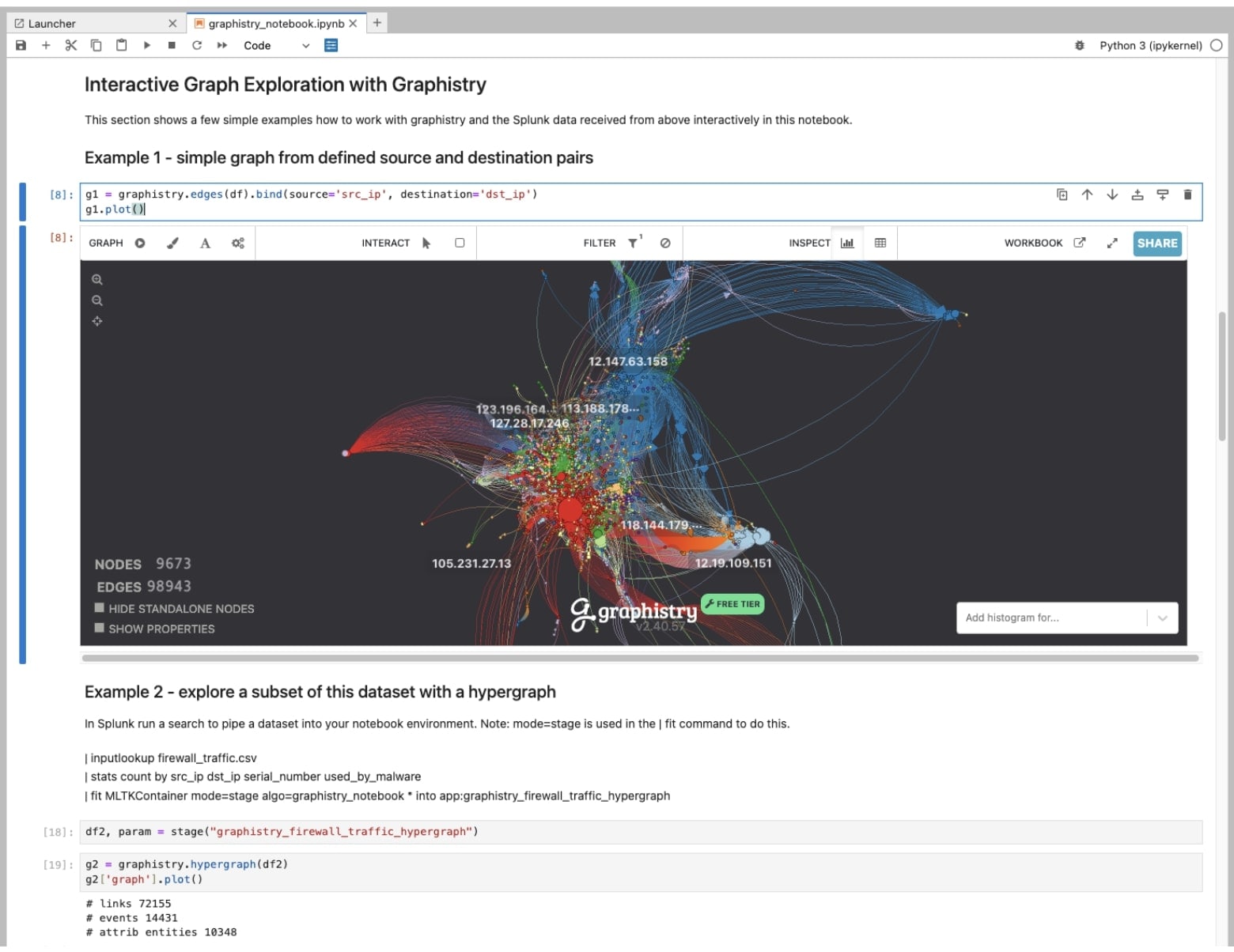
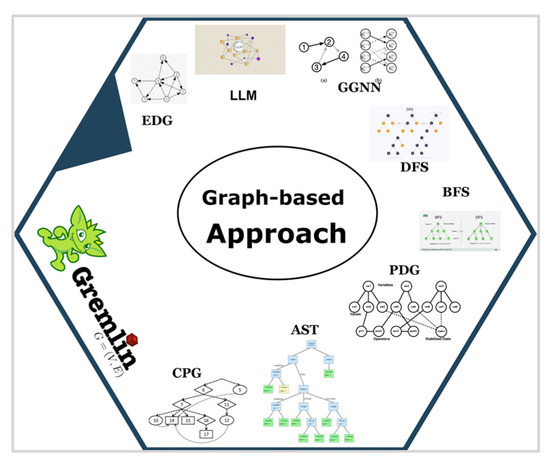
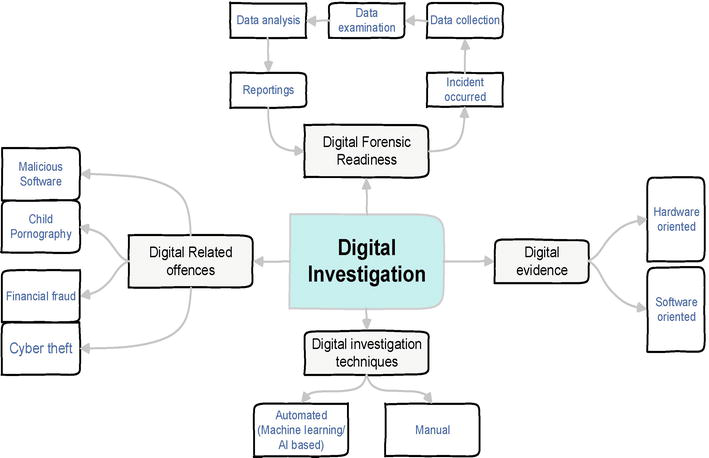
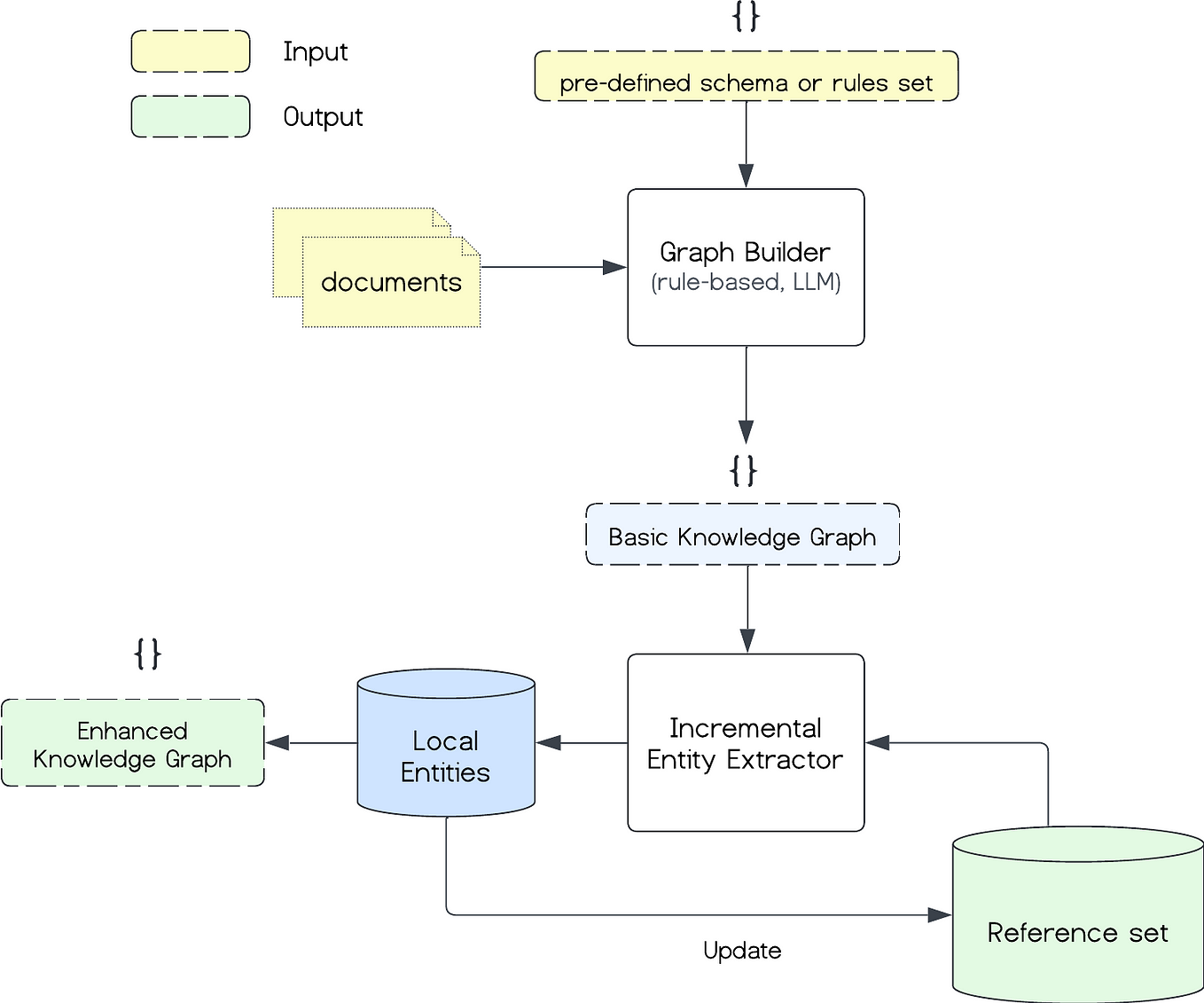
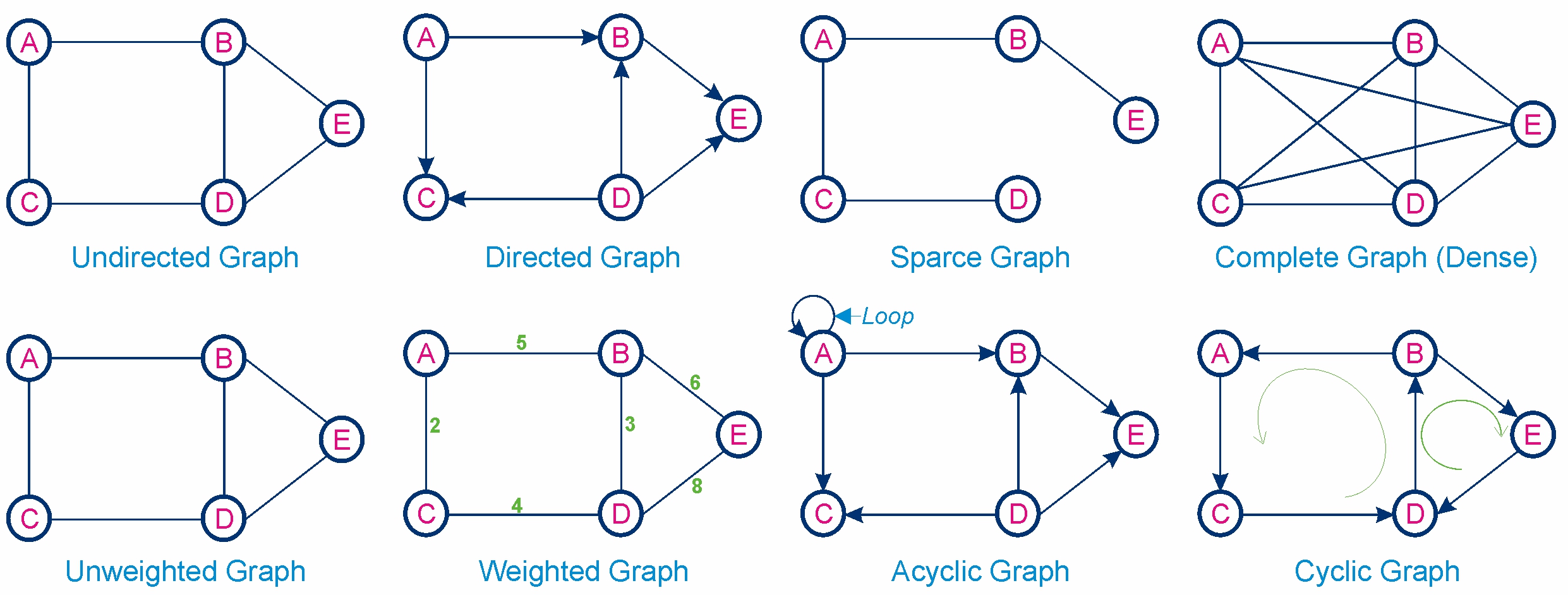
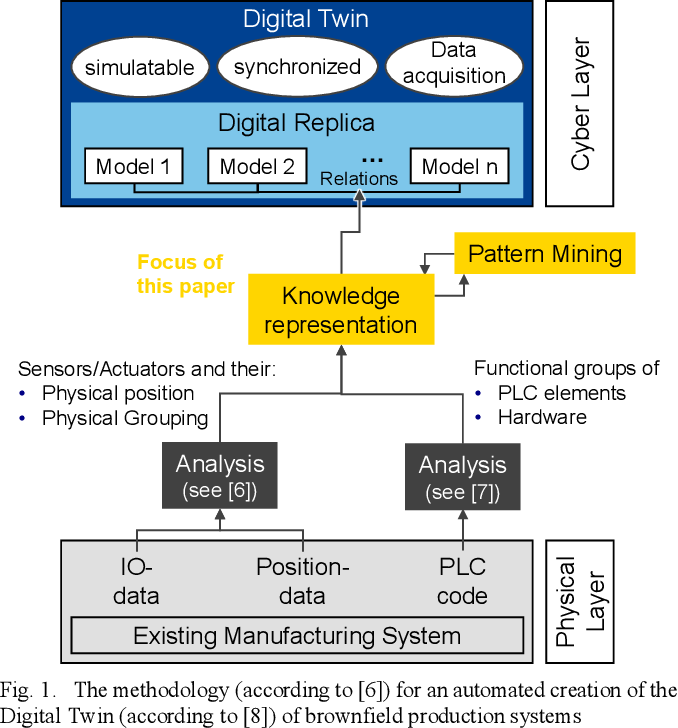
Experience the stunning modern approach to Graph Based Investigation Computer System with vast arrays of contemporary images. highlighting modern interpretations of technology, digital, and software. designed to showcase innovation and progress. Browse our premium Graph Based Investigation Computer System gallery featuring professionally curated photographs. Suitable for various applications including web design, social media, personal projects, and digital content creation All Graph Based Investigation Computer System images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Our Graph Based Investigation Computer System gallery offers diverse visual resources to bring your ideas to life. Diverse style options within the Graph Based Investigation Computer System collection suit various aesthetic preferences. Whether for commercial projects or personal use, our Graph Based Investigation Computer System collection delivers consistent excellence. Reliable customer support ensures smooth experience throughout the Graph Based Investigation Computer System selection process. Regular updates keep the Graph Based Investigation Computer System collection current with contemporary trends and styles. Each image in our Graph Based Investigation Computer System gallery undergoes rigorous quality assessment before inclusion. Comprehensive tagging systems facilitate quick discovery of relevant Graph Based Investigation Computer System content.















![[PPT] - Attack Graph Based Metrics for Identifying Critical Cyber ...](https://c.sambuz.com/788938/attack-graph-based-metrics-for-identifying-critical-cyber-l.jpg)













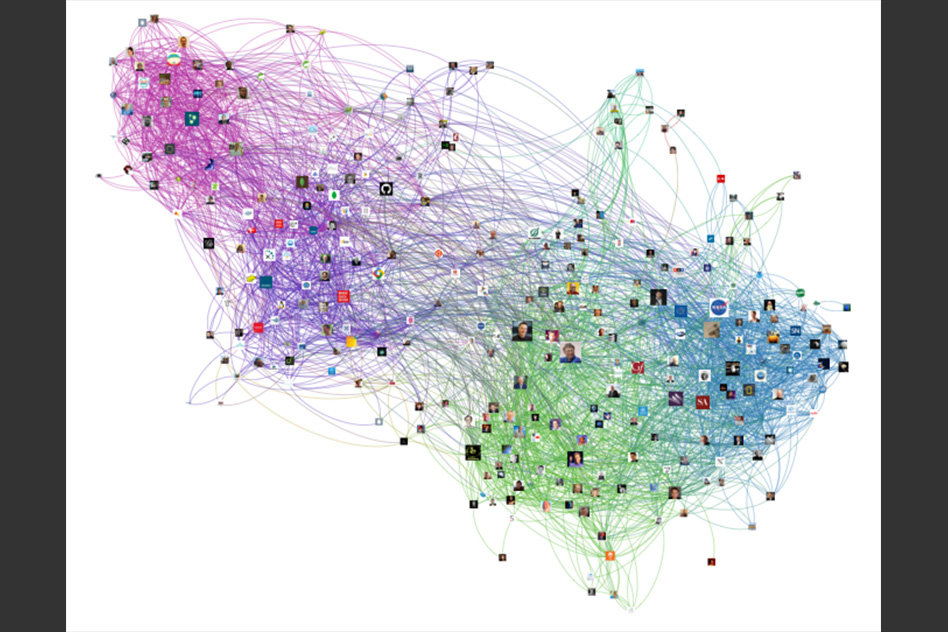



























![Connected Papers [14] graph-based visualization. | Download Scientific ...](https://www.researchgate.net/profile/Corinna-Breitinger/publication/357424397/figure/fig3/AS:1182773884796928@1659006677153/Connected-Papers-14-graph-based-visualization.png)







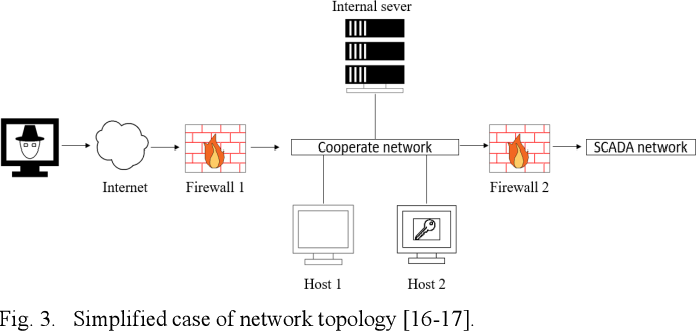
![Modified graph-based algorithm to analyze security threats in IoT [PeerJ]](https://dfzljdn9uc3pi.cloudfront.net/2023/cs-1743/1/fig-1-2x.jpg)