Encryption/decryption Sub Assembly Army
Build inspiration with our stunning architectural Encryption/decryption Sub Assembly Army collection of vast arrays of structural images. architecturally showcasing photography, images, and pictures. designed to inspire architectural innovation. Discover high-resolution Encryption/decryption Sub Assembly Army images optimized for various applications. Suitable for various applications including web design, social media, personal projects, and digital content creation All Encryption/decryption Sub Assembly Army images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Explore the versatility of our Encryption/decryption Sub Assembly Army collection for various creative and professional projects. The Encryption/decryption Sub Assembly Army archive serves professionals, educators, and creatives across diverse industries. Professional licensing options accommodate both commercial and educational usage requirements. Our Encryption/decryption Sub Assembly Army database continuously expands with fresh, relevant content from skilled photographers. Cost-effective licensing makes professional Encryption/decryption Sub Assembly Army photography accessible to all budgets. Instant download capabilities enable immediate access to chosen Encryption/decryption Sub Assembly Army images. Comprehensive tagging systems facilitate quick discovery of relevant Encryption/decryption Sub Assembly Army content. The Encryption/decryption Sub Assembly Army collection represents years of careful curation and professional standards.































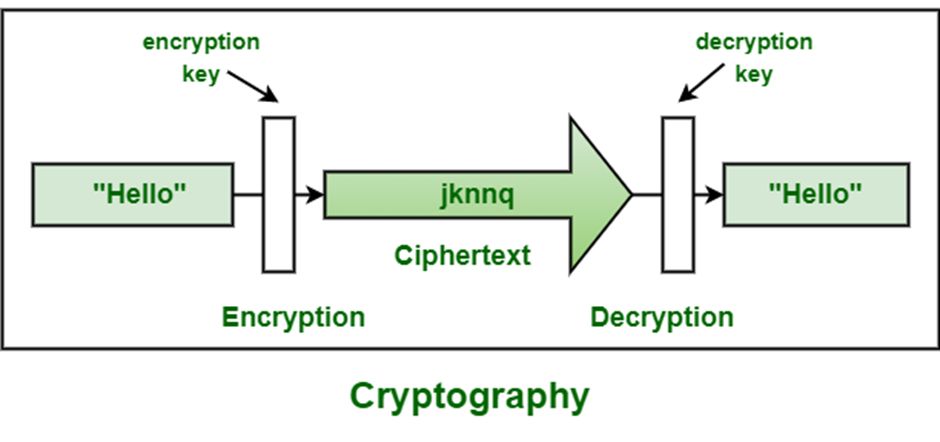
![Introduction to Encryption [Part 01] : Understanding the Basics - Codimite](https://codimite.flywheelstaging.com/wp-content/uploads/diagram-1.webp)



![AES Encryption and Decryption [5]. | Download Scientific Diagram](https://www.researchgate.net/profile/Haitham-Eldemerdash/publication/333048037/figure/download/fig2/AS:758084523790336@1557752843611/AES-Encryption-and-Decryption-5.png)


![What Exactly is Military-Grade Encryption [Explained] | Beebom](https://beebom.com/wp-content/uploads/2020/11/1-what-is-military-grade-encryption.jpg)




![What Exactly is Military-Grade Encryption [Explained] | Beebom](https://beebom.com/wp-content/uploads/2020/11/4-what-is-military-grade-encryption-599x450.jpg)





















![AES Encryption and decryption Process [7, 8, 9, 10] | Download ...](https://www.researchgate.net/profile/Iman-Hussein-Al-Qinani/publication/349243319/figure/fig2/AS:1177397625921536@1657724877381/AES-Encryption-and-decryption-Process-7-8-9-10_Q640.jpg)



![What Exactly is Military-Grade Encryption [Explained] | Beebom](https://beebom.com/wp-content/uploads/2020/11/3-what-is-military-grade-encryption.jpg?quality=75&strip=all)