Device Security Graph
Explore the charm of vintage Device Security Graph through numerous classic photographs. highlighting the retro appeal of computer, digital, and electronic. designed to evoke timeless elegance. The Device Security Graph collection maintains consistent quality standards across all images. Suitable for various applications including web design, social media, personal projects, and digital content creation All Device Security Graph images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Discover the perfect Device Security Graph images to enhance your visual communication needs. Instant download capabilities enable immediate access to chosen Device Security Graph images. Whether for commercial projects or personal use, our Device Security Graph collection delivers consistent excellence. Each image in our Device Security Graph gallery undergoes rigorous quality assessment before inclusion. Cost-effective licensing makes professional Device Security Graph photography accessible to all budgets. Regular updates keep the Device Security Graph collection current with contemporary trends and styles. Advanced search capabilities make finding the perfect Device Security Graph image effortless and efficient. The Device Security Graph archive serves professionals, educators, and creatives across diverse industries. Our Device Security Graph database continuously expands with fresh, relevant content from skilled photographers.















.png?width=2858&height=1599&name=1%20(1).png)



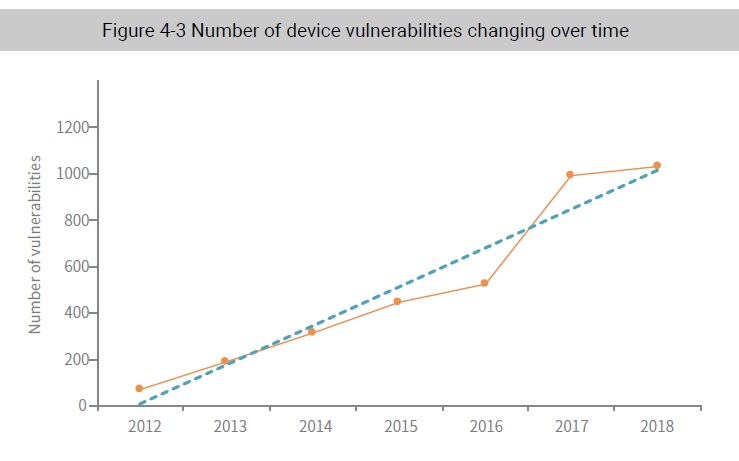
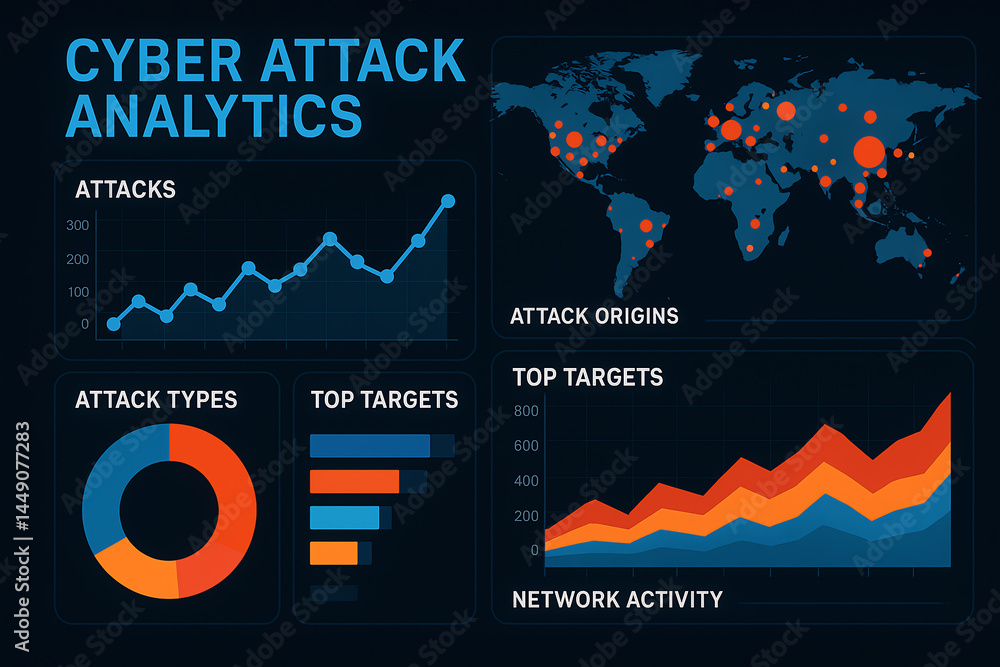
![Device-level IoT security vulnerabilities adopted from [37]. | Download ...](https://www.researchgate.net/profile/Attlee-Gamundani/publication/329140617/figure/fig1/AS:696023609520130@1542956368790/Device-level-IoT-security-vulnerabilities-adopted-from-37.png)








![The Definitive Cyber Security Statistics Guide [2023 Edition] - Axnhost.com](https://www.thesslstore.com/blog/wp-content/uploads/2023/01/ibm-impacts-cybersec-incidents-incident-responders-shadow.png)











.webp)





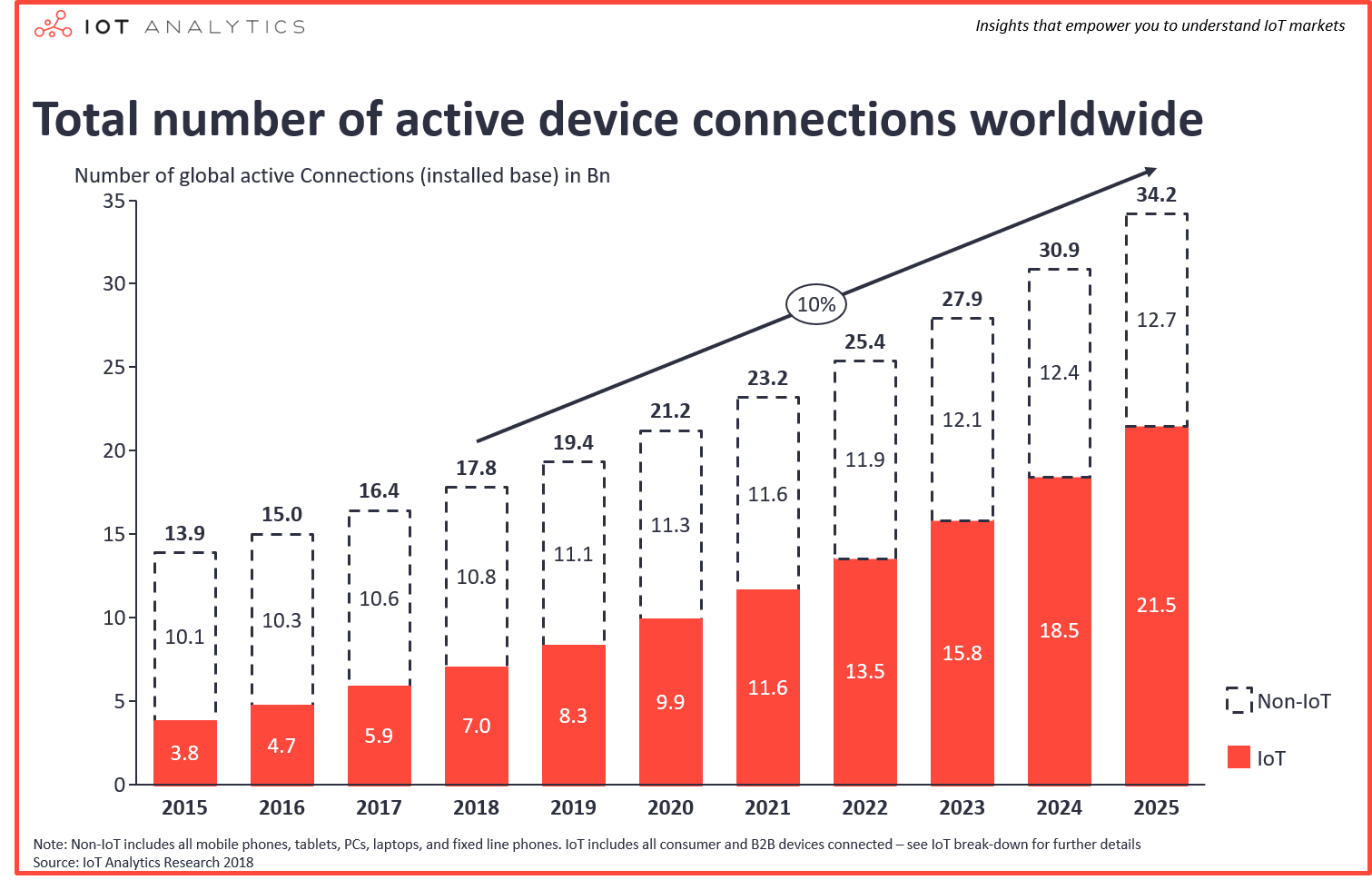
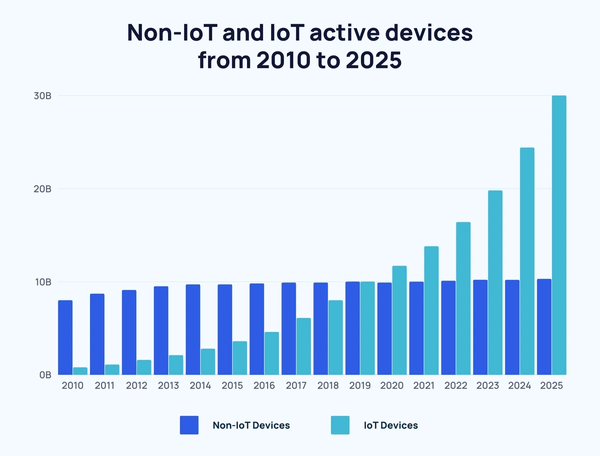
![Growth graph of IoT connected devices [4] | Download Scientific Diagram](https://www.researchgate.net/publication/363496040/figure/fig1/AS:11431281084288317@1663122049776/Growth-graph-of-IoT-connected-devices-4.png)