Command Get User Hash Id
Showcase trends with our fashion Command Get User Hash Id gallery of substantial collections of chic images. fashionably showcasing photography, images, and pictures. ideal for style blogs and trend reporting. The Command Get User Hash Id collection maintains consistent quality standards across all images. Suitable for various applications including web design, social media, personal projects, and digital content creation All Command Get User Hash Id images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Explore the versatility of our Command Get User Hash Id collection for various creative and professional projects. Time-saving browsing features help users locate ideal Command Get User Hash Id images quickly. Advanced search capabilities make finding the perfect Command Get User Hash Id image effortless and efficient. Whether for commercial projects or personal use, our Command Get User Hash Id collection delivers consistent excellence. Cost-effective licensing makes professional Command Get User Hash Id photography accessible to all budgets. Multiple resolution options ensure optimal performance across different platforms and applications. Comprehensive tagging systems facilitate quick discovery of relevant Command Get User Hash Id content. Regular updates keep the Command Get User Hash Id collection current with contemporary trends and styles.
:max_bytes(150000):strip_icc()/001_how-to-find-a-users-security-identifier-sid-in-windows-2625149-5c74b645c9e77c0001f57abe.jpg)


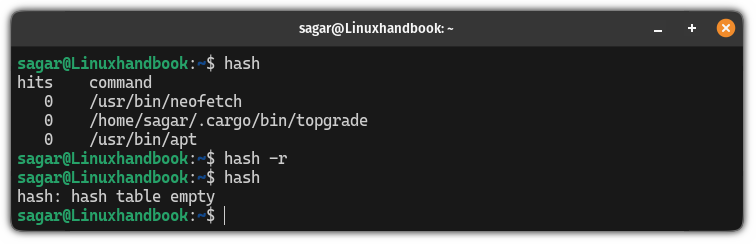
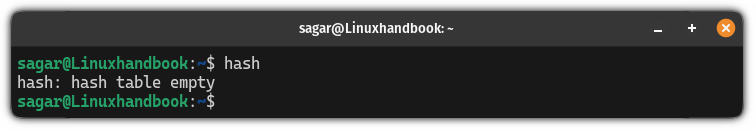
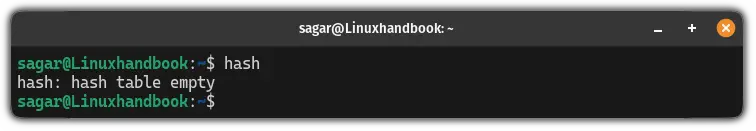















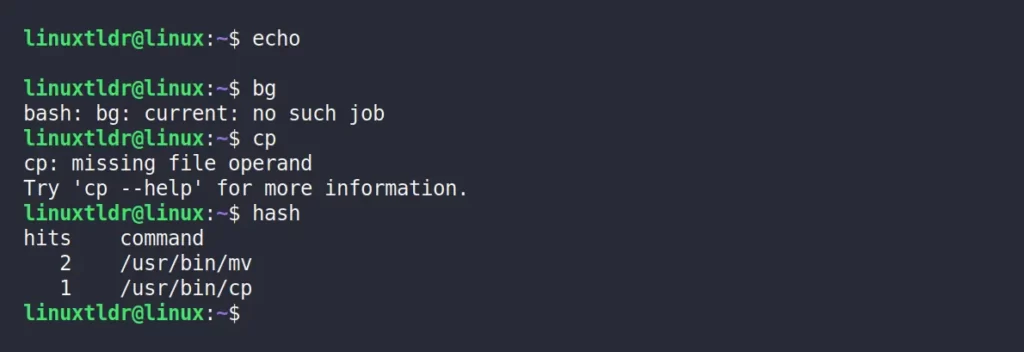


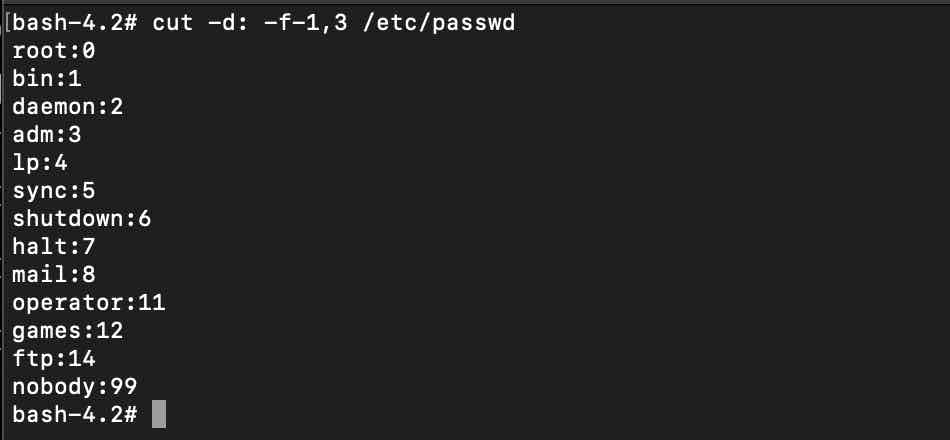
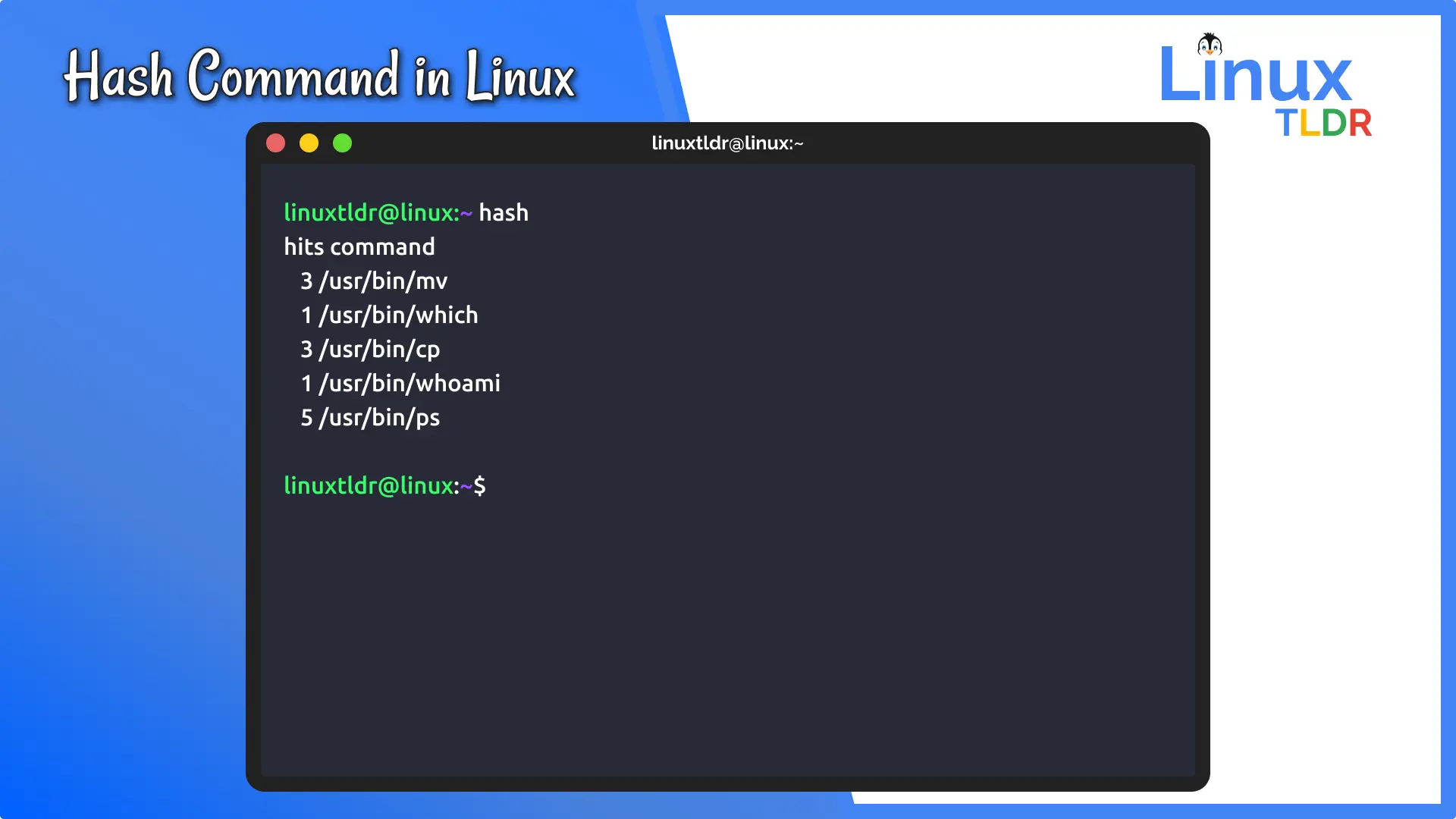
![The “hash” Command in Linux [6 Practical Examples]](https://linuxsimply.com/wp-content/uploads/2023/07/img2-Displaying-the-contents-of-hash-table.png)
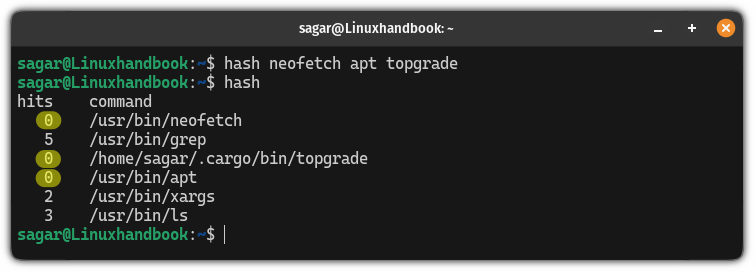
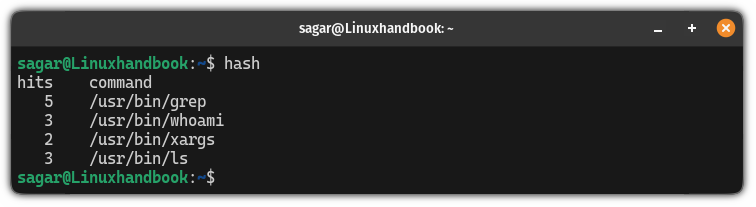
![The “hash” Command in Linux [6 Practical Examples]](https://linuxsimply.com/wp-content/uploads/2023/07/img4-listing-hash-table-767x276.png)
![The “hash” Command in Linux [6 Practical Examples]](https://linuxsimply.com/wp-content/uploads/2023/07/img1-checking-return-values-766x284.png)
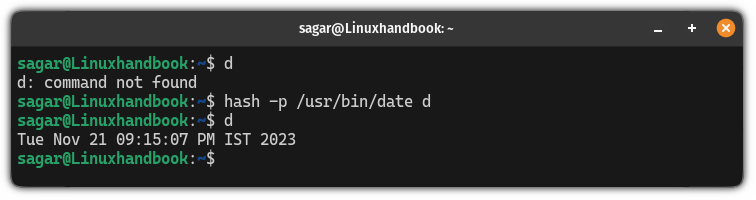
![The “hash” Command in Linux [6 Practical Examples]](https://linuxsimply.com/wp-content/uploads/2023/07/img7-adding-naming-new-path-768x361.png)
![The “hash” Command in Linux [6 Practical Examples]](https://linuxsimply.com/wp-content/uploads/2023/07/img6-location-of-multiple-commands-767x242.png)
![The “hash” Command in Linux [6 Practical Examples]](https://linuxsimply.com/wp-content/uploads/2023/07/Feature-image-hash-command-in-linux.png)
![The “hash” Command in Linux [6 Practical Examples]](https://linuxsimply.com/wp-content/uploads/2023/07/img5-location-of-command.png)

![The “hash” Command in Linux [6 Practical Examples]](https://linuxsimply.com/wp-content/uploads/2023/07/img9-clear-hash-table.png)

![The “hash” Command in Linux [6 Practical Examples]](https://linuxsimply.com/wp-content/uploads/2023/07/img8-delete-an-item-766x311.png)



![The “hash” Command in Linux [6 Practical Examples]](https://linuxsimply.com/wp-content/uploads/2023/07/img3-hash-table-empty-765x177.png)

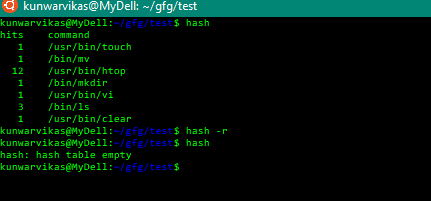
![How to Find UID of a User in Linux [3 Best Methods]](https://linuxier.com/wp-content/uploads/2024/04/listing-content-of-passwd-file-768x535.jpg)

















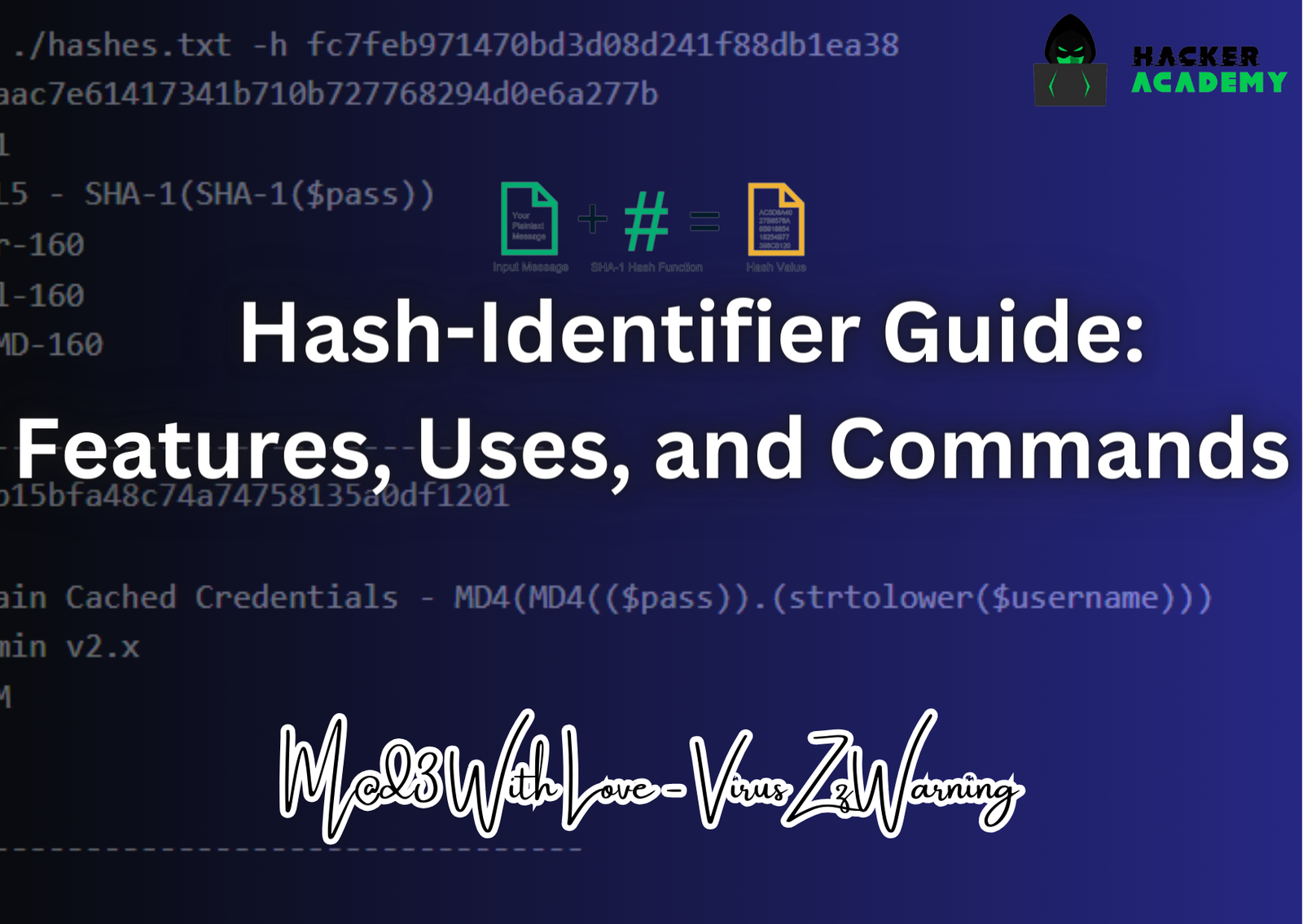
![Fingerprint a Hashed Password with Hash-Identifier [Tutorial] - YouTube](https://i.ytimg.com/vi/aC7Pjjr6NcM/maxresdefault.jpg)