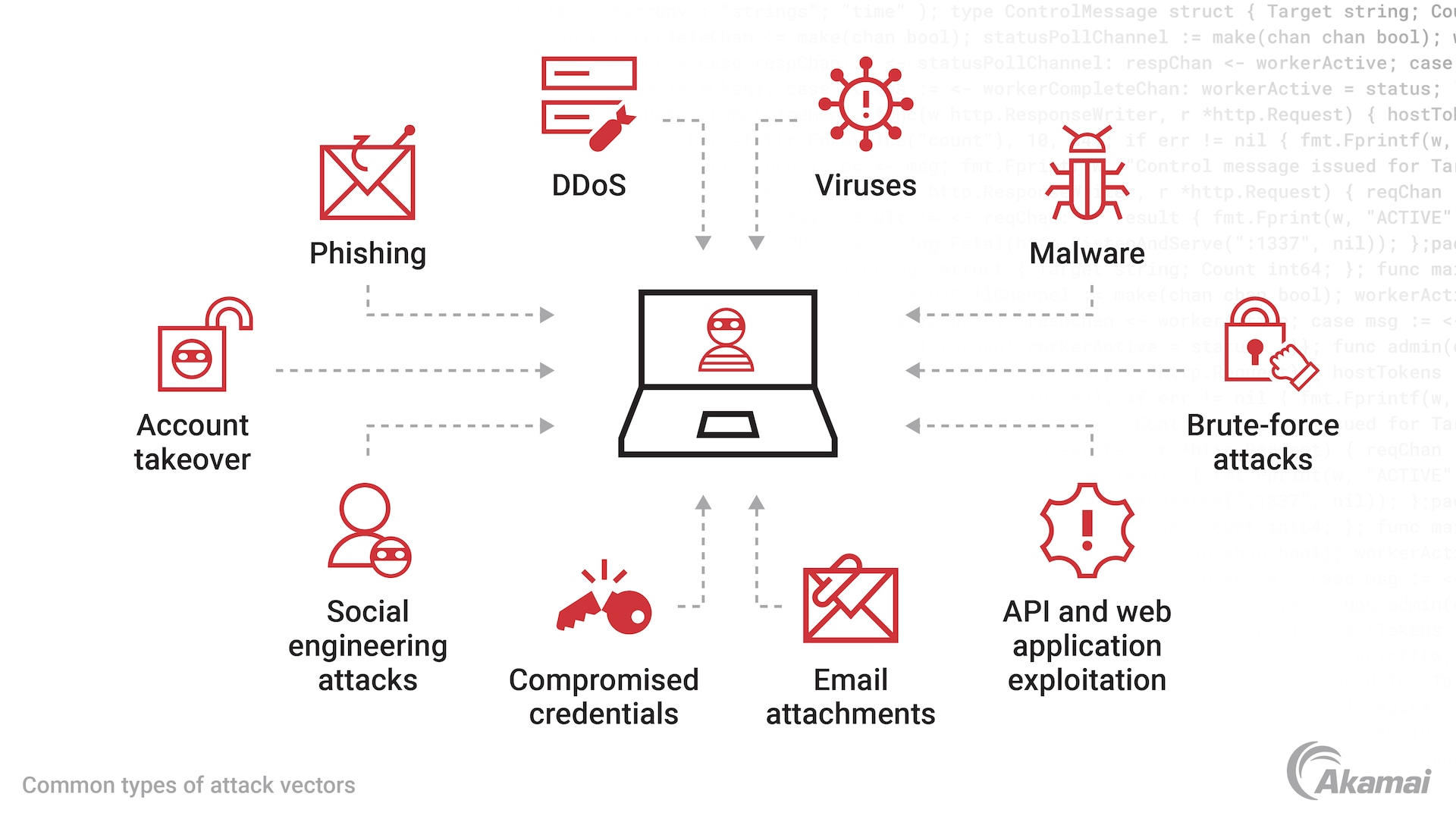
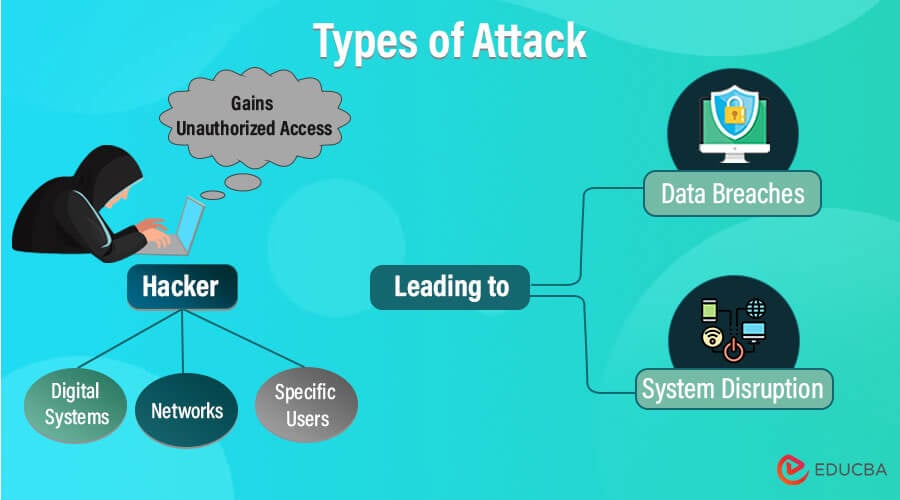
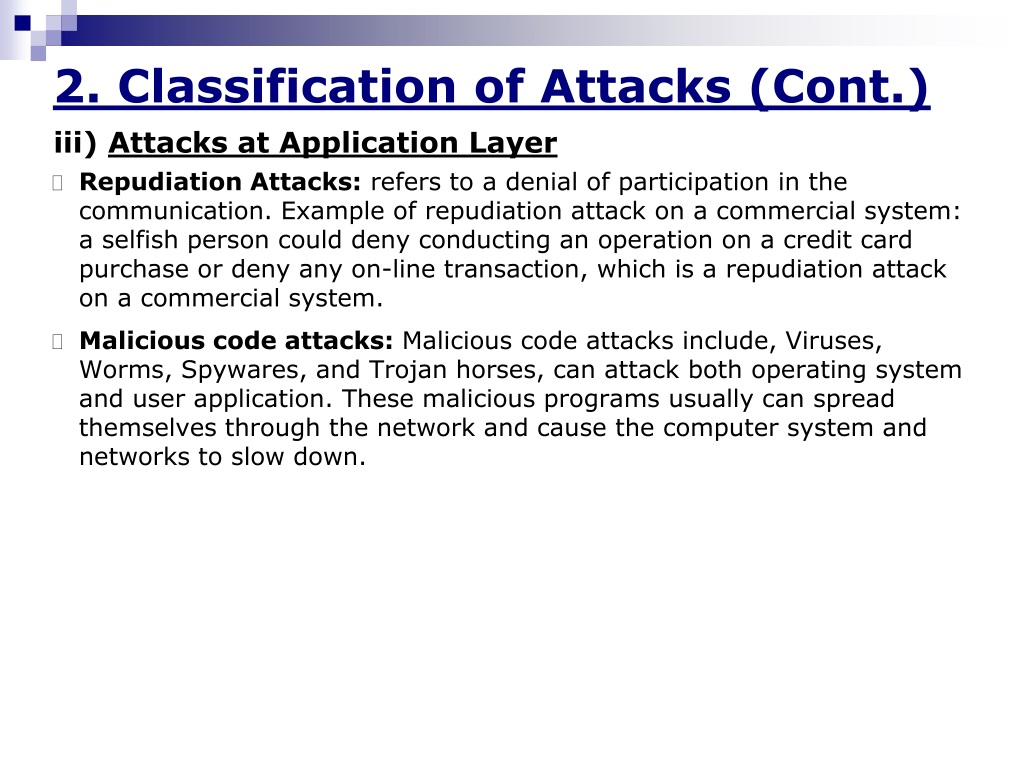
Attack Names
Access our comprehensive Attack Names database featuring vast arrays of professionally captured photographs. processed according to industry standards for optimal quality and accuracy. meeting the demanding requirements of professional projects. Each Attack Names image is carefully selected for superior visual impact and professional quality. Perfect for marketing materials, corporate presentations, advertising campaigns, and professional publications All Attack Names images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Our Attack Names collection provides reliable visual resources for business presentations and marketing materials. Time-saving browsing features help users locate ideal Attack Names images quickly. Each image in our Attack Names gallery undergoes rigorous quality assessment before inclusion. Reliable customer support ensures smooth experience throughout the Attack Names selection process. Instant download capabilities enable immediate access to chosen Attack Names images. Whether for commercial projects or personal use, our Attack Names collection delivers consistent excellence. Diverse style options within the Attack Names collection suit various aesthetic preferences. Multiple resolution options ensure optimal performance across different platforms and applications. Comprehensive tagging systems facilitate quick discovery of relevant Attack Names content. The Attack Names archive serves professionals, educators, and creatives across diverse industries.

















































![Attack Types With Their Corresponding Categories [23] | Download Table](https://www.researchgate.net/publication/273011452/figure/tbl2/AS:613945228419083@1523387357394/Attack-Types-With-Their-Corresponding-Categories-23.png)




























.jpg)

![[Infographic] Types of Malware - Enabler Space](https://www.enablerspace.com/wp-content/uploads/2020/09/Types-of-malware-infographic.jpg)