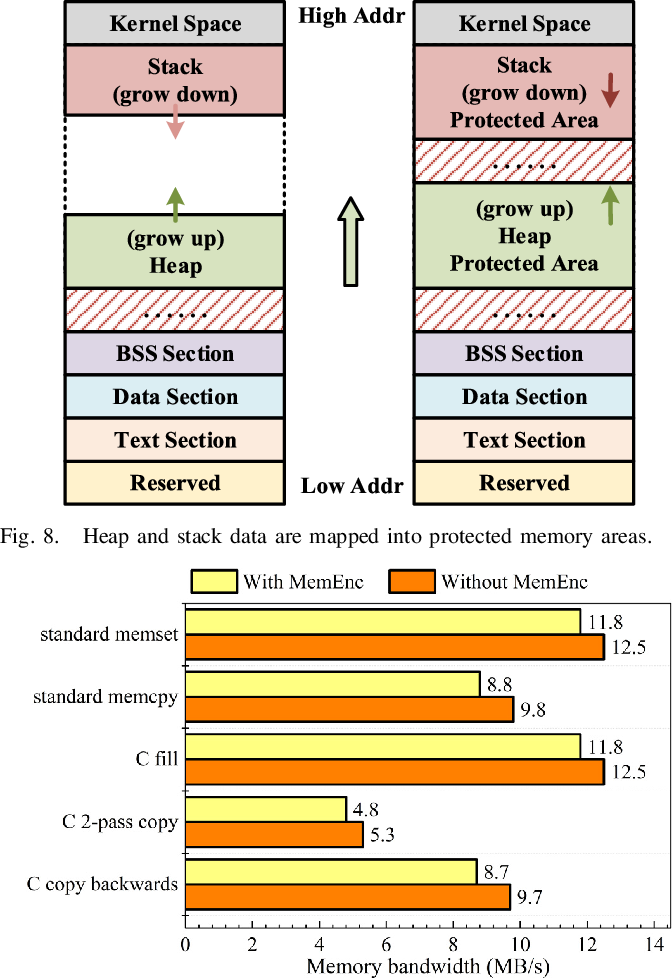
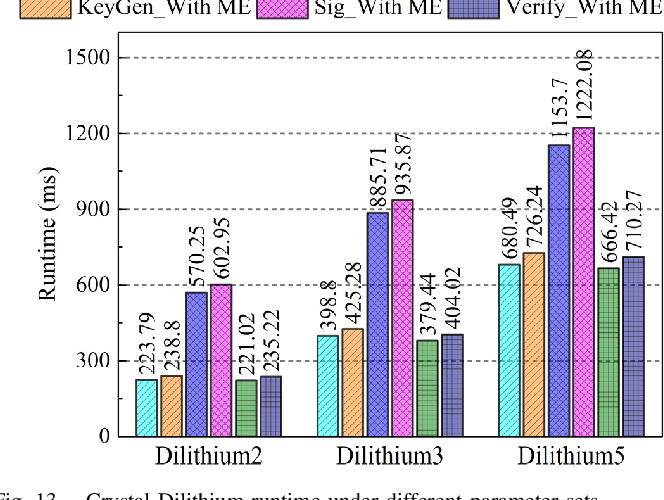
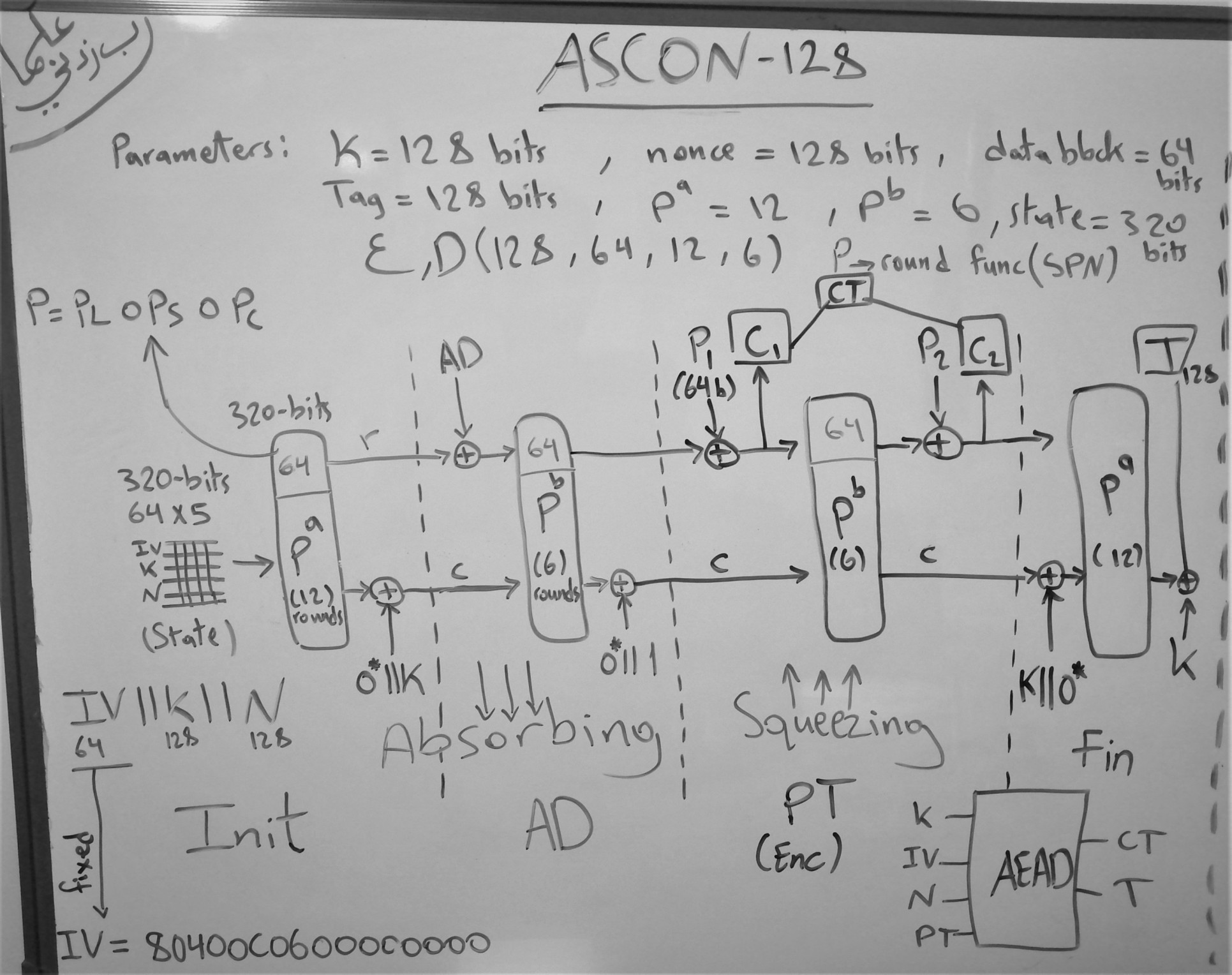
Ascon Cipher Encryption
Discover the vibrancy of city life through hundreds of urban Ascon Cipher Encryption photographs. highlighting the diversity of photography, images, and pictures in urban settings. designed to showcase urban culture and lifestyle. The Ascon Cipher Encryption collection maintains consistent quality standards across all images. Suitable for various applications including web design, social media, personal projects, and digital content creation All Ascon Cipher Encryption images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Our Ascon Cipher Encryption gallery offers diverse visual resources to bring your ideas to life. Instant download capabilities enable immediate access to chosen Ascon Cipher Encryption images. Diverse style options within the Ascon Cipher Encryption collection suit various aesthetic preferences. Regular updates keep the Ascon Cipher Encryption collection current with contemporary trends and styles. Comprehensive tagging systems facilitate quick discovery of relevant Ascon Cipher Encryption content. Advanced search capabilities make finding the perfect Ascon Cipher Encryption image effortless and efficient. Each image in our Ascon Cipher Encryption gallery undergoes rigorous quality assessment before inclusion. Cost-effective licensing makes professional Ascon Cipher Encryption photography accessible to all budgets. Our Ascon Cipher Encryption database continuously expands with fresh, relevant content from skilled photographers.
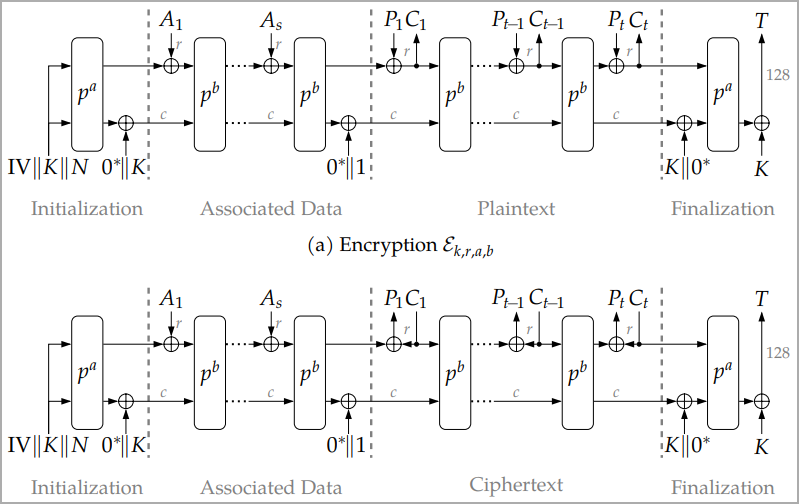
![Ascon authenticated encryption [18] | Download Scientific Diagram](https://www.researchgate.net/publication/356948706/figure/download/fig1/AS:1099665424547840@1639192076668/Ascon-authenticated-encryption-18.png)





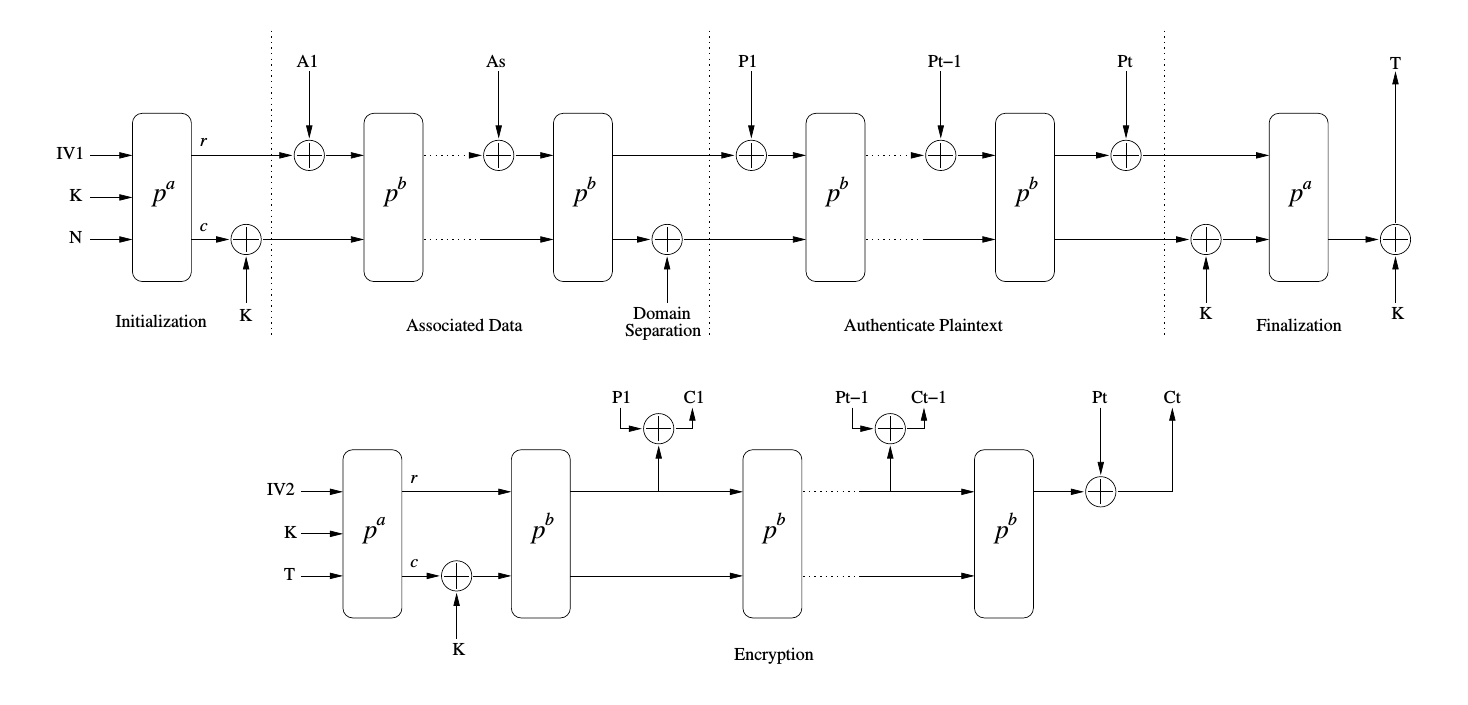
![Ascon Encryption and Decryption Processes [13]. | Download Scientific ...](https://www.researchgate.net/publication/365972743/figure/fig2/AS:11431281104368288@1670029251412/Ascon-Encryption-and-Decryption-Processes-13_Q640.jpg)







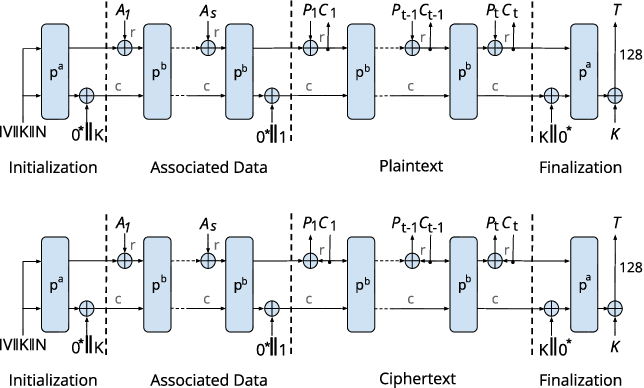
![Ascon authenticated encryption [18] | Download Scientific Diagram](https://www.researchgate.net/publication/356948706/figure/fig1/AS:1099665424547840@1639192076668/Ascon-authenticated-encryption-18_Q640.jpg)









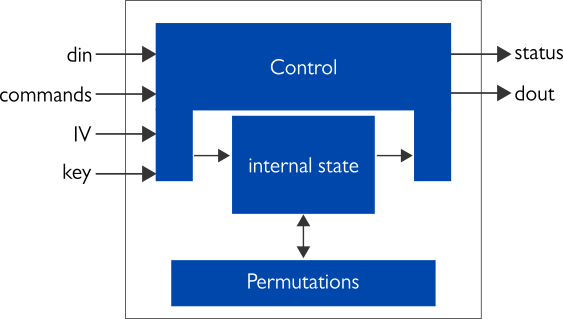
![Ascon-128 Encryption [35]. | Download Scientific Diagram](https://www.researchgate.net/publication/358243540/figure/fig5/AS:1121603580637185@1644422540196/Ascon-128-Encryption-35.png)