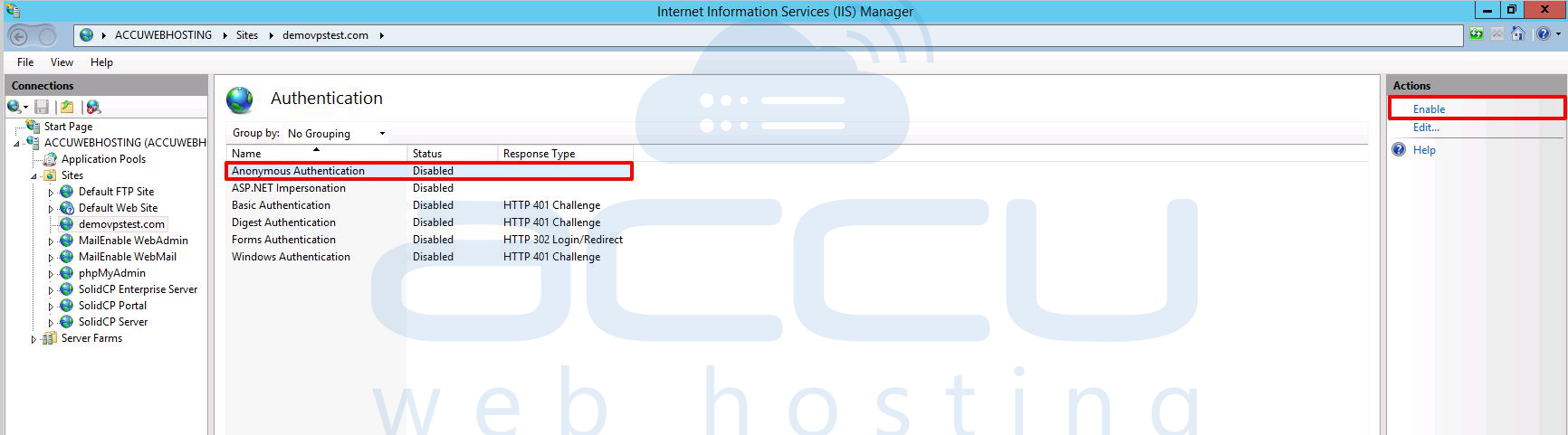
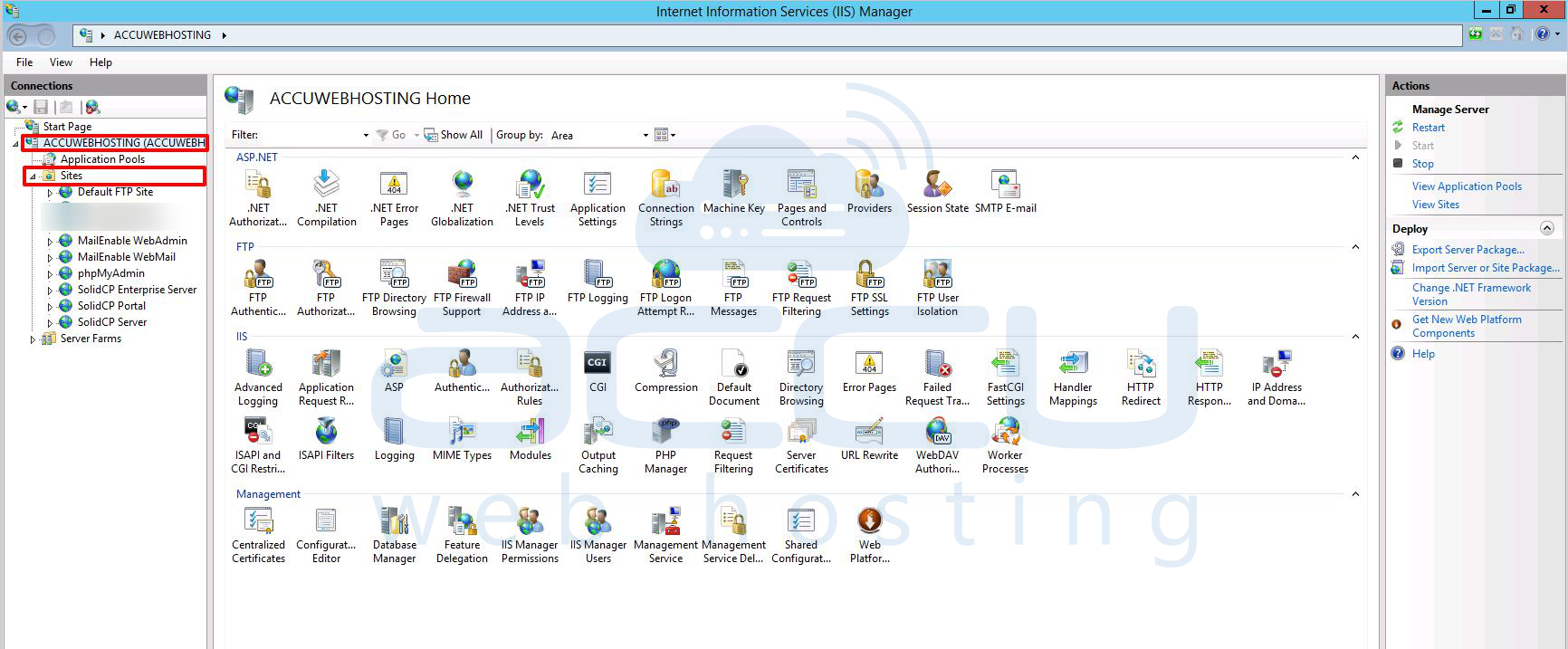
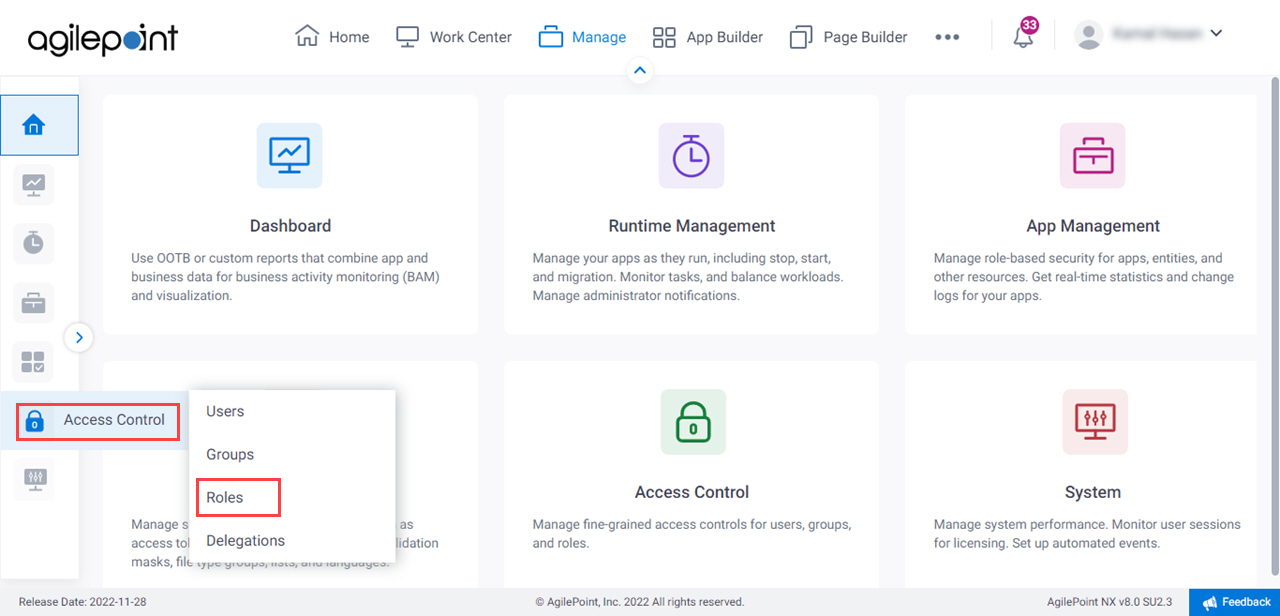
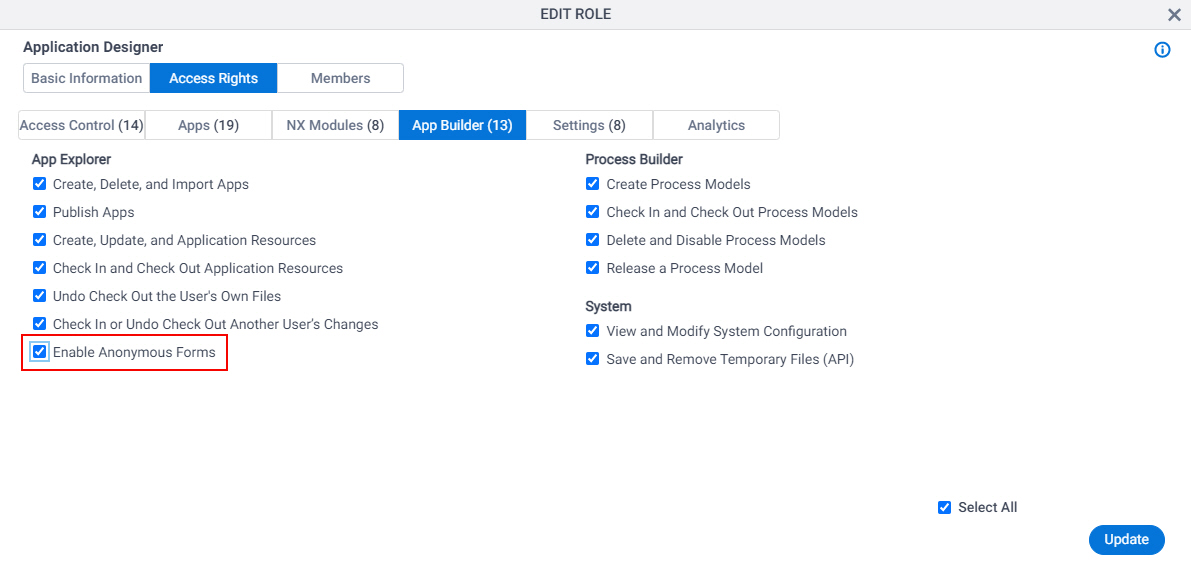
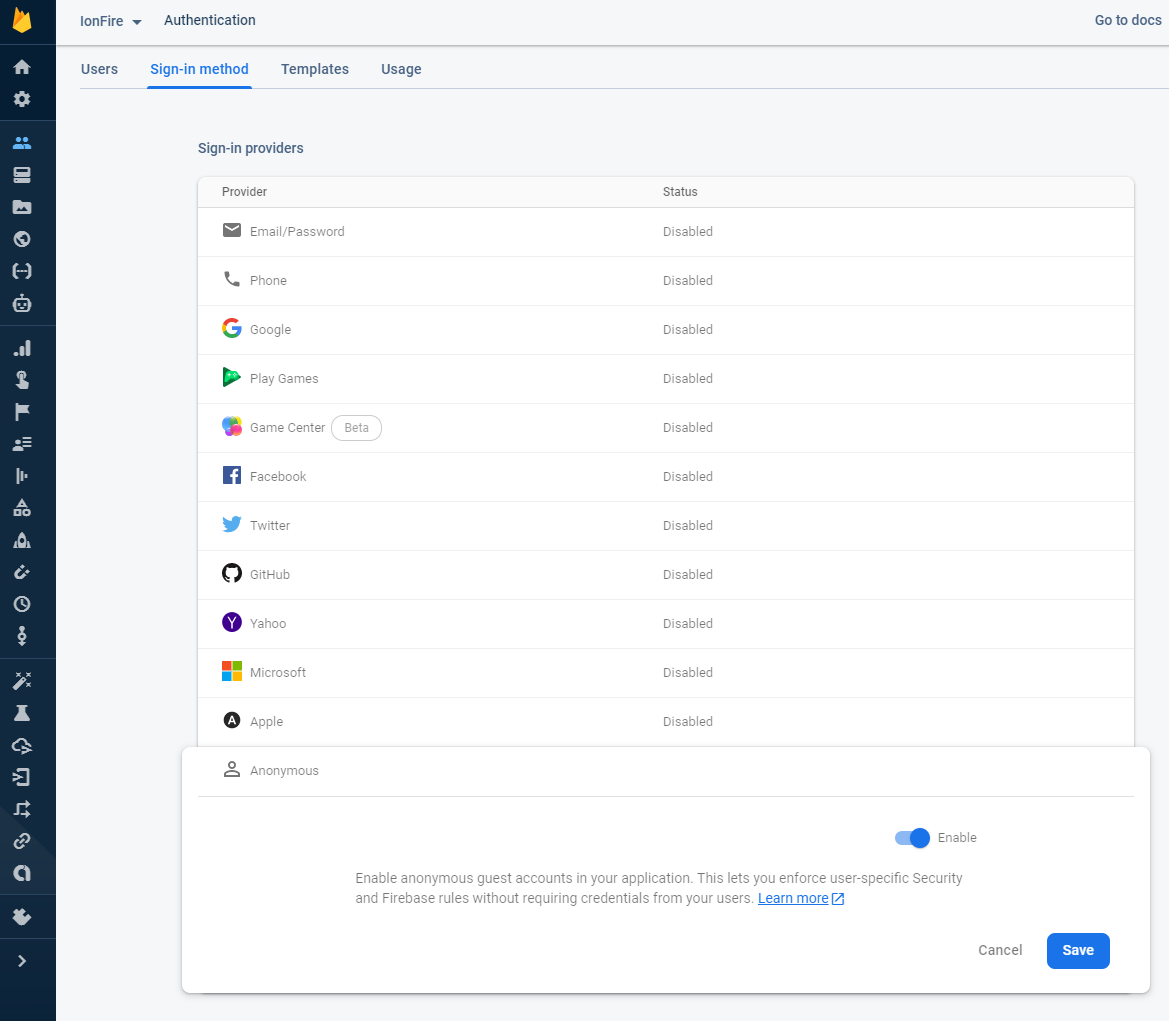
Anonymous Authentication
Celebrate the visual poetry of Anonymous Authentication through countless carefully composed images. where technical excellence meets creative vision and artistic expression. creating lasting impressions through powerful and memorable imagery. Our Anonymous Authentication collection features high-quality images with excellent detail and clarity. Ideal for artistic projects, creative designs, digital art, and innovative visual expressions All Anonymous Authentication images are available in high resolution with professional-grade quality, optimized for both digital and print applications, and include comprehensive metadata for easy organization and usage. Each Anonymous Authentication image offers fresh perspectives that enhance creative projects and visual storytelling. Our Anonymous Authentication database continuously expands with fresh, relevant content from skilled photographers. Time-saving browsing features help users locate ideal Anonymous Authentication images quickly. Multiple resolution options ensure optimal performance across different platforms and applications. The Anonymous Authentication collection represents years of careful curation and professional standards. Regular updates keep the Anonymous Authentication collection current with contemporary trends and styles. Comprehensive tagging systems facilitate quick discovery of relevant Anonymous Authentication content. Instant download capabilities enable immediate access to chosen Anonymous Authentication images. The Anonymous Authentication archive serves professionals, educators, and creatives across diverse industries. Professional licensing options accommodate both commercial and educational usage requirements. Whether for commercial projects or personal use, our Anonymous Authentication collection delivers consistent excellence.






















![The anonymous authentication in scheme [78]. | Download Scientific Diagram](https://www.researchgate.net/profile/Mohammad-Masdari-2/publication/309227950/figure/fig25/AS:418564780642305@1476805028671/The-anonymous-authentication-in-scheme78.png)



































![Anonymous authentication stages [Azees et al. 2017] | Download ...](https://www.researchgate.net/publication/362542089/figure/fig4/AS:1186619344338963@1659923506166/Authentication-protocol-Assar-et-al-2018_Q320.jpg)